MailGuard have identified and successfully blocked a malware scam email purporting to be from the Australian Taxation Office.
There have been a number of variations of the ATO scam over the years, proving successful by preying on people’s hope of receiving more money back on tax.
The observed emails form part of a malicious malware attack, where attachments have been 'camouflaged' in order to hide their true intent.
Here is a screenshot of the type of email to watch out for.
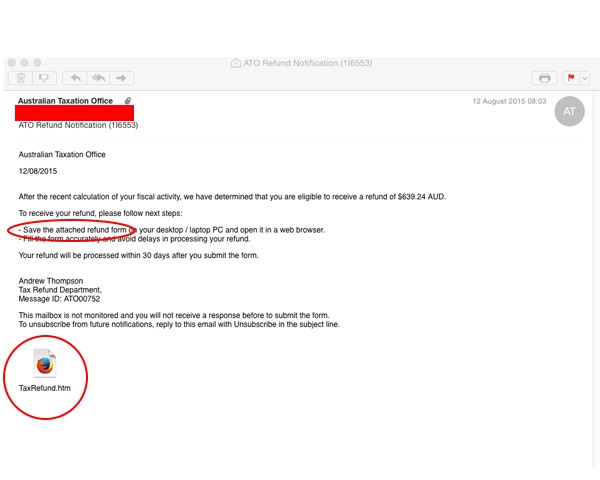
As you can see, the email appears to originate from the Australian Taxation Office, and requests vulnerable victims download and complete an “attached refund form” to receive their supposed tax refund.
The email does a lot right to convince its target that the email is legitimate.
- It addresses the victim by appearing as if they are emailed directly, and not as part of a bulk spam blast encompassing multiple recipients.
- It specifies a refund notification number and appears to come from an employee of the Tax Refund Department.
- The email is competently written and even appears to comply to the SPAM act requiring email notification if they wish to unsubscribe.
Where this particular scam fails is in directly requesting personal information the ATO already has access too. We cannot stress enough that organisations like the ATO will never ask you to give personal information via email or downloadable files.
The email encourages the user to download and open the attached TaxRefund.htm file. Unfortunately, at the time MailGuard discovered this new variant, no other antivirus vendors were detecting this scam - the target is subsequently able to download and open the file without being intercepted.
When the file is run, it launches on the local machine within a web browser and displays as a standard phishing scam. However, after further inspection of the file’s source code, this attack has an ulterior motive as a multipronged exploit. Upon launch, the malware lodges into the windows start up routine to infect the computer. Whilst the untrained eye assumes they have dodged a bullet in detecting the file as a phishing scam and exiting the web page, their system has already been infiltrated in the background.
What’s happening in the background? Why aren’t AV vendors detecting this scam?
Spam senders have gone to great lengths to try and hide this entire web page in code. The source code of the .htm file reveals a command that transforms the web page into valid HTML able to confuse spam filters and bypass virus scanners.
MailGuard has successfully identified and blocked many variations of ATO scams, read more about these via the links below:
- Bogus ATO 'refund' email detected as October 31st tax deadline approaches
- Another Fake ATO Tax Return Scam
- Fake ATO Tax Return Scam
There are many key identifiers for an email recipient to check when assessing if an email is a fraudulent one. To find out more, take a look at our blog, Don’t Click That! Your Guide To Cyber-attacks And Tips For Being Cyber Safe Within Your Business.
Educating staff and employing cloud-based email filtering and web filtering, complimented by multilayered defences including desktop antivirus, anti-malware and anti-spyware will go a long way to mitigating the risk from a wide range of email scams.
Keep up to date on the latest email scams by subscribing to MailGuard’s weekly update or follow us on social media.







