Australians have again been targeted with another fake Australian Federal Police (AFP) infringement campaign which attempts to trick users into downloading damaging ransomware.
This campaign is almost identical to another attempt last year, with cyber criminals tricking email recipients into downloading ransomware, which is likely to lock the victim’s files before demanding a hefty ransom fee in return for a decryption key.
Here is a sample of the email you should look out for:
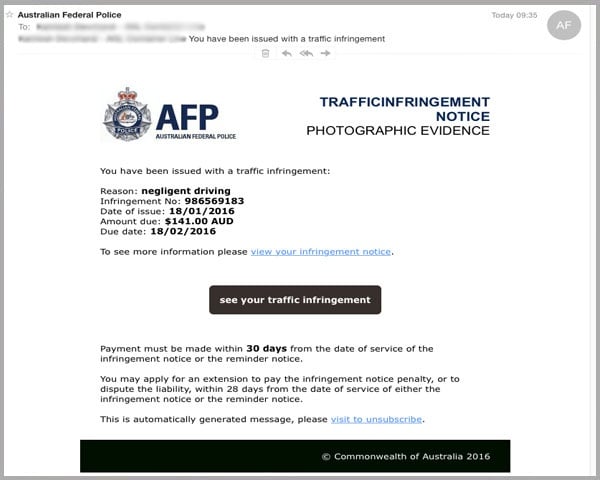
As you can see the email appears to come from Australian Federal Police, providing a sense of legitimacy, with the scammers editing the “header from” email address in the email settings.
Further investigation shows that the email has actually been sent from a compromised email account that the scammer has successfully hacked into. Use of the official AFP logo also provides further sense of authenticity.
In a change from other recent AFP email scams which included poor language and grammatical mistakes, this email is well-written, showing that cyber criminals are getting wiser and improving the quality of their scams.
The email includes a range of details about a supposed traffic infringement, and requests that the reader clicks on an enclosed link to “view your infringement notice”.
The AFP scam uses advanced social engineering techniques to make the reader respond quickly, including a statement that the payment must be made within 30 days.
Clicking on this link then directs recipients to a fake AFP landing page shown below, which is almost identical to the legitimate AFP site:
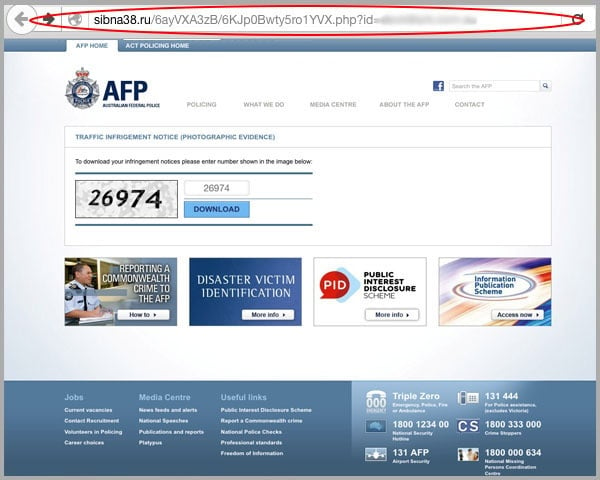
As you can see from the URL this clearly isn’t a legitimate AFP page, but the quality of the replica is very good and includes identical images, buttons and a detailed footer, which can be enough to fool email recipients.
The page asks the user to continue to the next step by entering a verification number, before downloading their infringement notice. The verification number never changes and is the same for every user.
Once the reader has proceeded, they are then asked to confirm the download of a .zip file – this file contains ransomware that could encrypt files and install other malware:
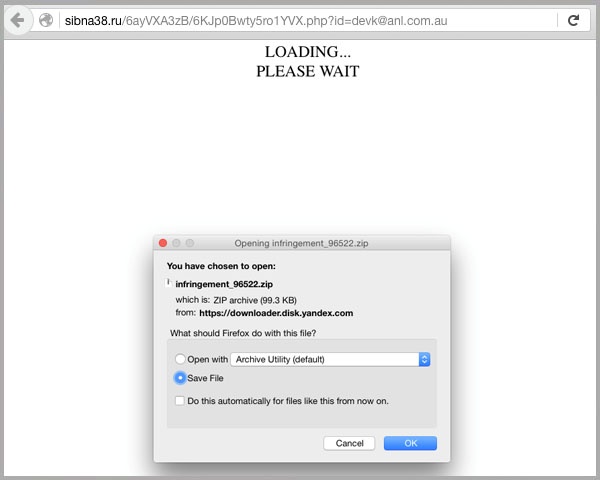
Once this file has been executed, it is likely to encrypt all the files on your network and prevent you from accessing them until you’ve paid the cyber criminals a hefty ransom fee. In some instances, not even guaranteeing the decryption key.
Protecting yourself from ransomware campaigns
In order to protect yourself from ransomware campaigns like this AFP email scam, it’s important that you educate team members on the typical warning signs of attacks:
- The Australian Federal Police never send out traffic infringement notices via email
- Never click links within an email that seem suspicious – if you are expecting an email from a legitimate company such as a bank or government organisation, go directly to their website through your browser or Google search
- Always check the URL of the landing page you’re being directed to by hovering your mouse over the link – if the URL looks suspicious, don’t click it
- Don't download any .exe or .zip files unless you’re absolutely sure that they’re legitimate, as these files are the most common types used to deliver malware. Your business can help to protect itself by restricting the ability of staff to download .zip or run .exe files without permission from the Network Administrator
- Back up your business data every day – giving you a safety net should your data ever be held to ransom
- As these scams get more professional by the day, you’ll need to be increasingly vigilant – you should always call the organisation in question if you are suspicious about an email they have purportedly sent you.
User education and sharing prevention tips will help mitigate risk to your business, but won’t stop malware scams from getting into your inbox in the first place.
Employing cloud-based email and web filtering offers the first line of protection by identifying new varieties of malware in real-time, blocking them before they even reach your network.
By layering these on top of an on-premise antivirus, anti-malware and anti-spyware solution, you can mitigate the risk from a wide range of online scams.
To educate your staff on how to identify spam, malware and more, feel free to share this helpful blog: Don’t Click That! Your Guide To Cyber-attacks And Tips For Being Cyber Safe Within Your Business.
Keep up-to-date on the latest email scams by subscribing to MailGuard’s weekly update or follow us on social media.







