In early 2021, the FBI issued a notice which warned that both domestic and international companies were seeing a sharp increase in vishing attacks. At the time, they attributed the rise in attacks to the switch to remote work that many companies made in response to the COVID-19 pandemic. Yet despite the fact that many businesses have made a full or partial transition back to the office, reports of vishing and smishing attacks continue to rise.
Vishing, short for voice or voicemail phishing, is when a criminal uses voice communication in an attack in order to access sensitive information. In a similar vein, smishing refers to when criminals use SMS to carry out their phishing attack.
Here's a common example of smishing:
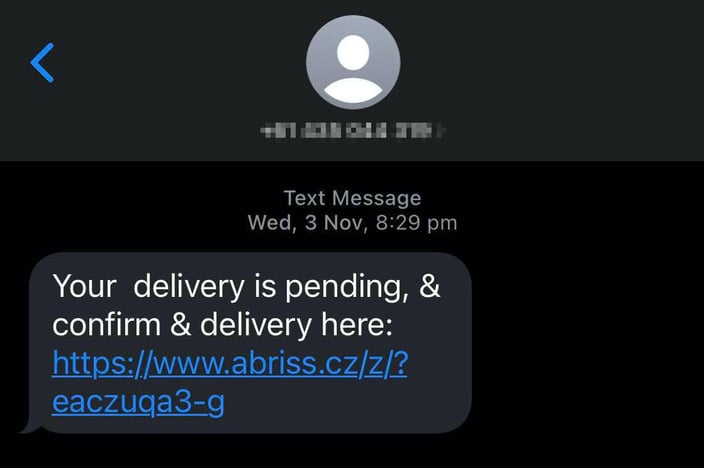
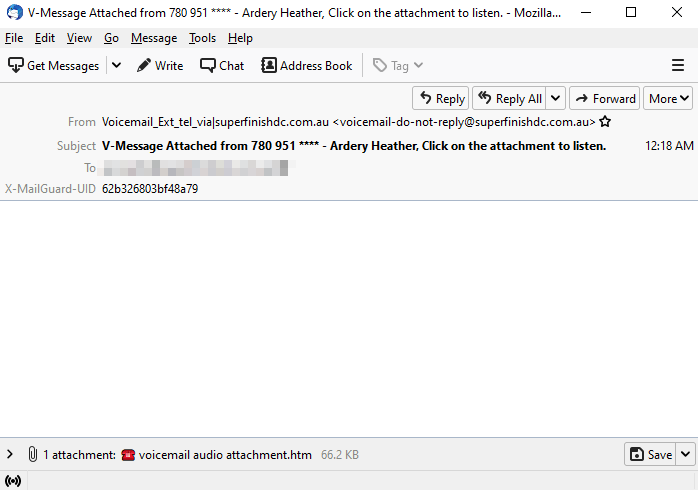
However, vishing also extends to promises of voice communication, such as the scam MailGuard recently intercepted where victims receive an email claiming they have a voicemail, but the attachment really leads them to a phishing page where their email credentials could be stolen. Such tactics have recently been used to target tech organisation and military personnel, leading to the U.S. Army putting out a warning to their community to be on the lookout for smishing and vishing scams.
This is how vishing emails can appear in your inbox:
New research has revealed that vishing attacks increased by more than 500% from 2021 to 2022, causing international organisations to take notice and act. Earlier this month, INTERPOL revealed they had orchestrated a worldwide crackdown on telecommunications fraud and business email compromise (BEC) scams. Taking place over a two-month span (8th of March 2022 – 8th of May 2022), police from 76 countries participated in the operation.
Although all results have not yet been confirmed, the preliminary figures from the clampdown include:
- More than 1,700 locations raided worldwide,
- Approximately 3,000 suspects identified,
- The arrests of roughly 2,000 operators, fraudsters, and money launderers,
- Frozen funds in around 4,000 bank accounts,
- And, approximately USD $50 million in fraudulently gained funds seized
Duan Daqi, Head of the INTERPOL National Central Bureau in Beijing stated that “The transnational and digital nature of different types of telecom and social engineering fraud continues to present grave challenges for local police authorities, because perpetrators operate from a different country or even continent than their victims and keep updating their fraud schemes.”
The rise in cases of this sort is of particular concern as in recent years, employees have increasingly been using work devices to access personal information and services, which is a threat in itself, but is magnified by the reduced oversight that comes with remote work. Although vishing and smishing scams frequently target individual consumers, if their accounts or devices are compromised, it may leave their business vulnerable to the attack too.
So, given vishing and smishing are becoming such major security threats, what can your clients do to avoid falling victim to a vishing or smishing attack?
Preventing Vishing/Smishing Scams
Your clients should always be sceptical of any phone calls or text messages they receive that:
- Claim to be from or acting on behalf of a government agency
Government agencies such as the Australian Tax Office or Medicare will typically not reach out via phone or SMS unsolicited, especially not with requests for money. For those in Australia, messages are usually communicated via the myGov app unless requested otherwise. - Ask for personal information
Always confirm the identity of the person on the other end of the line before handing out any sensitive information or transferring money, even if they’re able to provide some information on you – it could have been scraped from social media. - Have a sense of urgency
Scammers prey on fear, so will frequently threaten legal trouble, financial penalties, or other repercussions if you don’t meet their demands within a short time frame. Don’t fall for the pressure. Instead, end the call and ring the individual, company, or agency yourself to confirm if the request is legitimate – just make sure not to hit redial as phone numbers can easily be faked. - Request remote access to your device
Unless it’s a call from your IT department, don’t give remote access to your device to anyone who rings you first, no matter what business, bank, or agency they claim to be from. The scammer will most likely have a credible story as to why they need to access your computer, but by doing so, they’ll also be able to access private information and potentially online banking accounts.
Whether it’s in their personal or business lives, your clients are sure to face a barrage of smishing and vishing attacks as they continue become a more popular method for scammers. We recommend sharing these tips with them to prevent the attacks becoming successful.
Keeping businesses safe and secure
Prevention is always better than a cure, and the best defence is to encourage businesses to proactively boost their company’s cyber resilience levels to avoid threats landing in inboxes in the first place. The fact that a staggering 94% of malware attacks are delivered by email, makes email an extremely important vector for businesses to fortify.
No one vendor can stop all threats, so it’s crucial to remind customers that if they are using Microsoft 365 or G Suite, they should also have a third-party email security specialist in place to mitigate their risk. For example, using a third-party cloud email solution like MailGuard.
Talk to us
MailGuard's partner blog is a forum to share information and we want it to be a dialogue. Reach out to us and tell us how we can serve you better. You can connect with us on social media or call us and speak to one of our consultants.
Australian partners, please call us on 1300 30 65 10
US partners call 1888 848 2822
UK partners call 0 800 404 8993






