MailGuard has intercepted phishing emails that are purporting to be from St. George Bank.
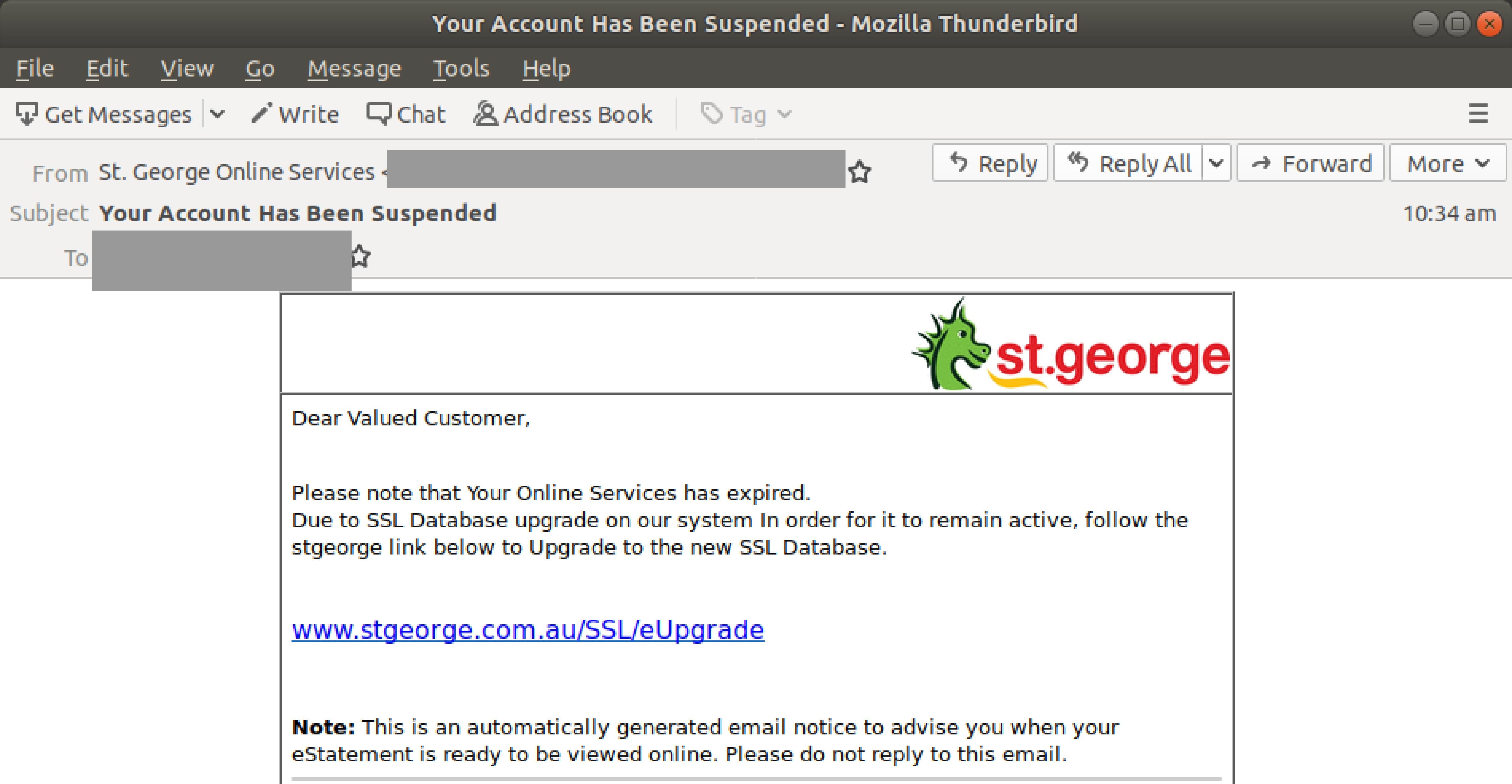
First detected earlier today morning, the 30th of October 2019, the emails use the display name ‘St. George Online Services’ and are titled ‘Your Account Has Been Suspended’. The body of the email advises recipients that their ‘Online Services’ have expired and they need to ‘Upgrade to the new SSL Database’ to re-activate those services.
Here is a screenshot of the email:
Unsuspecting recipients who click on the link to ‘upgrade’ are led to a fake St. George branded ‘logon page’, as per the below:
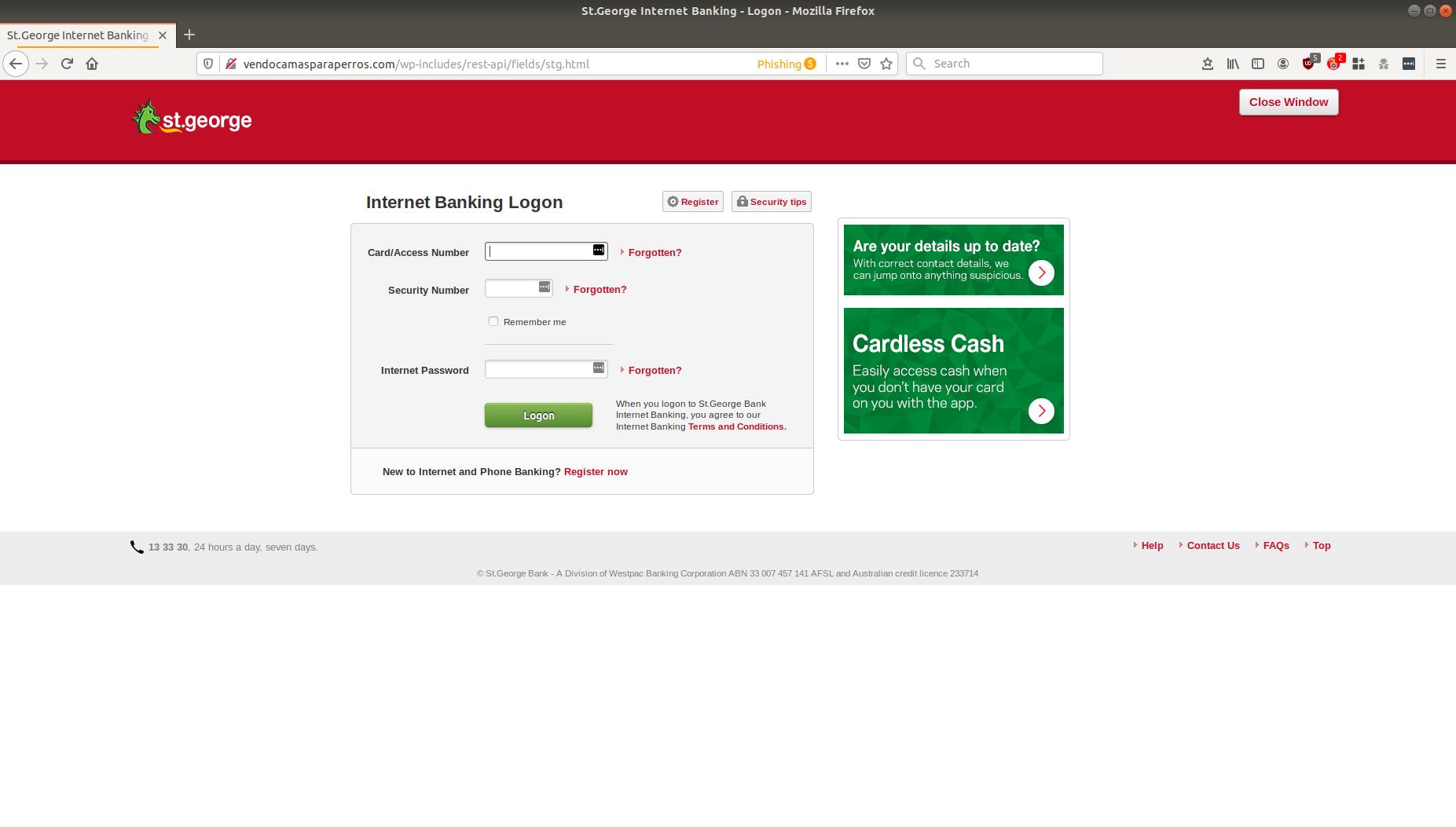
This is a phishing page that’s designed to harvest the login credentials of St. George Bank customers so the criminals behind this scam can break into their bank accounts.
As you can see from all the screenshots above, cybercriminals have attempted to replicate official landing pages from St. George Bank – including incorporating the bank’s branding and logo. All this is done in an attempt to trick the users into thinking the scam is legitimate.
It is also interesting to note that the email and the phishing pages ironically use security features such as account upgrades to trick recipients. This is a common trait expected of such a well-established bank. All this serves to elicit a more confident response from recipients who think they are, in fact, making their accounts more secure by clicking on the provided link and entering their confidential login details.
On top of this, this message contains several typical elements of a phishing email:
- use of a major brand name to inspire false trust; the usage of the supposed ‘St. George Online Services’ display name boosts the credibility of the email,
- repeated usage of ‘safety features’ typically expected of a well-established bank such as links to avoid hoaxes and bank support numbers,
- false urgency; a subject line such as ‘Your Account Has Been Suspended’ creates a sense of panic and anxiety
To reduce the risk of being tricked by one of these scams, you should immediately delete any emails that:
- Appear to be from a well-known organisation, typically a bank or service provider and are not addressed to you by name and may include poor grammar.
- Ask you to click on a link within the email body in order to access their website – your bank will always ask you to go to their website directly by typing their URL into your web browser address field, as a precautionary security measure.
- Ask you to submit personal information that the sender should already have access to.
Banks commonly hold a well-established and trusting relationship with customers, so when cybercriminals are looking for good trademarks to use in their email attacks they often brandjack banks.
St George Bank has an advisory page where they offer advice on how to avoid fraud. In the event that their customers receive fraudulent email, St George advises them to call the bank on 13 33 30 for advice.
If you've received this email, delete it immediately without clicking on any links.
MailGuard urges email users to remember that cybercriminals prey on the brands that we trust and love, like Microsoft. It's wise to always be sceptical of messages from unfamiliar senders asking you to log into your accounts.
Is your business receiving criminal intent emails?
It's time to get the protection your business needs.
Cybercriminals use email scams to infiltrate organisations with malware and attack them from the inside. All criminals need to break into your business is a cleverly-worded message. If they can trick one person in your company into clicking on a malicious link they can gain access to your data.
Speak to the MailGuard team today to learn more how MailGuard's predictive and advanced email security can help protect your business for a few dollars per staff member per month.
Talk to a solution consultant at MailGuard today about securing your company's network.
Why not stay up-to-date with MailGuard's latest blog posts by subscribing to free updates? Subscribe to weekly updates by clicking on the button below.







