Cybercriminals have brandjacked ANZ and are circulating fraudulent emails purporting to be from the bank in a bid to steal users’ confidential data.
The email is sent from an anz.com.au address, with a display name of ‘ANZ Bnak’. The misspelling of the display name can be due to a mistake on the cybercriminals' end or more likely, an attempt to bypass checks looking for the correct spelling.
MailGuard has detected that cybercriminals are forging the anz.com.au domain, which results in an SPF record soft fail. This SPF soft fail result indicates that the emails are not from a server that anz.com.au lists as a legitimate source. However, the recipients' mail server may choose to not enforce this as the anz.com.au domain is set to soft fail rather than hard fail.
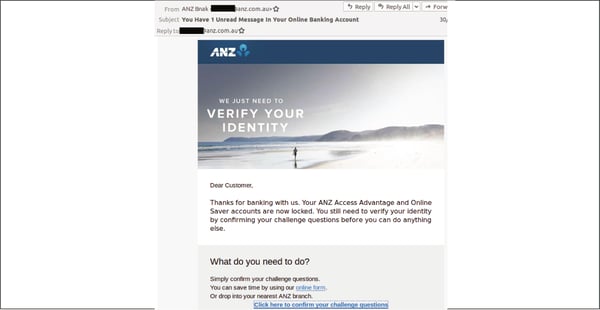
A link is provided in the email for users to confirm their identity by completing a series of ‘challenge questions.’
Recipients who click on the link are led to an ANZ branded phishing page. This page tricks users into revealing their bank account credentials. The phishing page has since been taken down.
This attack is particularly malicious because of the multiple strategies it has adopted to appear as a legitimate notification from ANZ Bank.
Aside from replicating the bank’s branding, the scam utilises challenge questions to scam users into handing over sensitive credentials. These are, ironically, renowned safety features universally adopted by many organisations to prevent data theft in the first place.
By including such safety features, this scam convinces users that it is a genuine alert from ANZ – one which is, as usual, taking all the necessary precautions that are normally expected from a large and reputable bank.
Having convinced recipients that the email is actually from ANZ, cybercriminals exploit the trusted reputation of the brand to trick customers into divulging their confidential data via the phishing page.
What is "phishing?"
Phishing is the practice of tricking email recipients into revealing personal information that criminals can exploit for gain.
Phishing emails go to a wide group of random people; it’s like a fisherman casting a wide net to see what he can catch. The attackers know that not everyone will respond, but they know that if they send enough emails out somebody will probably take the bait.
A phishing attack message will typically include a link that will send the unwary victim to a fake login website. Once there, the user will be asked to enter username and password data which will be automatically captured by the phishing page.
Scammers use phishing pages to collect login credentials for email accounts, bank accounts, and a wide range of other online services.
Protect your business online
Phishing scams and website hijacking can make millions of dollars for criminals. The big rewards for cybercrime have driven explosive growth in phishing in recent years, but many businesses are still poorly prepared to counter such attacks.
If you would like to learn more about cybersecurity and how to protect your business, please download the e-book Surviving the Rise of Cybercrime. It’s a plain English guide explaining the most common threats and providing essential advice on managing risk.
For a few dollars per staff member per month, add MailGuard's cloud-based email and web filtering solution to your business security. You’ll significantly reduce the risk of new variants of malicious email from entering your network. Talk to an expert at MailGuard today about your company's cybersecurity needs: expert@mailguard.com.au
Keep up to date on the latest email scams by subscribing to MailGuard’s weekly update, or follow us on Twitter @MailGuard.







