Cybercriminals have once again exploited Westpac Bank’s trademarks in a phishing email scam.
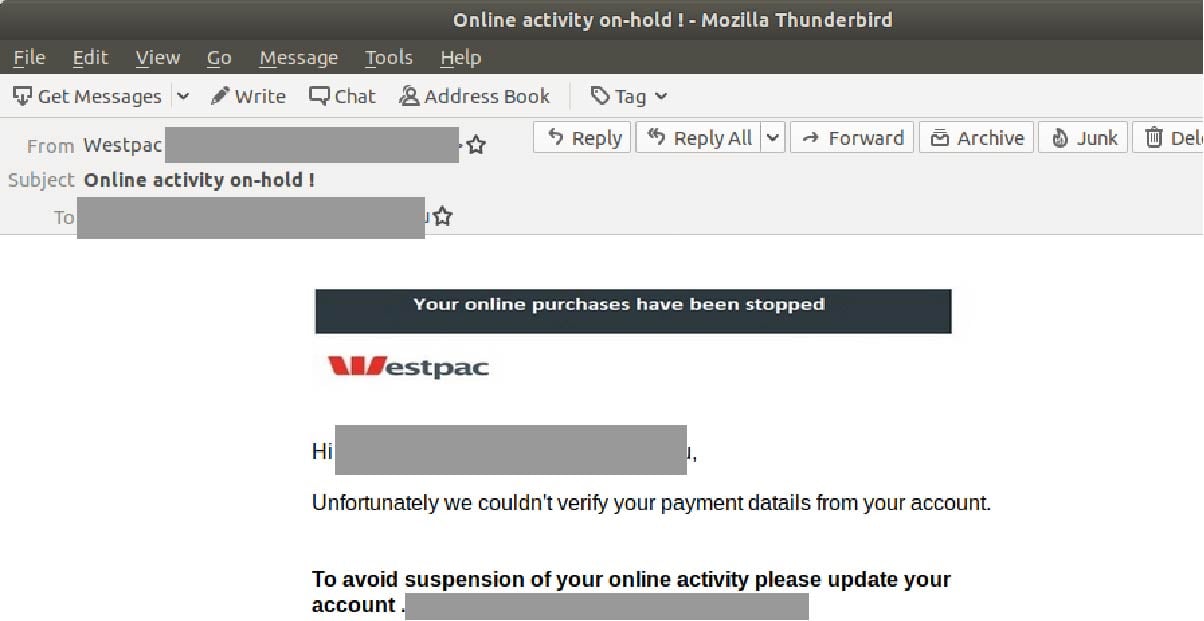
The emails are titled ‘Online activity on-hold !”, and are infiltrating inboxes using the display name ‘Westpac’. The email address used next to the display name uses a domain not belonging to Westpac.
The email includes Westpac’s logo and a header titled “Your online purchases have been stopped”. It informs you that your payment details could not be verified from your account. To resolve this problem and to “avoid suspension of your online activity”, users are directed to update their account via a link.
Here is what the email looks like:
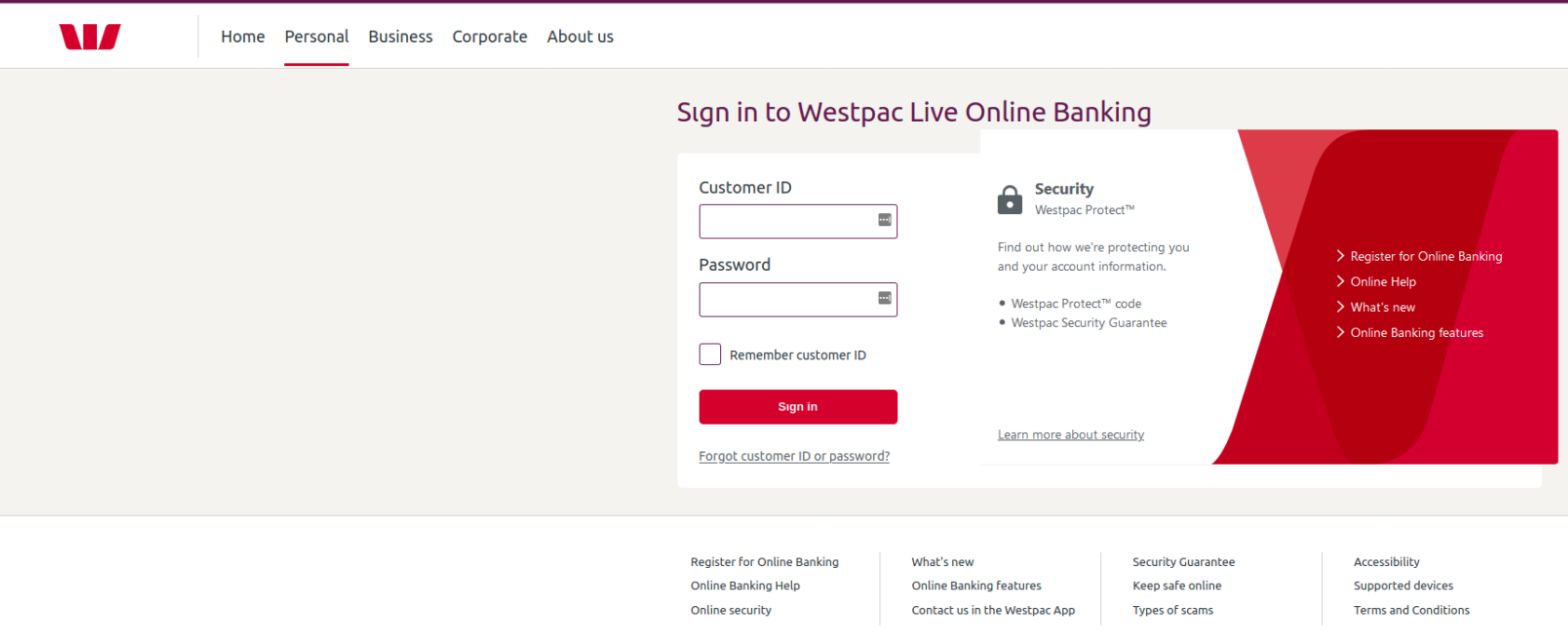
Unsuspecting recipients who click on the link are led to a fake Westpac-branded login page asking for their Customer ID and password. Interestingly, this page is hosted on a domain not belonging to Westpac:

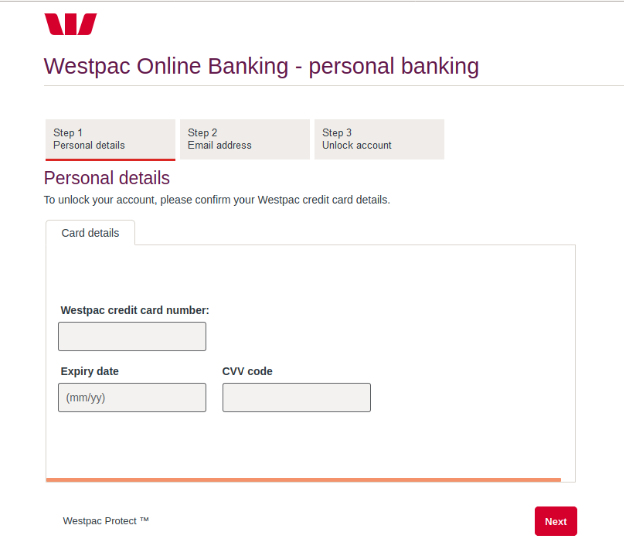
Upon “signing in”, users are led to another similiarly-crafted page asking them to follow 3 steps in order to unlock their account. In the first step, they are asked for their credit card details:
After inserting their details and clicking “Next”, users are led to step 2. This step asks users to insert their email address and password, as per the below:
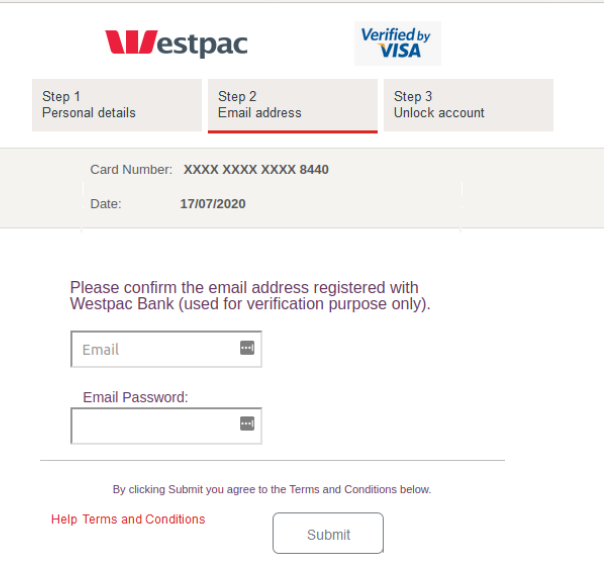
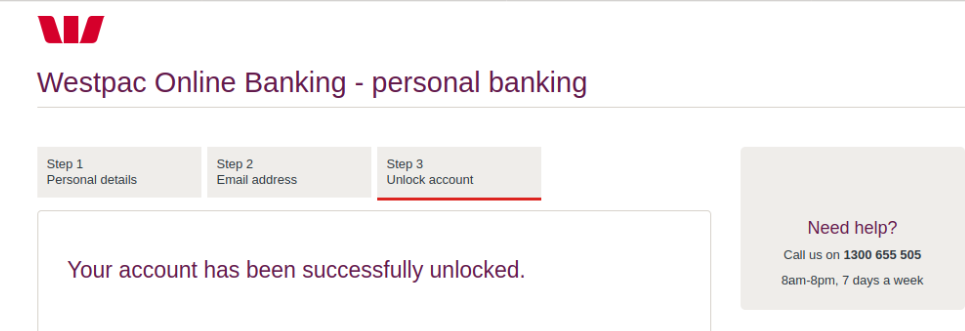
The third step, titled “unlock account” is a confirmation page telling users their account has been successfully unlocked. They are then redirected to the actual Westpac login page.
This sole purpose of this elaborate phishing scam is to harvest the login credentials of Westpac customers so the criminals behind this scam can break into their bank accounts.
By typing in your account number and password, you’re handing this sensitive account information to cybercriminals and enabling them to commit identity theft.
The hallmark of this scam lies in how authentic it looks. Cybercriminals have employed multiple techniques to boost its credibility. For instance, all of the phishing pages feature high quality branding elements such as WestPac’s logo & layout.
Furthermore, cybercriminals behind this scam have incorporated several techniques within the email itself to boost its credibility. These include:
- The inclusion of a display name like “Westpac”, implying the email has been sent from a credible source belonging to the bank and,
- An alarming subject line; informing recipients that their “online activity” is on hold creates a sense of urgency and anxiety. The email body also threatens users that their account will be suspended if they don’t update their account by clicking on the provided link. This motivates users to take action immediately without checking on the email’s authenticity.
Combined, all these techniques motivate the users to proceed forward in ‘reactivating’ their account.
Despite these techniques however, several tell-tale signs are present in this email that point to its illegitimacy. These included several spelling mistakes within the email body (e.g. “your payment datails”) and the fact that the Westpac branded pages don’t use a domain belonging to the bank.
As a precaution, we urge you not to click links within emails that:
- Are not addressed to you by name.
- Appear to be from a legitimate company but use poor English, or omit personal details that a legitimate sender would include.
- Are from businesses that you were not expecting to hear from.
- Take you to a landing page or website that is not the legitimate URL of the company the email is purporting to be sent from. The URL for Westpac’s internet banking login page is: https://online.westpac.com.au
Westpac offers a comprehensive online resource to help identify and report scams purporting to be from them. You can verify the authenticity of any contact you aren’t sure about, or report a scam, by calling 132 032 or emailing them at hoax@westpac.com.au.
Phishing preys on the weakest link in the IT security chain – users. Tricking someone into handing over their password is far simpler than breaking into a bolstered system. As a result, hackers use tactics such as brandjacking to manipulate users and obtain sensitive data.
Whilst MailGuard is stopping this email scam from reaching Australian businesses, we encourage all users to be extra vigilant against this kind of email and whatever happens, do not open or click them.
Don't get scammed
If your company’s email accounts aren’t protected, emails like the one above are almost certainly being received by your staff. Cybercriminals know people can be tricked; that’s why they send out millions of scam messages and put so much effort into making them look convincing.
People are not machines; we're all capable of making bad judgement calls. Without email filtering protecting your business, it’s just a matter of time before someone in your organisation has a momentary lapse of judgement and clicks on the wrong thing.
One email is all that it takes
All that it takes to break into your business is a cleverly-worded email message. If scammers can trick one person in your company into clicking on a malicious link they can gain access to your data.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive and advanced email security.
Talk to a solution consultant at MailGuard today about securing your company's network.
Why not stay up-to-date with MailGuard's latest blog posts by subscribing to free updates? Subscribe to weekly updates by clicking on the button below.







