MailGuard has successfully identified and blocked a highly-sophisticated spam campaign which uses Microsoft Word files to infect computers with crypto ransomware.
In a similar vein to a recent Word macro malware attack, this variant relies on users opening an email attachment which utilises a macro in order to infect their computer.
However, in this example, cyber criminals have combined a range of deceptive techniques in a way we’ve previously not seen before.
Here’s a screenshot of the type of email you should look out for:
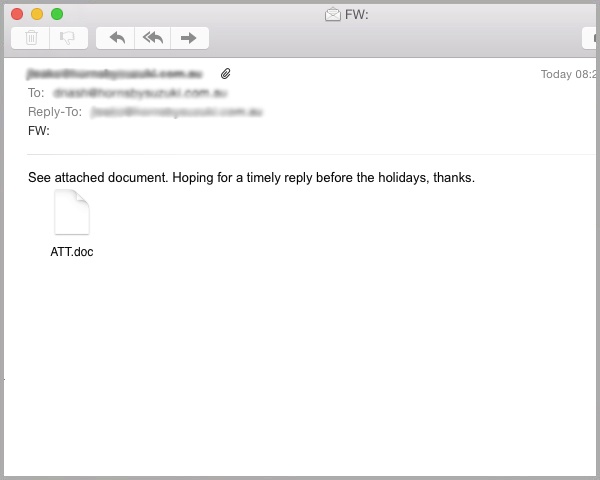
As you can see, the spammer has used a typical email template to create this attack, encouraging the user to open the attached Word ‘.doc’ file.
However, here the sender has managed to forge its email address to mimic the recipient’s domain (although for privacy reasons we’ve blanked it out).
Forging the 'from' header to match the recipient's domain name – a widely-used technique used in spear phishing scams – fools readers into thinking the email is a legitimate communication from someone within their company, or from a trusted associate.
However, in this case, further investigation shows that the spammer’s true domain address or “envelope” address, is of no relation to the recipient’s.
By asking for readers to reply “before the holidays”, at a time when most staff members will be winding down for Christmas, it instils a sense of urgency and entices the recipient to open the attachment without thinking – increasing the likelihood of the malware being delivered.
Once the Word attachment has been opened, users will see the screen below.
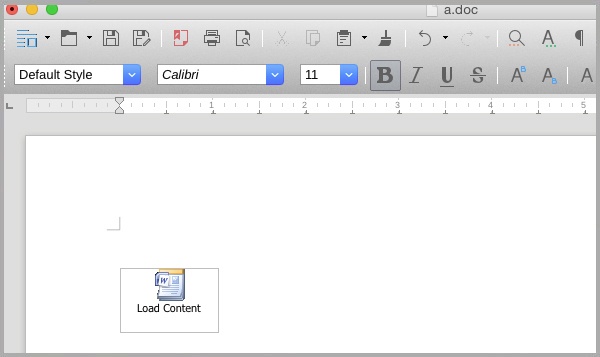
The way that this campaign differs to other recent macro malware spam attacks is that recipients are then prompted to open a second Microsoft Word attachment which is contained within the document itself.
It’s only when a user opens this secondary file that a Visual Basic script contained within the file is activated, beginning a sequence of events that leads to the computer becoming compromised with Crypto malware.
The contained macro creates and saves a new file to your computer, then instructs Windows to execute this file. This then prompts the download of the final payload, which in this case is an advanced piece of crypto ransomware.
Once downloaded and executed, the crypto malware cripples sensitive data by encrypting specific data files and documents within the recipient's network, restricting access to them. Cyber criminals then typically demand a hefty ransom payment before allowing you to regain access to your files.
This case is particularly interesting as cyber criminals have utilised Microsoft’s Object Linking and Embedding (OLE) technology, to create a “daisy chain”, allowing them to hide malicious macros within a secondary file attachment.
In doing so, spammers hope that security protection won’t scan attachments on secondary level, increasing the chance of the message getting through to your inbox.
More on macro malware.
Professional services employees such as accountants, financial analysts and risk managers will often receive file attachments containing word macros, normally used to automate and speed up repetitive tasks.
However, cyber criminals are increasingly using macros for malicious purposes in order to infect businesses – we recently reported on a scam in which Human Resources professionals were targeted using fake job applications.
Recent versions of Microsoft Word disable macros by default in order to reduce the security threat. However, by tricking users into opening the second attachment, they are able to fool the victim into enabling the macro.
Protect yourself or risk financial penalties.
Once crypto ransomware has taken hold of your machine, you have the choice of either paying the ransom fee or risk losing your files and data forever.
That’s why it’s really important that you take extra care to educate staff not to open emails that don’t address them within the email’s body copy by name and contain attachments or links to suspicious pages.
However, as this case shows, with advanced social engineering techniques being used, it’s becoming more and more difficult for staff to differentiate between malicious content and genuine emails.
Firms must therefore make sure that they employ a security mix which stops spam from getting into their mailbox in the first place.
Employing a cloud-based email and web filtering is your first and best line of defence. By identifying new varieties of malware, like crypto, in real-time, they are able to block them at the point of detection.
By combining these services in a multi-layered approach, with on premise antivirus, anti-malware and anti-spyware solutions, you can help to mitigate risk from a wide range of malware delivered through multiple vectors.
Keep up to date with email scams affecting your business by subscribing to MailGuard’s weekly update.
Microsoft is a registered trademark or trademark of Microsoft Corporation in the United States and/or other countries.







