Think twice before opening any attachments purporting to be from Westpac. The established bank has been brandjacked by cybercriminals attempting to steal confidential data from users.
MailGuard intercepted emails purporting to be from Westpac on Sunday afternoon AEST. The emails use a display name of "Security Live Westpac Agent No.093971" and several other variants on this.
It was found that the emails actually come from one of a large number of compromised email accounts. The majority of these accounts are from a domain with a TLD (Top Level Domain) of .JP (Japanese domains).
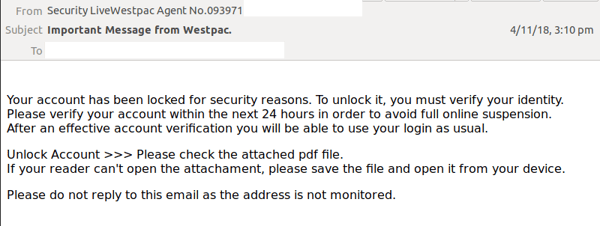
The email advises recipients that their account has been locked for security reasons. To unlock their account, they must verify their identity within 24 hours or else face ‘full online suspension’. Instructions to do this are attached in a PDF which includes the logo and branding of Westpac bank.
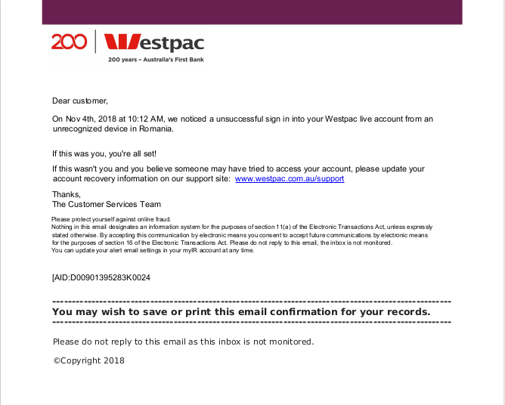
Titled ‘4Nov_WSP_Notif_93423876.pdf’, the abovementioned PDF informs recipients about an unsuccessful login attempt. It adds that if users initiated the unsuccessful login attempt, then they do not need to worry. However, if the attempt was not them, they should update their account recovery information on the Westpac support site.
The PDF encourages users to click on a link if they wish to recover their accounts via the support site.
Unsuspecting users who click on the link are led to a site that is offline (currently provides a 404 response). The site is suspected to have hosted a Westpac branded phishing page.
This attempt preys on Westpac users, and leverages on the well-established reputation of the bank to convince users into thinking the email notification is a legitimate one.
Phishing preys on the weakest link in the IT security chain – users. Tricking someone into handing over their password is far simpler than breaking into a bolstered system. As a result, hackers use tactics such as brandjacking to manipulate users and obtain sensitive data.
How to prevent phishing:
- Delete emails that are impersonal or not addressed to you by name.
- Be wary of communication from senders you were not expecting to hear from.
- Mouse over the link to see where it will take you before you click it. Pay close attention to the URL the purported sender uses. If it takes you somewhere you don't recognise, then it's something to treat as suspicious.
Whilst this attempt isn’t as sophisticated as many other examples we have seen, it will still fool less vigilant recipients into entering their login credentials. It is important to identify any oddities in URLs and immediately exit any webpages that do not match that of the official sender.
Educating staff and employing cloud-based email and web filtering is your first and best line of defence. Compliment this multilayered defence with on premise antivirus, anti-malware and anti-spyware solutions. This will go a long way to mitigating the risk from a wide range of email scams.
For a few dollars per staff member per month, add MailGuard's cloud-based email and web filtering solution to your business security. You’ll significantly reduce the risk of new variants of malicious email from entering your network. Talk to an expert at MailGuard today about your company's cybersecurity needs: expert@mailguard.com.au
Keep up to date on the latest email scams by subscribing to MailGuard’s weekly update, or follow us on Twitter @MailGuard.







