A new sham Apple phishing scam has emerged, which uses a range of tactics to fool users into surrendering personal information including their account and credit card details.
The Apple scam, which appears to originate from the American technology giant, gives readers the impression that unauthorised access may have occured on their account.
Below is a sample of the email you should look out for:
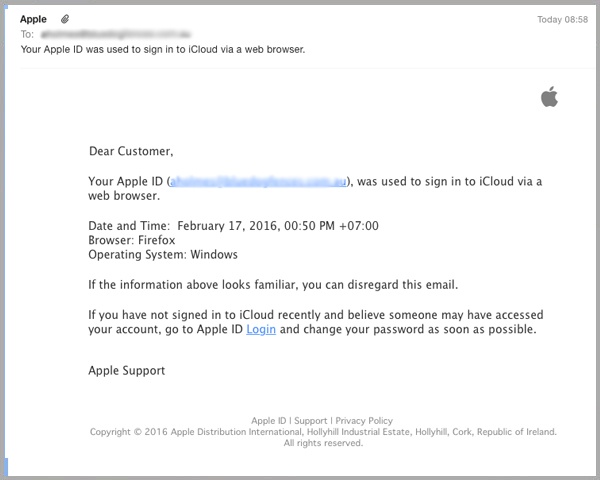
As you can see the email appears to originate from ‘Apple’, with use of their synonymous logo in the top right corner adding further sense of authenticity.
The email suggests that there may have been suspicious activity on the reader’s account, providing the date and time of a supposed unauthorised login to Apple’s iCloud service.
A sense of legitimacy is also added with the statement “If the information above looks familiar, you can disregard this email” – a clever double bluff which works to elicit an inquisitive response from readers, in a particularly savvy example of social engineering.
Readers are encouraged to click on the enclosed hyperlink to change their username and password immediately, before being taken to the below page:
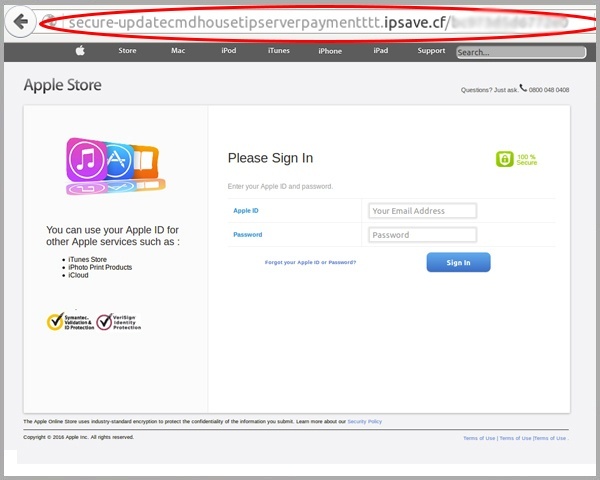
As you can see, this landing page is a carbon copy of an official Apple log-in page, although closer inspection of the URL clearly shows that the domain bears no relation to the American technology firm.
Once the user has submitted their username and password details, they are then told that access to their account has been disabled for security reasons, as shown below:
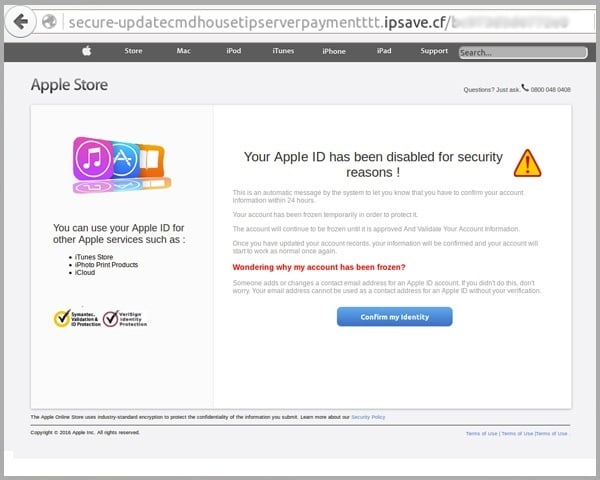
The page suggests that users will need to update their details in order to resume access to their account.
The use of grammatical errors might raise some suspicion, as you’d expect a reputable company to have a better eye for detail than this sentence: “Wondering why my account has been frozen? Someone adds or changes a contact email address for an Apple account.”
By clicking on the blue “Confirm my identity” button, readers are then taken to the below page, where they are asked to submit a range of personal details, including their name, date of birth, address, security question and answer.
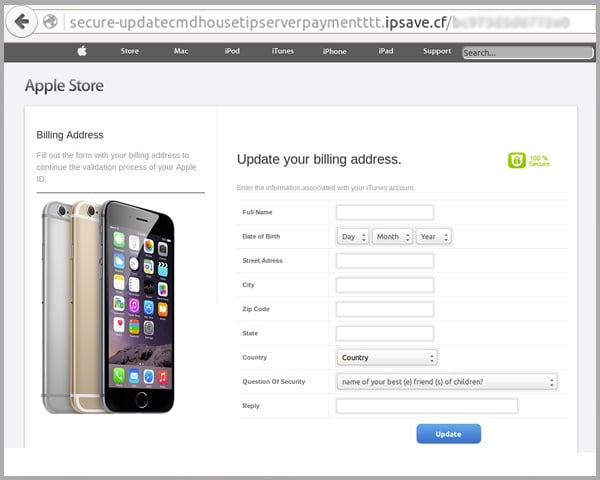
At this point, vigilant readers would immediately be suspicious of a webpage which asks them to update personal information which the purported organisation should already have access to.
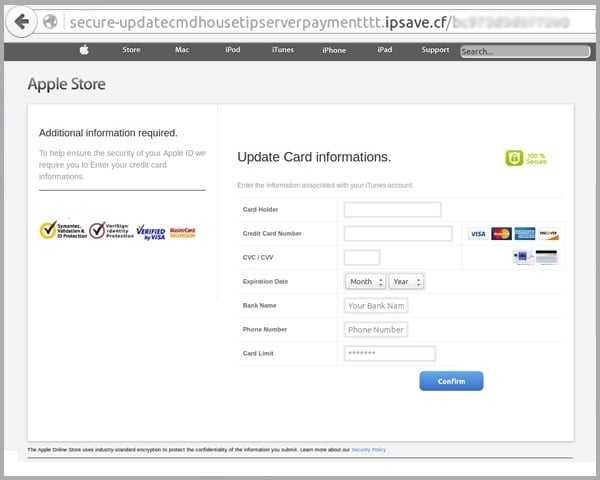
The suspicious nature of the request is heightened in the following screen, where users are asked to re-submit their credit card details, including their security number and expiry date, together with the limit value on the card:
After loading, this Apple scam takes readers to the below screen, which tells them their details have been updated successfully, before eventually redirecting to the official Apple login screen, again creating a sense of legitimacy.
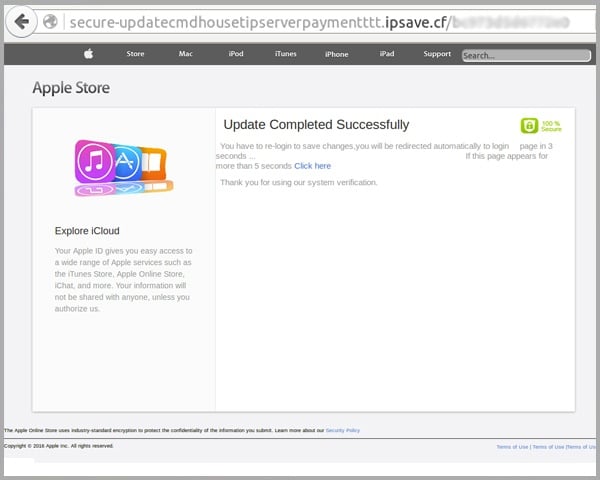
Users that fall for this fake Apple phishing scam will clearly give up a range of personal information which cyber criminals can then profit from.
Having surrendered their credit card details, they've given scammers the opportunity to appropriate funds or make purchases on their account, while submission of key personal details increases the likelihood of their identify being stolen.
By falsely claiming that unauthorised account access may have occurred, the cyber criminal has also persuaded the reader to unwittingly surrender details which will now allow this illegal access to occur: namely their Apple ID, password and security question/answer.
Why phishing emails are bad for business
Although this fake Apple phishing email is primarily targeted towards consumers, cyber criminals also use phishing emails to manipulate employees into surrendering access to a range of sensitive and valuable business information.
This can include access to your corporate usernames and passwords used to access and steal confidential data, or verification information used to access your business bank accounts and then appropriate funds.
Only last year, health insurer Anthem surrendered access to 100m health records as a result of phishing email, costing US$230m in legal and consulting fees alone.
The financial, reputational and litigation costs associated with phishing can therefore be huge, and it’s important that your business takes steps to protect itself.
We recommend that you educate staff on how to spot phishing emails in the event that they infiltrate your email inbox – you can access a range of hints and tips here.
You can also read more about how cloud-based email filtering works to stop malicious emails like phishing campaigns from reaching you in the first place here.
If you’ve received this fake Apple email scam, Apple ask that your forward it to reportphishing@apple.com. They also offer a range of information on how you can identify and report suspected phishing emails involving their company.
Keep up to date on the latest email scams by subscribing to MailGuard’s weekly update or follow us on social media.







