A new phishing email scam intercepted by MailGuard is a good reminder of the importance of exercising caution before clicking on links within an email – even if it appears to be sent from a legitimate sender.
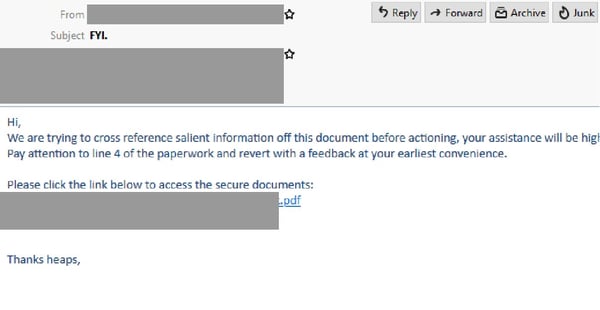
Titled “FYI”, the email appears to be sent from a compromised email account belonging to a Finance Worker working in an Australian organisation. The email claims it is ‘trying to cross reference salient information’ and asks recipients to view the attached paperwork and ‘revert with a feedback’. A link is provided for the recipients ‘to access the secure documents’.
Here’s what the email looks like:
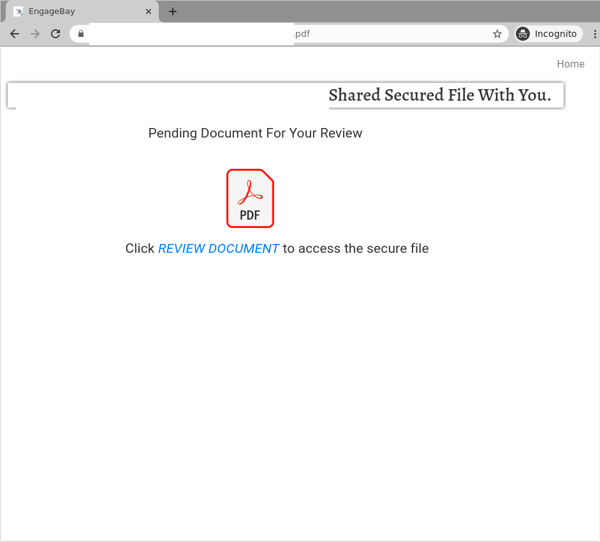
Clicking on the link leads recipients to a webpage that appears to be a document sharing site. Just like in the email, users are informed there is a ‘pending document’ for their review and are asked to view a ‘secure file’. The Adobe PDF logo is included in this page, as per the below:
Clicking on the link to ‘review document’ leads users to a login page that employs branding elements belonging to both Dropbox and Microsoft Office 365. Users are asked to sign in with their email provider, either Office 365 or any other email service. Here are screenshots of this page:
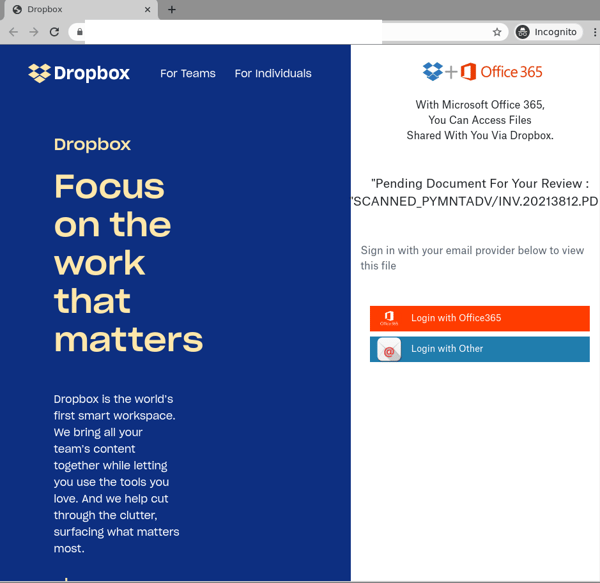
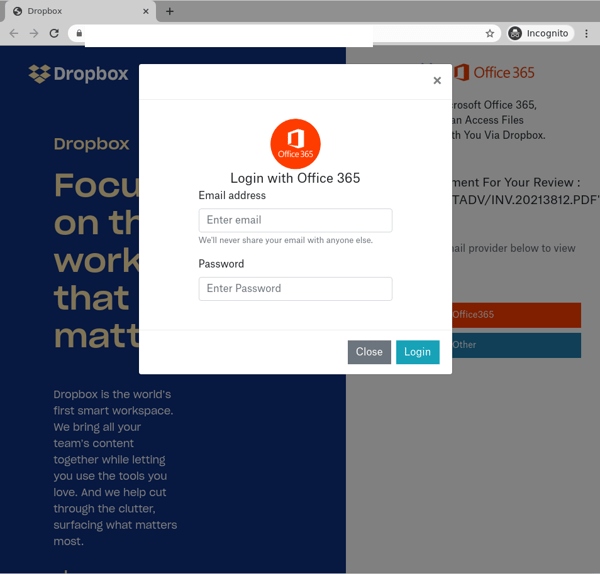
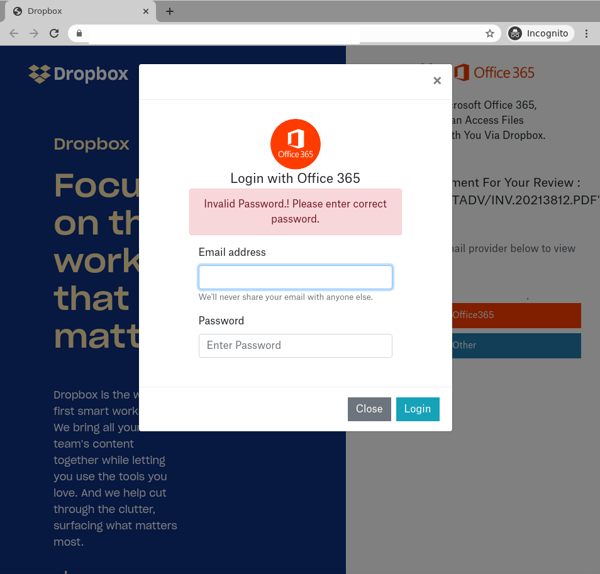
Interestingly, the domain used in the URL of this page doesn’t belong to Dropbox, nor to Microsoft Office 365. This is actually a phishing page that appears to be a compromised website hosted on GoDaddy. Once users ‘sign in’, their credentials are harvested for later use by attackers, and they are met with an error saying that the credentials are invalid, as per the below:
Whilst MailGuard is stopping this email scam from reaching Australian businesses, we encourage all users to be extra vigilant against this kind of email and whatever happens, do not open or click them.
Scams like these have a high likelihood of successfully tricking users, especially in the current climate. With workforces becoming more remote in light of COVID-19, it is common for employees to email confidential business documents to one another. Therefore, notifications like the above aren't likely to raise any alarm bells when they appear in an inbox, motivating users to click on the provided links. without a second thought.
The use of well-known brand names, like popular cloud file-sharing platform Dropbox, along with Microsoft and Adobe also serves to inspire false trust, boosting the email’s credibility. Cybercriminals frequently exploit the branding of global companies like these in their scams, because their good reputation lulls victims into a false sense of security, and with such a large number of users they are an easy and attractive target. Their established brands help convince recipients that the files being shared via this email are secure.
In addition, scams that are initiated from compromised accounts like the one above are particularly dangerous, for a number of reasons:
- The emails are sent from a legitimate account, so they are not likely to be blocked by email security services,
- The recipients are more receptive to the emails, especially where the sender is known to them, and
- Because they may deliver a malicious payload, or simply a .PDF file like in the above example, and may direct users to external phishing pages to harvest credentials.
In such cases, users are reminded of the importance of not accepting/clicking on documents from unknown senders, despite the organisation they purport to be from. All attachments/links should only be accessed when users are certain about the credibility of their owners.
Despite these techniques, recipients of this email would be able to spot several red flags that point to the email’s in-authenticity. These include the fact that the email doesn’t address the recipient directly, and that the domains used in the phishing page don’t belong to Adobe, Microsoft or Dropbox.
We encourage all users to exercise caution when opening messages like these, and to be extra vigilant against this kind of cyber-attack. If you are not expecting a file from the sender, do not open the email, download files or click through on the links. Check with the sender first, even if they are known to you.
As a precaution, MailGuard urges you not to click links within emails that:
- Are not addressed to you by name.
- Appear to be from a legitimate company but use poor English, or omit personal details that a legitimate sender would include.
- Are from businesses that you were not expecting to hear from.
- Take you to a landing page or website that is not the legitimate URL of the company the email is purporting to be sent from.
One email is all that it takes
All that it takes to break into your business is a cleverly-worded email message. If scammers can trick one person in your company into clicking on a malicious link they can gain access to your data.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive and advanced email security.
Talk to a solution consultant at MailGuard today about securing your company's network.
Why not stay up-to-date with MailGuard's latest blog posts by subscribing to free updates? Subscribe to weekly updates by clicking on the button below.







