A sophisticated fast-breaking payload email identified by MailGuard today exploits a bug in unpatched versions of Microsoft Office.
The high-tech phishing scam bypasses most virus scans: tests by MailGuard found that only five out of 60 traditional virus vendors detected it.
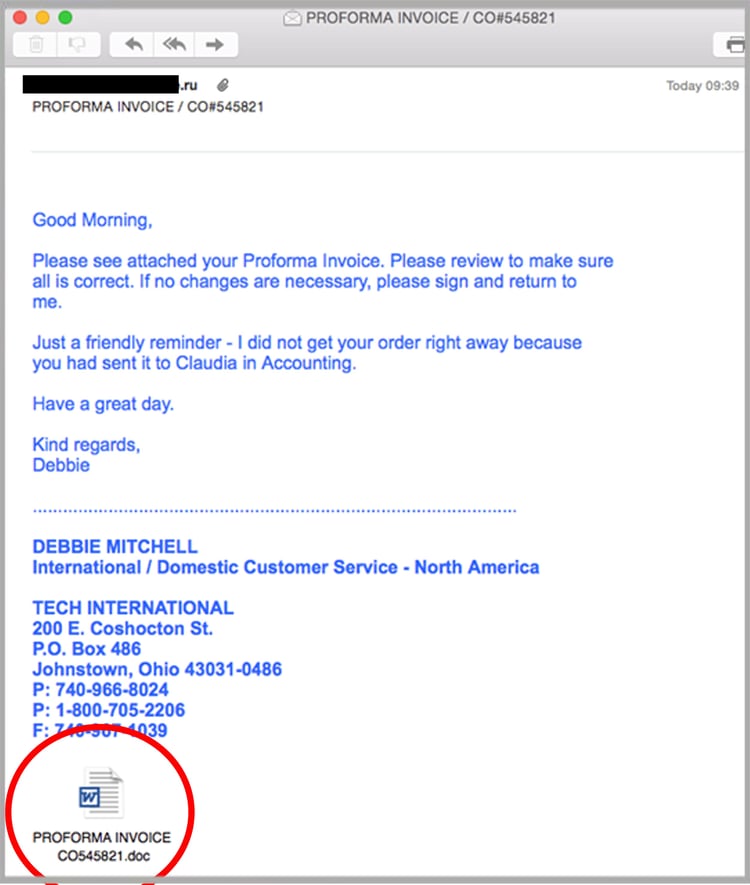
The zero-day phishing scam has two variations. One email has the subject: “PROFORMA INVOICE /CO#545821” and the other has the subject: “Purchase Order”.
Those who click the attachment run the risk of allowing malware to be installed in the form of a Trojan.
The email, sent from a compromised domain in an attempt to hijack the company’s legitimate reputation, asks recipients to check an invoice. It seeks confirmation that the details are correct, imploring the recipient to open the dangerous attachment. The attachment opens an image of an invoice in Russian.
Both emails include an exploit that could be potentially malicious. In both cases, the aim is to have the attachments opened, rather than a transfer of money. In the most severe case, code could be executed remotely if a user opens an attached Microsoft Office file.
As the malware runs with the same level of system permissions the recipient has, people with more system rights, such as administrators, face a higher risk of exploitation. If they are logged on, an attacker could take control of the affected system and install programs, view or delete data or create new accounts with full user rights.
While most phishing scams attach a macro, this takes the far more sophisticated – and difficult – approach of capitalising on an exploit in Microsoft Office.
To reduce the risk of being tricked by one of these scams, you should immediately report and delete any emails that:
- Are sent from companies you don’t normally deal with
- Are from companies you usually deal with but ask you to update payment details for their direct deposits
- Ask you to download or open attachments that seem unusual.
If in doubt, try contacting the company that appears to have sent you the email to verify it is legitimate.
We recommend you share these tips with your staff to make them aware of these campaigns.
By employing a cloud-based email and web filtering solution such as MailGuard, you’ll also reduce the risk of these new variants of phishing from entering your network in the first place.
Our benchmarking shows that MailGuard is consistently between 2 hours and 48 hours ahead of the market in preventing new attacks.
Keep up to date on the latest email scams by subscribing to MailGuard’s weekly update or follow us on social media.







