A highly-sophisticated new ATO phishing scam uses the lure of a tax refund to steal Australians’ banking details and personal information.
The email, which appears to be from the Australian Taxation Office and is titled ‘ATO Refund Status’, differs from other phishing scams which tend to contain links to compromised websites.
Instead, the email includes an attached HTML file, titled TaxReturn.htm. If clicked by a curious recipient, the phishing website is copied to a temporary directory on their computer, and is loaded into their browser.
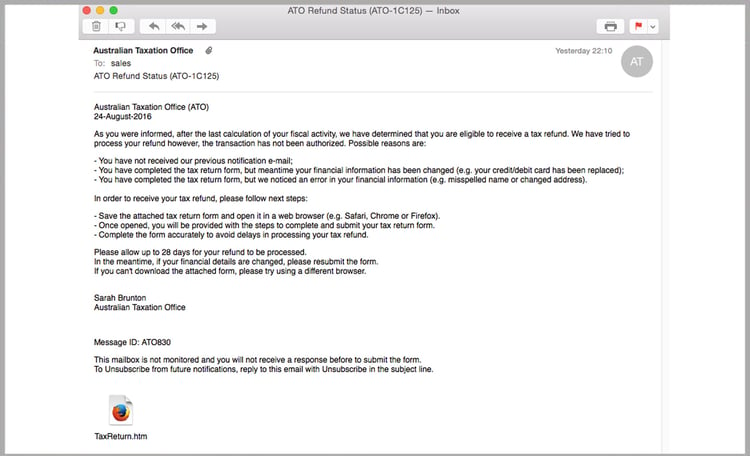
This is where the sophistication of the scam becomes clear.
Those who click the attachment are sent to an official-looking ATO page, complete with logo and references to the still-relevant Taxation Administration Act 1953.
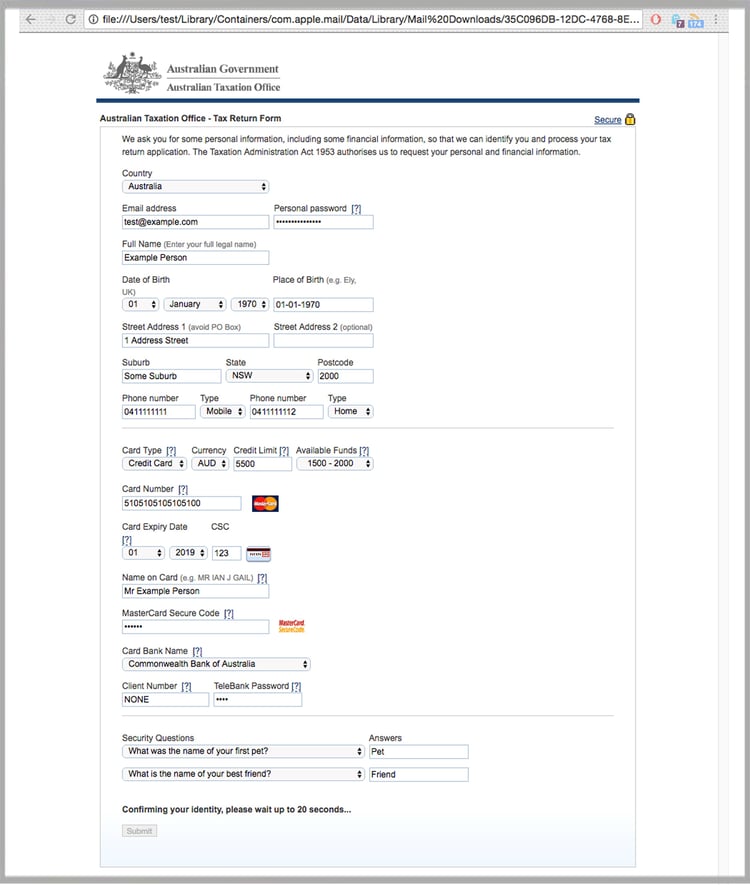
If the recipient begins to fill out the fields presented, more fields begin to appear. The fields become more probing; as they progress through the form, users are asked for details including:
- Email address and password
- Date of birth
- Address
- Credit card number, expiry date, credit limit and funds available
- Bank name, customer number and phone password
- Bank security questions and answers
Cleverly, the fields are dynamic: attempts to input a fake email addresses and credit card numbers are immediately met with an error message.
Those who fill out the form and click ‘Submit’ are advised that their identity is being confirmed.
Finally, a confirmation page advises victims their information is being processed and that their tax return is imminent.
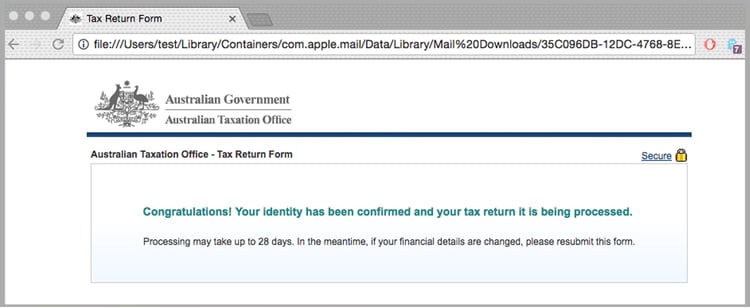
Instead, their private information is being transferred into criminal hands.
MailGuard CEO Craig McDonald said a lot of work had gone into developing the scam.
“They’ve done their homework,” he said.
“All the banks in Australia have been added to the ‘bank name’ dropdown menu and the information victims provide is immediately verified. Attempts to input an incorrect MasterCard sequence are immediately knocked back.
“They’ve spent a serious amount of time developing this scam. Most likely the aim is to sell the information they can gather on the black market.”
Why an attachment?
What does the ATO scammer have to gain by giving targets an attachment, rather than a link to a fake ATO website?
Saving an HTML file to your computer bypasses link-checking security systems, known as RBL (Real-time Blackhole List). These keep track of domain names and IP addresses that are known to generate spam.
To reduce the risk of being tricked by one of these scams, you should immediately report and delete any emails that:
- Appear to be from a well-known organisation, typically a bank or service provider, and are not addressed to you by name and/or may include poor grammar
- Ask you to click on a link within the email body in order to access their website or download suspicious files. If unsure call the company directly and ask whether the email is legitimate
- Offer money, reward or gift to entice you to hand over your personal details
- Ask you to submit personal information that the sender should already have access to or should not be requesting from you in the first place
The Australian Tax Office website shares advice on how to verify and report scams impersonating the ATO.
We recommend you share these tips with your staff to make them aware of these campaigns.
By employing a cloud-based email and web filtering solution such as MailGuard, you’ll also reduce the risk of these new variants of phishing from entering your network in the first place.
Our benchmarking shows that MailGuard is consistently between 2 hours and 48 hours ahead of the market in preventing new attacks.
At the time of writing, only one out of 67 vendors are currently flagging this content as malicious.
Keep up to date on the latest email scams by subscribing to MailGuard’s weekly update or follow us on social media.







