MailGuard has intercepted a phishing email scam masquerading as a file-sharing notification in order to trick users.
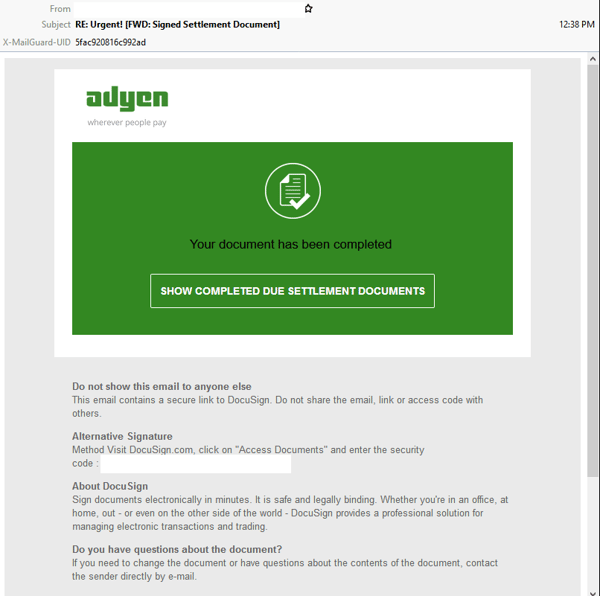
The email uses a subject line beginning with “Urgent!” and claims to share a “Signed Settlement Document”. The email appears to be one generated from DocuSign, informing recipients that their document “has been completed” and includes a detailed footer containing information related to DocuSign documents. However, the email also employs the logo and branding elements of Adyen, a payment processing company. It actually originates from a compromised account.
Here’s what the email looks like:
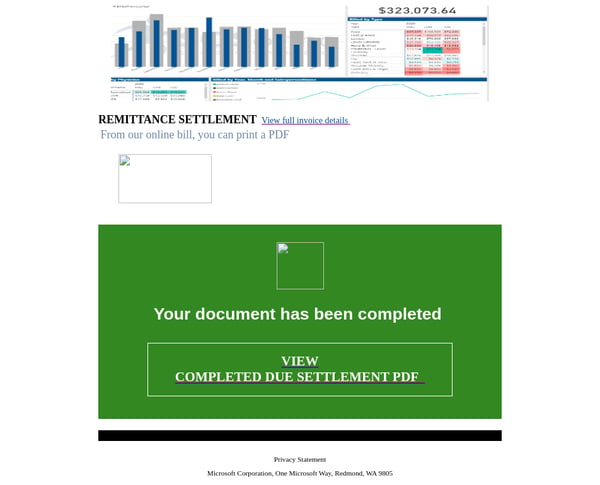
The email also includes an HTML attachment, as per below:
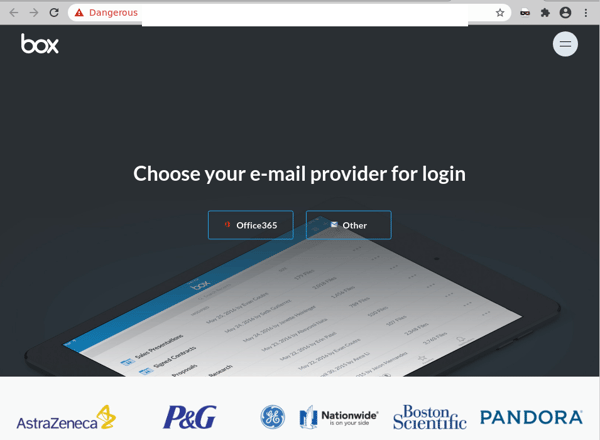
Unsuspecting recipients who click on the link of the email are led to a fake login page employing the logo & branding elements belonging to Box, a cloud content management and file sharing service for businesses. The bottom of the page also includes logos of several other companies, including P&G, Pandora and others. However, the domain used in this page’s URL doesn’t belong to Box, or any of these companies. Instead, the page is actually hosted on a compromised website. It directs users to sign in to either their Office 365, or any other email account. Here’s what the page looks like:
Clicking on either email provider leads users to another phishing page designed to harvest users' email addresses and passwords. Here is a screenshot of the page that users are led to when they click on the “Office 365” button:
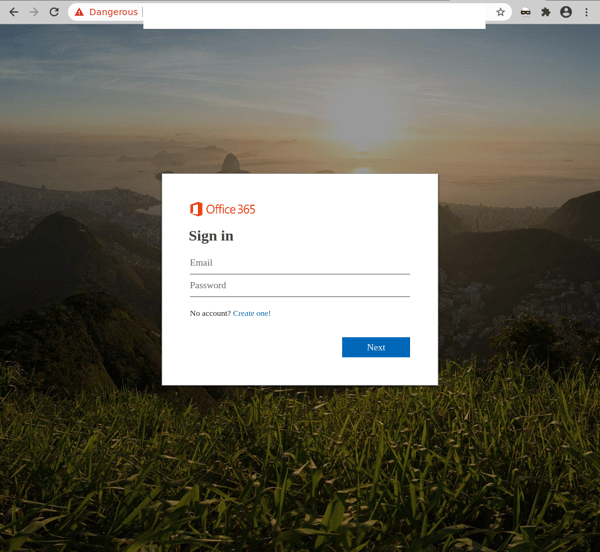
Once users “log into” their accounts by entering their email address and password, the attacker harvests the credentials for later use, and the user is redirected back to the login page.
We advise all recipients to delete these emails immediately without clicking on any links. Please share this alert with your social media network to help us spread the word around this email scam.
Multiple techniques are employed in this scam to boost the email's credibility, including the fact that several well-known brands are impersonated in both the email and phishing pages. For example, both DocuSign and Box are cloud file-sharing services widely used by businesses, so receiving an email containing a new document from either of them isn't likely to raise too many red flags. Their good reputation and familiarity makes them an attractive target among scammers, and since their service requires users to click a link to download files, they are a convenient trojan horse for malicious attacks. In addition, receiving documents from payment processing companies like Adyen in business inboxes is also a common practice. Cybercriminals know this, and hope that in their rush to view sensitive documents related to payments, users won’t pause to check the legitimacy of the email.
Besides the above, this particular scam also uses a subject line that is designed to evoke alarm and panic among recipients who, thinking there actually is an “urgent” document for them to view, may be motivated to click on the link provided without thinking twice. Plus, scams that are initiated from compromised accounts (like in this case) are particularly dangerous because the emails are sent from a legitimate account, so they are not likely to be blocked by email security services. Cybercriminals often exploit these rules to trick users.
Several red flags are, however, present in this email scam that should alert users. These include the fact that the email doesn’t address the recipient directly, and that the domain used in the URL of the phishing page belongs to a third party.
In such cases, users are reminded of the importance of not accepting/clicking on documents from unknown senders, despite the organisation they purport to be from. All attachments/links should only be accessed when users are certain about the credibility of their owners.
DocuSign lists the following advice on its incident reporting page:
“If you think that you’ve received a fraudulent email purporting to come from DocuSign, forward the entire email as an attachment to spam@docusign.com and delete it immediately.”
As a precaution, MailGuard urges you not to click links within emails that:
- Are not addressed to you by name.
- Appear to be from a legitimate company but use poor English, or omit personal details that a legitimate sender would include.
- Are from businesses that you were not expecting to hear from.
- Take you to a landing page or website that is not the legitimate URL of the company the email is purporting to be sent from.
One email is all that it takes
All that it takes to break into your business is a cleverly-worded email message. If scammers can trick one person in your company into clicking on a malicious link they can gain access to your data.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive and advanced email security.
Talk to a solution consultant at MailGuard today about securing your company's network.
Why not stay up-to-date with MailGuard's latest blog posts by subscribing to free updates? Subscribe to weekly updates by clicking on the button below.







