MailGuard has intercepted a new phishing email that masquerades as an auto-generated notification from the recipient’s mail server, informing them that their password has expired.
Titled “Password Expired”, the email uses a display name of “cPanel”, which is a popular web hosting control panel. However, neither the sender nor the recipient appears to be using cPanel. Instead, the email actually originates from a malicious third party and uses a domain that is likely set up for the express purpose of spamming users.
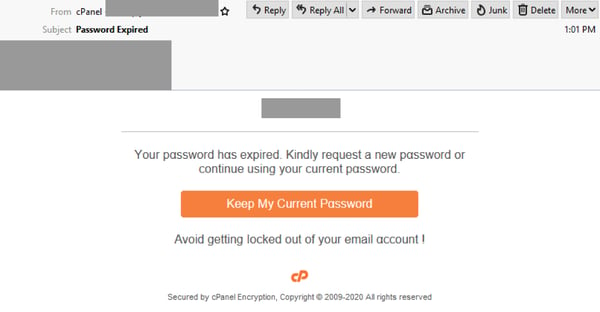
The email’s body begins with a header that indicates it is coming from the recipient’s mail server, and contains the branding & logo of cPanel. It informs users that since their password has expired, they should “kindly request a new password” or continue using their current one. A button is provided for them to keep their current password, and the email ends with a warning for users to “avoid getting locked out” of their email accounts. Ironically, the fraudulent email includes a disclaimer at the bottom, saying it is “Secured by cPanel encryption” – likely an attempt to boost the email’s credibility.
Here's what the email looks like:
Unsuspecting recipients who click on the button are led to a login page asking them for their email username and password, as per the below screenshot. While this page also contains cPanel’s logo, the domain used in the URL of the page doesn’t belong neither to cPanel, nor to the user’s mail server. Instead, it is actually hosted using the Internet Archive (archive.org).
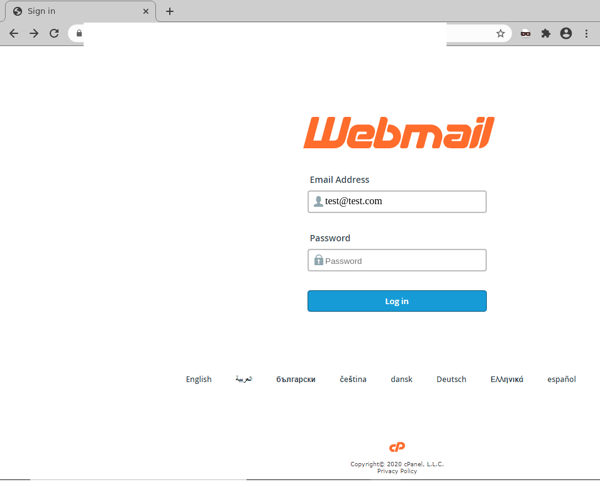
Once users “log in” by entering their credentials, the attacker harvests them for later use, and users are redirected to their domain’s website.
We strongly advise all recipients to delete these emails immediately without clicking on any links. Please share this alert with your social media network to help us spread the word around this email scam.
Here are a few ways how cybercriminals have attempted to make this email look like a legitimate notification:
- usage of cPanel’s logo, with a matching display name suggests the email is sent from a credible source i.e. a well known brand
- inclusion of the recipient’s mail server as an email body header suggests the notification is indeed intended for someone within the recipient’s organisation and,
- the threat of being “locked out” of their email account; this creates a sense of urgency and anxiety, especially among those users who might be working remotely and want to minimise the possibility of any IT issues or complications. This motivates users to take action immediately without checking on the email’s authenticity.
Despite these techniques, eagle-eyed recipients of this email would be able to spot several red flags that point to the email’s in-authenticity. These include the fact that the email doesn’t address the recipient directly, and that it contains spacing errors (e.g. “Avoid getting locked out of your email account !”).
As a precaution, MailGuard urges you not to click links within emails that:
- Are not addressed to you by name.
- Appear to be from a legitimate company but use poor English, or omit personal details that a legitimate sender would include.
- Are from businesses that you were not expecting to hear from.
- Take you to a landing page or website that is not the legitimate URL of the company the email is purporting to be sent from.
One email is all that it takes
All that it takes to break into your business is a cleverly-worded email message. If scammers can trick one person in your company into clicking on a malicious link they can gain access to your data.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive and advanced email security.
Talk to a solution consultant at MailGuard today about securing your company's network.
Why not stay up-to-date with MailGuard's latest blog posts by subscribing to free updates? Subscribe to weekly updates by clicking on the button below.







