In the past 24 hours a second wave of Telstra and Google email scams have hit email inboxes across Australia.
MailGuard is blocking a number of high volume phishing scams that are targeting thousands of users at a time. These new variant, zero-day threats are designed to bypass traditional AV. It is common for cybercrime networks to iterate on attacks like these, to avoid detection and maximise their gains.
The current wave of scams is again leveraging household brands. In the case of the Telstra scam, now offering a bill refund to Telstra customers, and the new Google Drive scam is similar to many that we have seen in the past, this time with a new URL to the phishing landing page.
Below are screen shots of the new wave of scams that you can share with your teams. If you would like to stay up to date these fast-breaking attacks, you can also subscribe to our RSS feed here. Or add the MailGuard RSS feed to your RSS reader. Many businesses are even integrating our feed into their Intranet to make sure their staff are constantly alert to new threats.
A sample of the new wave of Telstra scam emails circulating today:
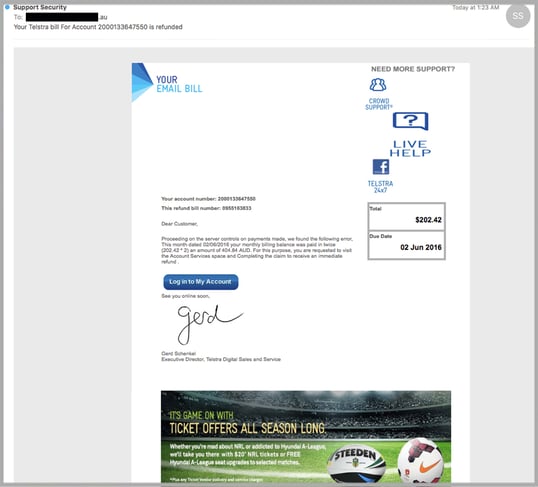
This email scam is similar to yesterday’s Telstra scam email, using the same email signature and reference to legitimate Telstra staff, but this time offering a ‘reward’ to the email recipient by suggesting they are entitled to a refund.
The cyber criminals behind the attack are forging "@online.telstra.com" - which is the same email domain that Telstra uses to send out legitimate phone bills. Also, online.telstra.com does not have an SPF record, which would help anti-virus vendors stop the emails when they are forged.
By clicking the ‘Log into My account’ link contained within the email, recipients are directed to a webmail phishing page and not a fake Telstra phishing page. The website may have been pulled down by the owner of the site that was originally compromised. This landing page should be a dead giveaway for the email recipients.
The second scam impersonates Google Drive. Although we have seen many of these fake Google scams in the past, please note the URL to the fake landing page is different to the last and is the main tactic cyber criminals are using to bypass security.
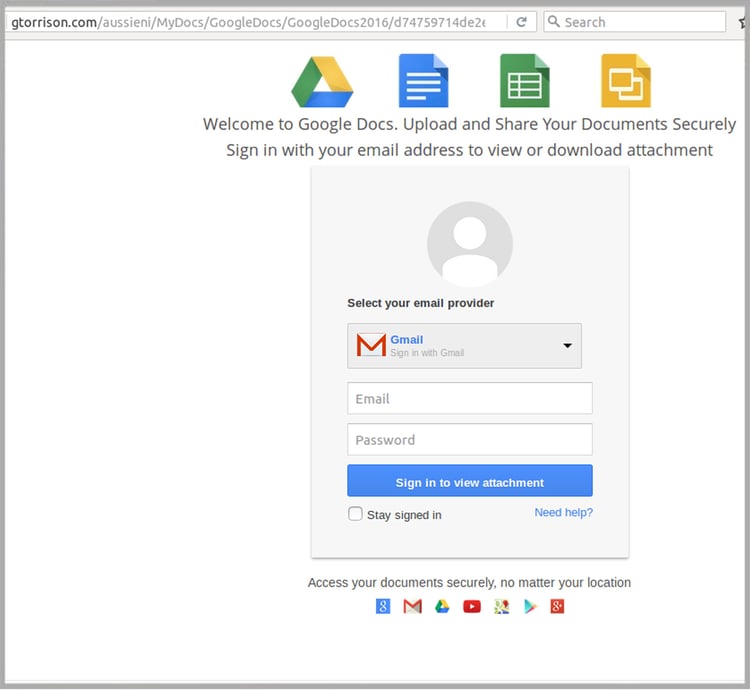
This is a standard phishing email looking for access to Google Drive accounts. Cyber criminals will of course have access to any files and information stored on these online accounts once login credentials are divulged.
How to recognise phishing emails
You can reduce the likelihood of being impacted by phishing emails like this Google scam by being wary of content which asks you to view documents out of the blue, especially where the user doesn’t explain their purpose or subject.
Make sure you study the URL in the landing page – in this case it bears no relation to Google, so is clearly a scam.
Also be on the lookout for other tell-tale signs of phishing scams, especially where the sender allows you to do things not normally allowed – for example being able to log-in using details from multiple email providers – a typical approach used to widen their phishing net.
You can stop phishing emails from getting into your inbox in the first place by implementing cloud-based email filtering technology, which will successfully protect your business from damage.
While the majority of other security providers are still yet to block this Google phishing scam, MailGuard’s cloud technology successfully blocked it immediately, in real-time.
If you’re experiencing problems, you can speak to a cloud security specialist on 1300 30 44 30 or email expert@mailguard.com.au
Keep up to date on the latest email scams by subscribing to MailGuard’s weekly update or follow us on social media.







