Popular entertainment company Netflix has once again been embroiled in a phishing email scam.
Containing several red flags that point to their illegitimacy, the phishing emails sent supposedly by Netflix are a good reminder for the need to remain cyber vigilant when accessing the web.
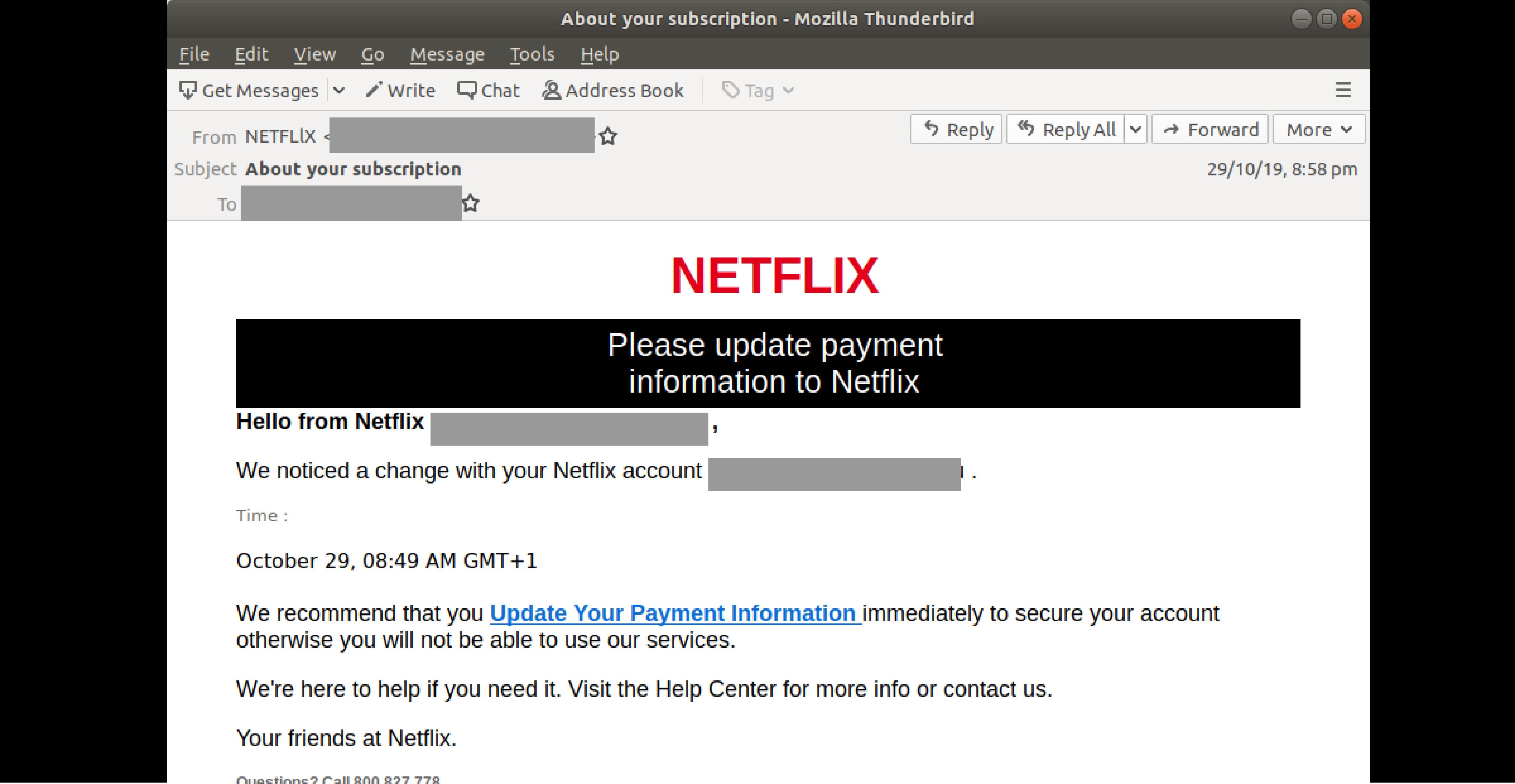
MailGuard first detected these malicious emails infiltrating inboxes across Australia on the 29th of October evening (AEST). Using a display name of ‘NETFLIX’ or ‘Netflix-Online’, the emails are titled ‘About your subscription’.
The body of the message contains the Netflix logo, and informs users that a change has been ‘noticed’ in their Netflix account. They are advised to update their ‘payment information immediately’ or risk not being able to use the popular digital entertainment tool. A link is provided for them to do so.
Here is a screenshot of the email:
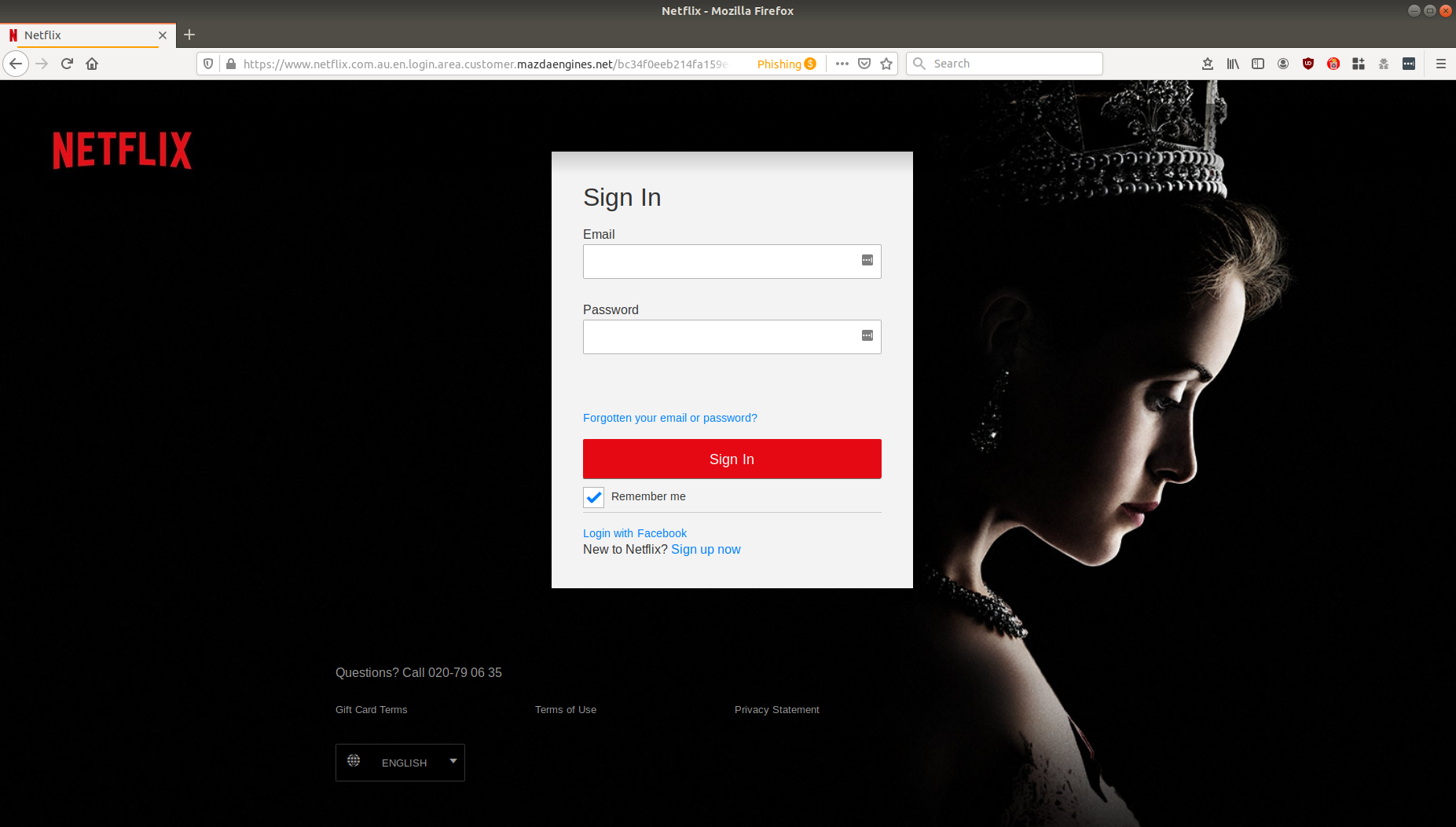
Unsuspecting recipients who click on the link to do so are led to a Netflix branded log-in page. Below is a screenshot of the page:
Upon ‘signing in’, users are then led to another phishing page asking for their credit card details, as per the below:
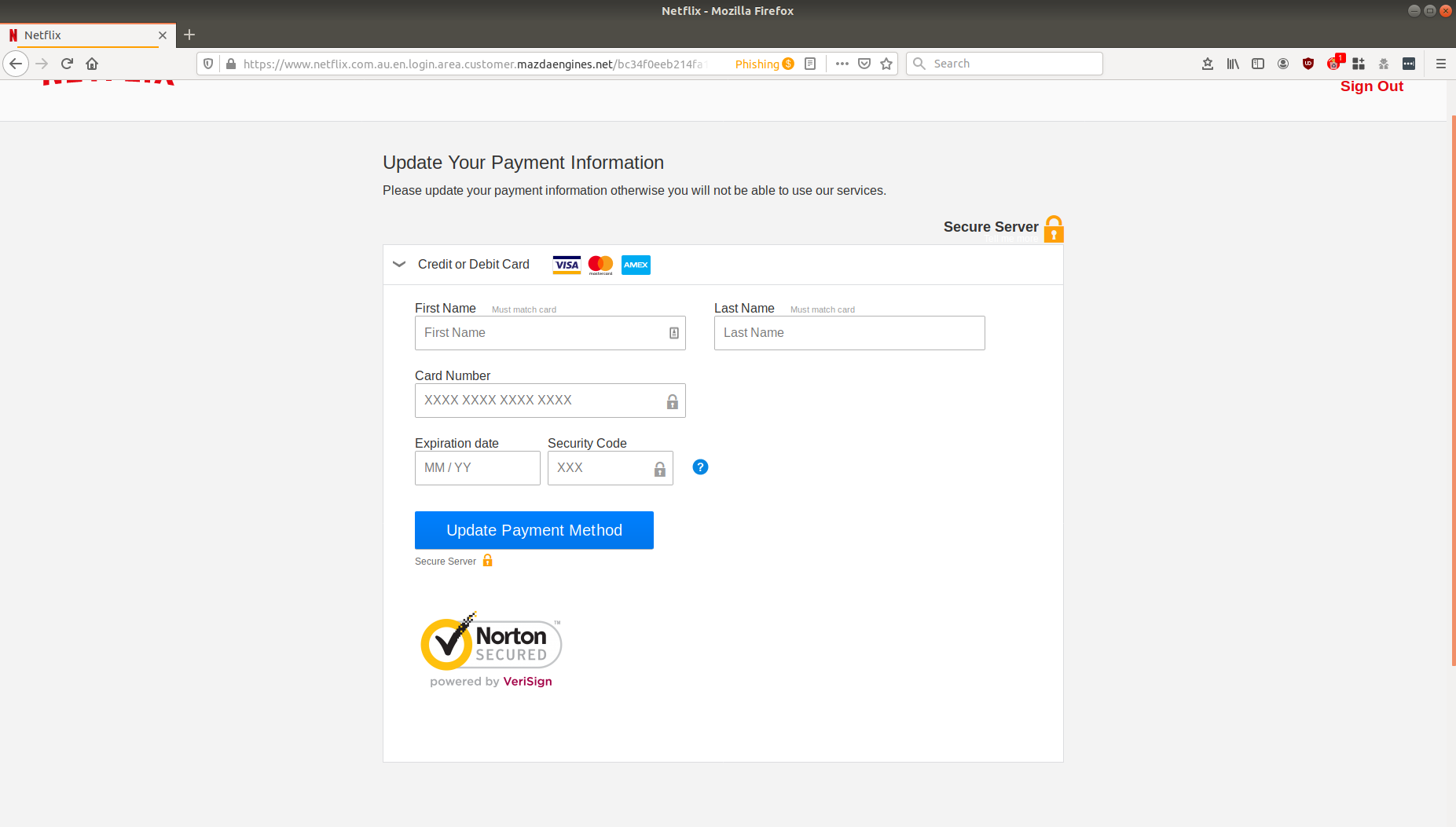
This is also a phishing page designed to harvest confidential payment data of users.
As you can see from the fake log-in above, cybercriminals have taken great pains to incorporate the exact colour scheme, logo, fonts and popular images commonly found in Netflix pages in a bid to convince the user that the email is actually originating from the entertainment company. The inclusion of the threat in the email that the recipients won’t be able to use Netflix’s services if they don’t update their payment information is also a trick designed to spark panic and urgency, motivating quick action.
However, while the email incorporates the branding and logo of the company, it contains several red flags for anyone who is vigilant enough to spot fake email scams.
Firstly, there are several grammatical and spelling errors within the body, such as “update payment information to Netflix”. Spacing errors are also present throughout the email, a trait that is expectedly not likely to be present if the email was, in fact, being sent from a well-established organisation such as Netflix.
This is not the first Netflix based scam MailGuard has seen recently. Netflix is a popular and well trusted company with an immensely large customer database, so their branding makes a good lure for cybercriminals looking to deceive people.
If you see an email from Netflix, please exercise caution and make sure it is a legitimate communication before you open it. Please share this alert with your social media network to help us make the people aware of the threat.
What to do if you receive such emails
As a precaution, avoid clicking links in emails that:
- Are not addressed to you by name, have poor English or omit personal details that a legitimate sender would include
- Are from businesses you’re not expecting to hear from.
- Ask you to download any files
Take you to a landing page or website that does not have the legitimate URL of the company the email is purporting to be sent from.
MailGuard urges email users to remember that cybercriminals prey on the brands that we trust and love, like Netflix. It's wise to always be skeptical of messages from unfamiliar senders asking you to log into your accounts.
Is your business receiving criminal intent emails?
It's time to get the protection your business needs.
Cybercriminals use email scams to infiltrate organisations with malware and attack them from the inside. All criminals need to break into your business is a cleverly-worded message. If they can trick one person in your company into clicking on a malicious link they can gain access to your data.
Speak to the MailGuard team today to learn more how MailGuard's predictive and advanced email security can help protect your business for a few dollars per staff member per month.
Talk to a solution consultant at MailGuard today about securing your company's network.
Why not stay up-to-date with MailGuard's latest blog posts by subscribing to free updates? Subscribe to weekly updates by clicking on the button below.







