Friday afternoon at a typical office in Sydney, Australia. Most of the staff have left to start their weekends when a junior accountant sees an email appear in her inbox. She hesitates for a moment but then she notices that it’s from the company’s CEO.
‘Are you still in the office?’ the message reads. ‘Sorry to keep you back on a Friday night, but this is urgent: I need you to make a wire transfer for me immediately in the amount of $45,000 to my broker in London. Please email me back and confirm when you have completed the transaction. See attached screenshot for details. Thanks.’
Below the brief message, the signature line reads ‘sent from my iPhone.’
The attached screenshot shows a wire transfer account and routing number.
Emails like the one described above are landing in corporate inboxes every day. This kind of cybercrime is known as ‘CEO fraud’ and it’s become very profitable for scammers.
CEO fraud attacks leverage impersonation of high-ranking executives to extract money from companies.
The cybercriminals who perpetrate this kind of fraud collect information about CEOs or hack into their email accounts so they can impersonate them. Once they have enough information to assume a CEO’s identity the scammers will use their authority to persuade another person in the company to send them money.
You might not think trickery like this could work, but the statistics on CEO fraud are alarming. According to the FBI, these kind of attacks have increased by 2,370% since 2015 and the global cost is now in the billions of dollars.
Low-tech cybercrime
People tend to think of cybercrime as being high-tech, but CEO fraud requires only very simple tools. Unlike ransom-attacks or spyware, CEO fraud doesn’t rely on clever software to be effective; it’s a kind of cybercrime known as ‘social engineering’ that uses psychological cues and deception to defraud victims.
In CEO fraud, instead of hacking code the scammers hack social networks, relationships and company structures.
All a criminal needs is the email address or phone number of a high ranking person inside a company and they can begin to construct a scheme.
Typically, scammers will create an email account that closely resembles the address of the person they want to impersonate. If the real email address is ceo@example.com they will register something like ceo@examp1e.com - with a 1 instead of an l - which looks close enough to go unnoticed.
In the example at the beginning of this post the fraudulent message showed the signature line ‘sent from my iPhone.’
The technique of sending a message that appears to be from a phone is commonly used in CEO fraud because it avoids the need to include company logos in messages.
In addition to impersonating a person with authority in a company, fraudsters usually try to create a sense of urgency with their messages. Timing a message to arrive near close-of-business, and urging staff to act quickly are ways to discourage them from checking the authenticity of a message before acting on it.
One email is all it takes
In a recent high profile CEO fraud case, businessman John Kahlbetzer lost $1 million in a single incident.
Kahlbetzer’s assistant got an email that appeared to be from her boss, instructing her to make a $1 million transfer to a UK bank account. Apparently, it was not unusual for the millionaire to email such instructions to his assistant, so she immediately completed the transaction.
Unfortunately, the email had not been sent by Kahlbetzer at all. The email address of the sender was very similar to Kahlbetzer’s - only one character different - so his assistant simply didn’t notice it was fake. She transferred the funds and by the time she realised her mistake, the money had been moved to multiple offshore bank accounts.
A fast-growing problem
Cybercrime is a booming industry. Recent research by the World Economic Forum (WEF) found that cybercrime attacks on businesses almost doubled in the five years to 2017; from 68 to 130 incidents per company.
The WEF’s research found that the growth in cybercrime is driven not only by the potential for big rewards but also by expanded opportunity. Business is increasingly conducted online but people’s security awareness is lagging behind the adoption of online systems.
FBI cybercrime data shows that the financial damage from email scams has grown especially fast; industry experts place the projected cost in excess of US$9 billion dollars globally during 2018.
Human beings are the weakest link in corporate security because unlike machines they are susceptible to psychological trickery and social pressure.
The skill required to infiltrate a company via hacking is considerable, but cybercriminals have learned that they can steal from companies much more easily by impersonating their executives.
All a scammer needs to commit CEO fraud is a phone and a little imagination.
For criminals, CEO fraud is an irresistible opportunity; minimal investment with high ROI.
Get the facts
You can download MailGuard’s executive guide to CEO fraud for free.
In this easy to read document you’ll learn about:
- How to protect your organisation
- Why CEO fraud is a whole-of-business risk
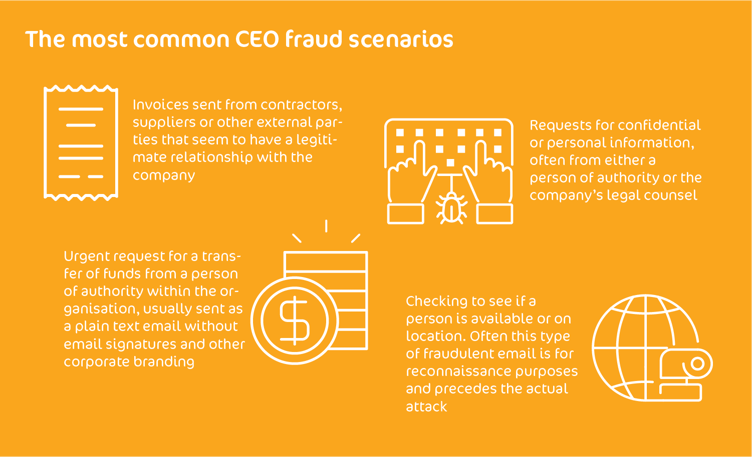
- Common fraud scenarios used by cybercriminals
- Ideal policy frameworks for combating CEO fraud
Download your copy, here.







