Microsoft Teams, a popular digital collaborative platform among businesses, has been fraudulently mimicked by cybercriminals in a phishing email scam intercepted by MailGuard.
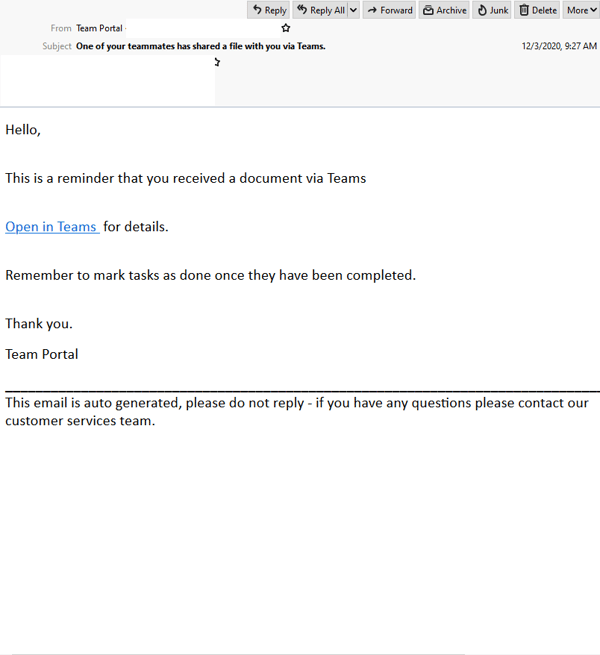
Titled “One of your teammates has shared a file with you via Teams”, the email uses a display name of “Team Portal”. However, it doesn’t contain any other branding elements (like logos) or styling related to Microsoft. The email actually originates from a compromised Amazon SES account.
The email appears to be an auto-generated “reminder” claiming to a share a document via Teams. A link is provided for users to view the file in Teams, along with a reminder to “mark tasks as done once they have been completed”.
Here's what the email looks like:
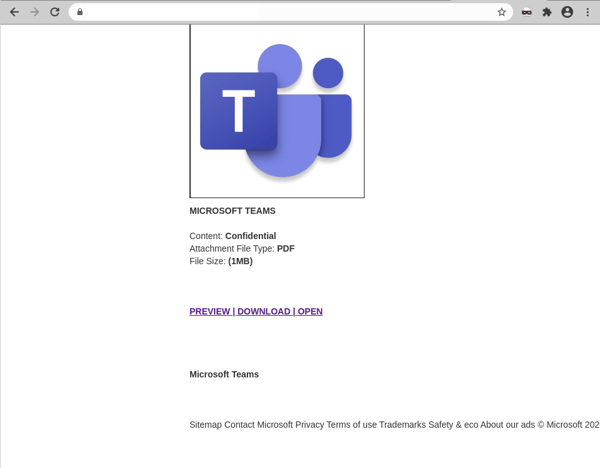
Unsuspecting recipients who click on the email are led to an intermediary page, containing details about the file, like file size & format. This page employs Microsoft Teams’ logo and other branding elements, including a footer. However, the domain used in the page’s URL doesn’t belong to Microsoft. The page is actually hosted on a third-party website generator. Here’s a screenshot of the page:
Here’s what the page looks like:
Clicking on the links to preview, download or open the file leads users to a login page asking for their email address and password. Similar to the intermediary page, this page also employs Microsoft’s branding. However, the domain used in the page’s URL doesn’t belong to the tech company. It’s actually a phishing page hosted on a compromised WordPress site.
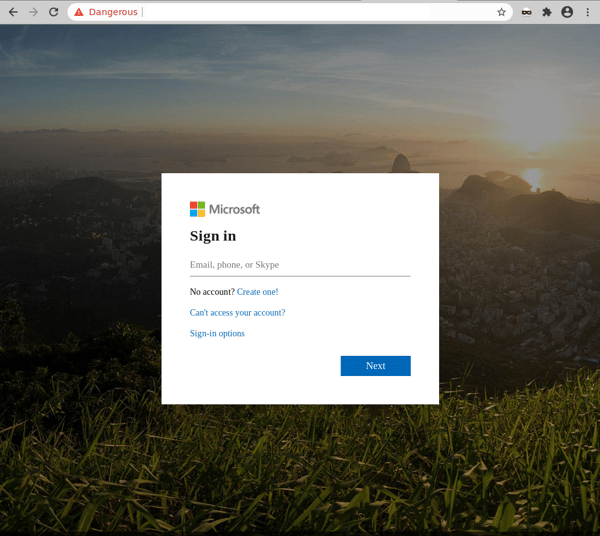
Once users enter & submit their credentials, the attacker harvests them for later use. Users are then met with an error saying that the credentials are invalid.
We strongly advise all recipients to delete these emails immediately without clicking on any links. Please share this alert with your social media network to help us spread the word around this email scam.
This is a good example of how cybercriminals are leveraging on recent trends in the way we communicate and work. With more companies employing remote working policies for their employees in light of the COVID-19 pandemic, the usage of collaborative business & videoconferencing platforms like Microsoft Teams has skyrocketed over the past year. With 115 million daily active users, there’s a high chance the recipients of this phishing email have a Microsoft Teams account, increasing the likelihood of the scam being successful. Cybercriminals know this, and often frequently exploit the branding of global companies like Microsoft in their scams, because their good reputation lulls victims into a false sense of security.
Here are a few ways how cybercriminals behind this scam have attempted to exploit users:
- The use of a display name like "Team Portal"; this suggests the email is sent from a credible source, boosting its credibility,
- Inclusion of the Microsoft Team logo and Microsoft’s branding elements further aims to convince users into thinking the email is authentic, and
- With false urgency; a subject line and an email body about the arrival of a document creates a sense of curiosity and excitement, motivating users to act immediately without checking on the email’s authenticity.
Despite these techniques, eagle-eyed recipients of this email would be able to spot several red flags that point to the email’s in-authenticity. These include the fact that the phishing pages aren’t hosted on a Microsoft domain, and that the recipient isn’t addressed directly in the email.
This practice of launching cyberattacks that are centered around ongoing trends isn’t anything new. Over the past year, we have intercepted various malicious emails impersonating other collaborative tools, like Zoom, and those related to COVID-19.
As such, we strongly advise being extra vigilant when you receive emails such as these and lookout for any tell-tale signs that might be suspicious.
As a precaution, MailGuard urges you not to click links within emails that:
- Are not addressed to you by name.
- Appear to be from a legitimate company but use poor English, or omit personal details that a legitimate sender would include.
- Are from businesses that you were not expecting to hear from.
- Take you to a landing page or website that is not the legitimate URL of the company the email is purporting to be sent from.
One email is all that it takes
All that it takes to break into your business is a cleverly-worded email message. If scammers can trick one person in your company into clicking on a malicious link they can gain access to your data.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive and advanced email security.
Talk to a solution consultant at MailGuard today about securing your company's network.
Why not stay up-to-date with MailGuard's latest blog posts by subscribing to free updates? Subscribe to weekly updates by clicking on the button below.







