New phishing and malware attacks today targeting Office 365, Xero and DropBox users have emphasised a growing trend of brand exploitation.
In the past 24 hours, cybercriminals have tried to impersonate Xero, Office 365 and DropBox in phishing scams detected by MailGuard.
Each ploy attempts to steal passwords and other account information – sometimes installing costly malware with just one click.
And while you might know better than to click a grammatically-challenged email with an outdated logo, you’d be surprised by how many people take the bait.
Why are cybercriminals so determined to impersonate well-known brands?
Phishing scams come and go. They evolve and adapt as new tactics prove more lucrative. In fact, this year alone more than 18,400 Australians have fallen victim to phishing, costing more than $55 million, according to the Australian Competition and Consumer Commission.
So why are brand-impersonation scam emails so popular? Here are some factors:
- A ready-made audience: By targeting popular brands, recipients are more likely to a have relationship with the company being impersonated. That’s an instant foot in the door. More than 25% of all recipients open phishing emails, and a well-executed phishing landing page can yield a success rate as high as 45%, according to a study by Google and the University of California. How many marketers can claim a success rate as high as this? Not many, according to MailChimp.
- Just like the most successful criminals of the past, cybercriminals spent their time perfecting their plan of attack. One phishing email could be the result of months of planning. In some cases, it can even be outsourced to an expert hacker. A well-orchestrated phishing ploy is like a meticulously-planned bank robbery: nothing is left to chance. In the most lucrative phishing scams, opportunism doesn’t play a part.
- Recent data breaches involving big names such as LinkedIn, eBay, AOL, Vodafone, JPMorgan Chase and Verizon mean companies are now especially vigilant on cybersecurity. This means brands are quick to notify their customers in the event of a security risk, suggesting that passwords be changed or account information verified. By sending out similar correspondence, scammers are attempting to capitalise on security-conscious recipients and vigilant brands. Read more about the worst data breaches in internet history.
- Mocking up an email impersonating a trusted company is easier today than ever. Google Images provides logos and screenshots of recent outreach emails sent by the company, making replication relatively simple. It’s a simple way to exploit customer loyalty built up by big brands.
Attacks in the past 24 hours
Office 365 fake ‘undelivered message’
In today’s Office 365 phishing email, detected by MailGuard, the recipient receives a message about an undelivered message.
A link takes users to a fake Office 365 log-in page which harvests the credentials of the user.
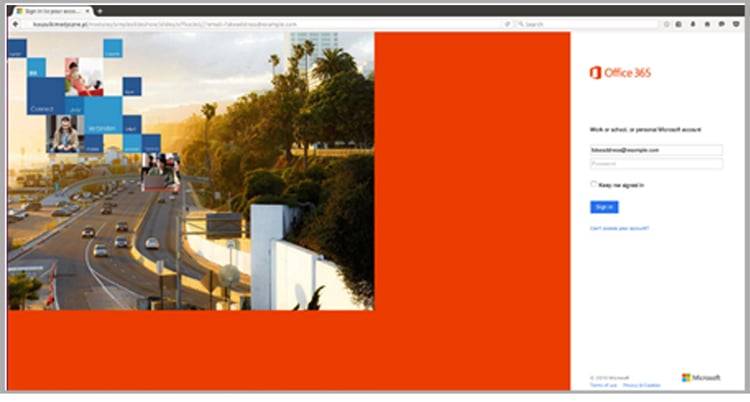
As many people – dangerously – use the same log-in and password information across many internet sites, victims may inadvertently hand over the keys to their bank accounts and other sensitive account information.
Fake Xero invoice malware scam
Meanwhile, Xero has again been impersonated by cybercriminals intent on a quick payday.
The phishing email appears to come from a Xero software user. It tells recipients they need to pay an outstanding invoice. A link in the email takes users to a SharePoint page containing malware.
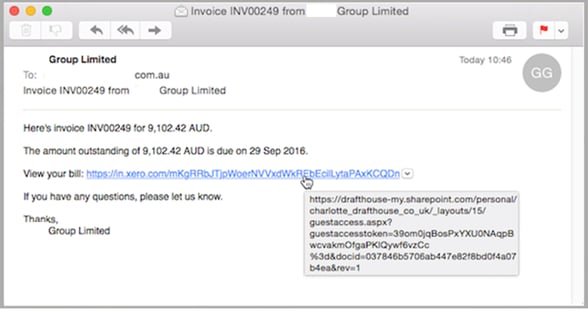
It’s the second time Xero users have been the target of a malware attack in the past week, albeit today’s version is on a much smaller scale. Other accounting software providers including Intuit QuickBooks and FreshBooks have also been targeted recently.
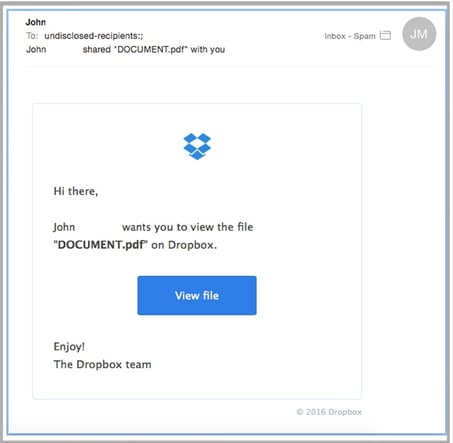
Scammers impersonate DropBox to siphon account details
Another fake log-in page is the vehicle for this faux-DropBox phishing attempt, identified by MailGuard this afternoon. Again the attempt is to harvest valuable log-in and password credentials.
How can I protect myself from these types of email scams?
To reduce the risk of being tricked by one of these scams, you should immediately delete any emails that:
- Seem suspicious and ask you to open or download files that you were not expecting
- Are purporting to be from businesses you may know and trust, yet use language that is not consistent with the way they usually write (including multiple grammatical errors)
- Ask you to click on a link within the email body in order to access their website. If unsure call the company/person directly and ask whether the email is legitimate.
For a few dollars per staff member per month, add MailGuard's cloud-based email and web filtering solution to your business security. You’ll significantly reduce the risk of new variants of malicious email from entering your network.
Our benchmarking shows that MailGuard is consistently 2-48 hours ahead of the market in preventing new attacks.
Find more tips on identifying email scams by subscribing to MailGuard’s blog.
Keep up to date on the latest email scams by subscribing to MailGuard’s weekly update or follow us on social media.







