In the closing days of 2019, while many of us are winding down, cybercriminals continue to probe inboxes with a myriad of email stings designed to catch us unaware.
In the past week, MailGuard has intercepted several smaller and less common email threats, along with some larger scams from the usual suspects like PayPal and Netflix impersonators, as reported in separate posts.
Two such scams were impersonating email and marketing tech firms MailGun and HubSpot, while another was masquerading as Amazon Web Services. Each of the scams makes reference to a payment due.
The fraudulent HubSpot scam is hoping that recipients are employed by one of the 68,800 customers of the marketing technology giant. HubSpot, which is listed on the NYSE claims to have customers in more than 100 countries. The email which leverages authentic HubSpot branding, carries the subject ‘Action required: Update your payment information now’ with a sender display name of ‘HubSpot <noreply[@]hubspot.com>’ while the actual sending address is ‘no-reply[@]west-sales.com.’
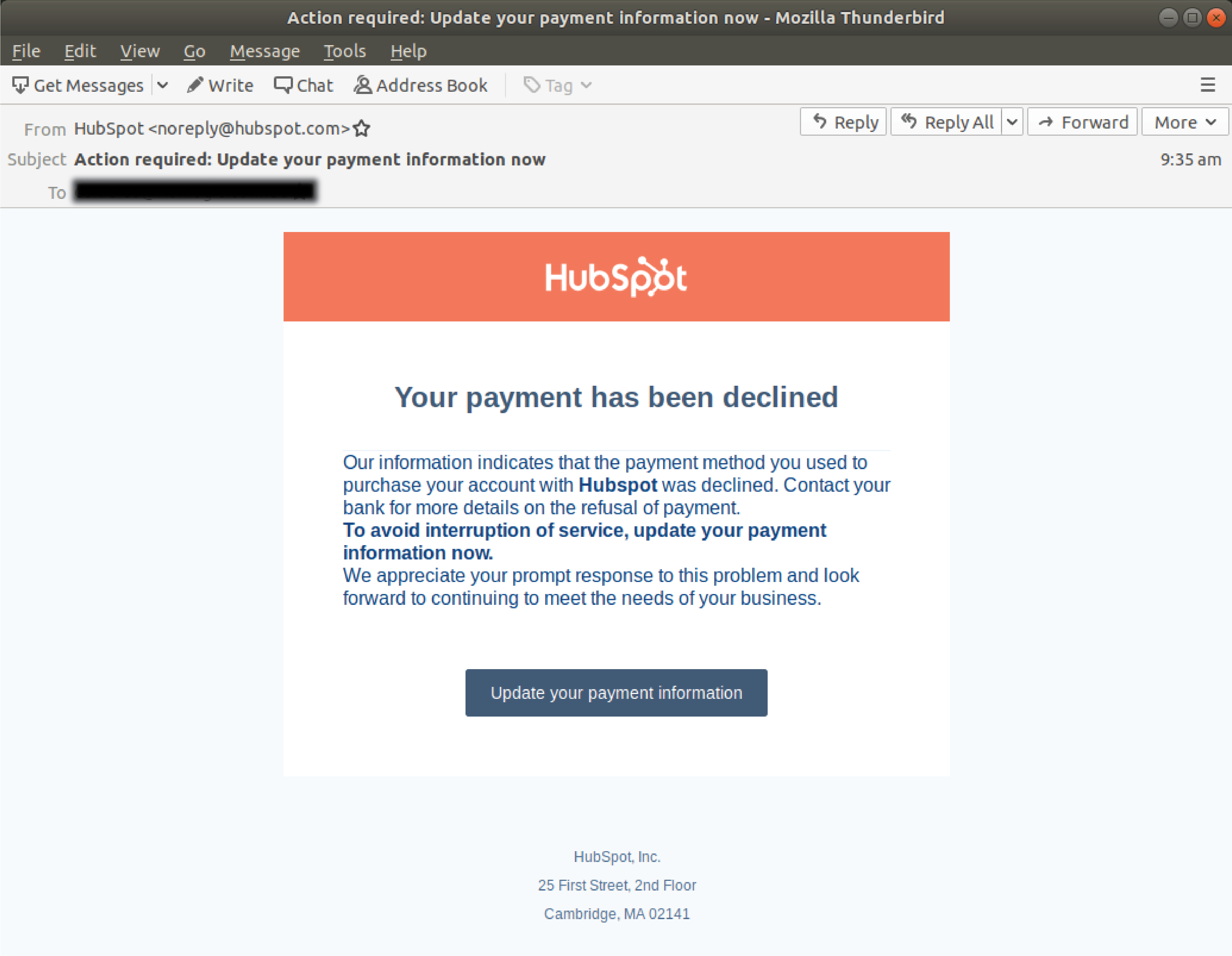
The email contains a phishing link that directs those who click through to a fake HubSpot login landing page.
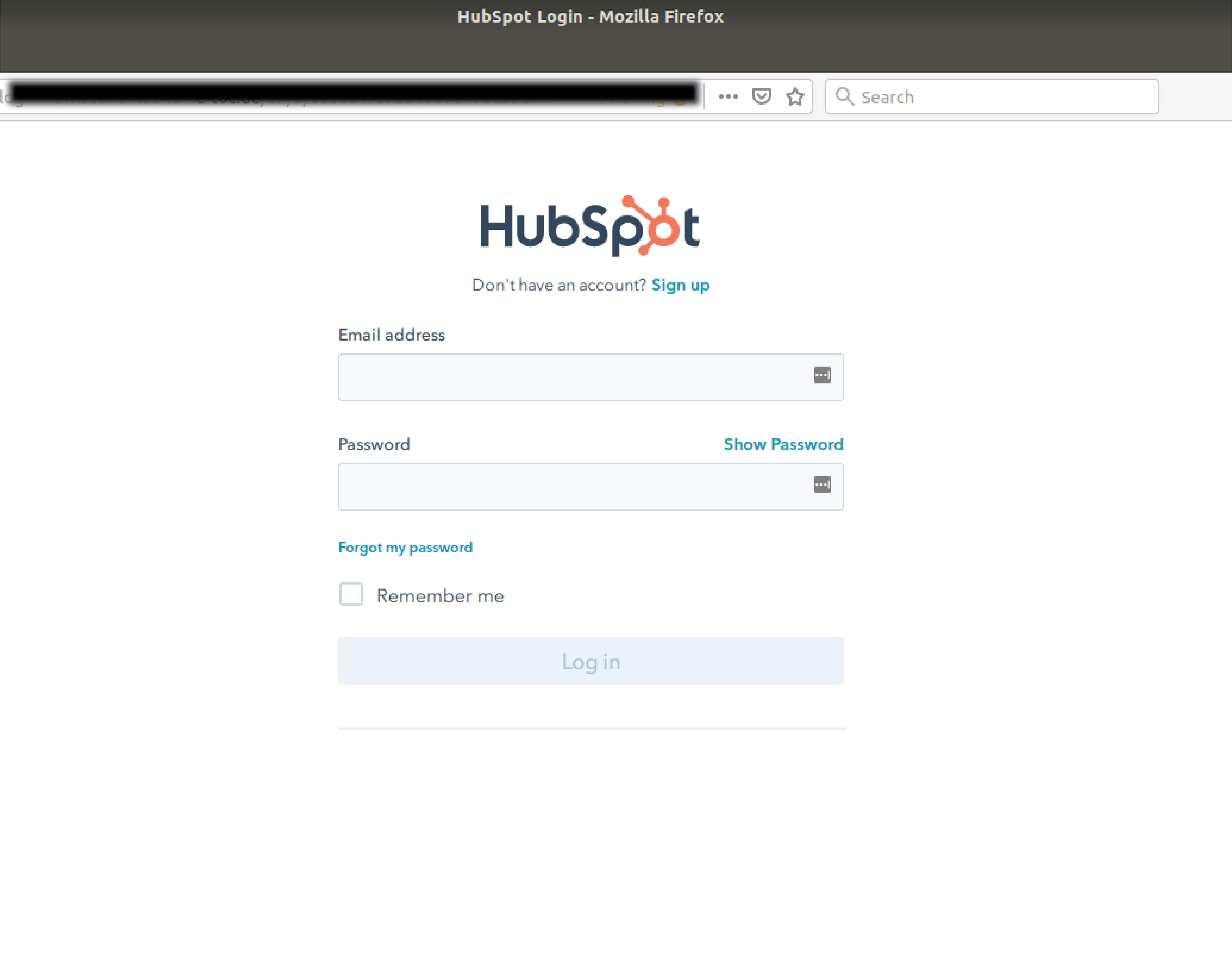
The scam is designed to steal the login credentials of the user, and if successful will also yield access to the sensitive customer data associated with a victims HubSpot account.
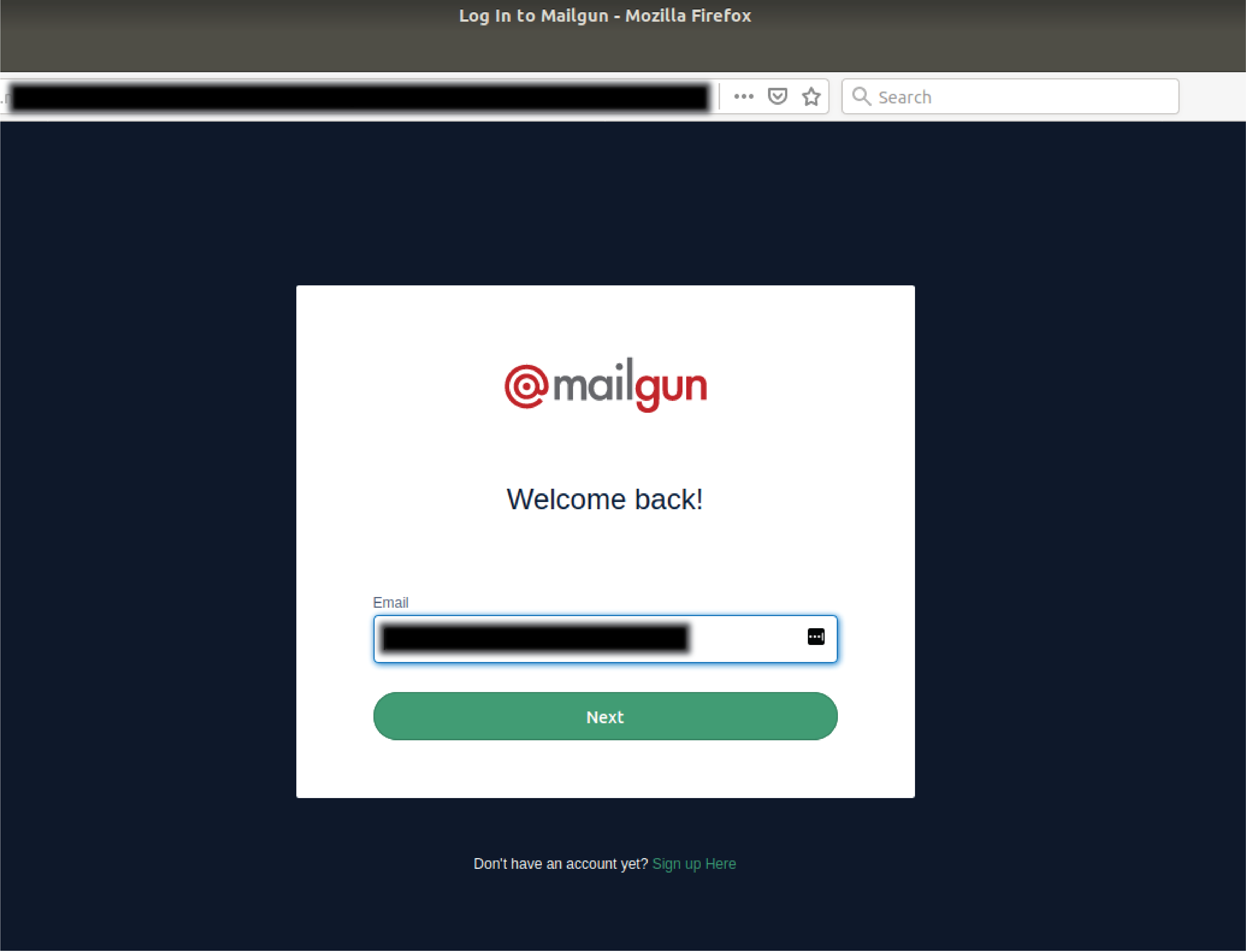
The MailGun scam operates with a very similar approach, again pretending to deliver an invoice requiring payment from the Texas based tech firm. With the subject ‘New invoice has been created for your account’ the display name is a convincing ‘MailGun <invoice[@]mailgun.com’ while the actual sending email address is ‘no-reply[@]klakan.xyz.’
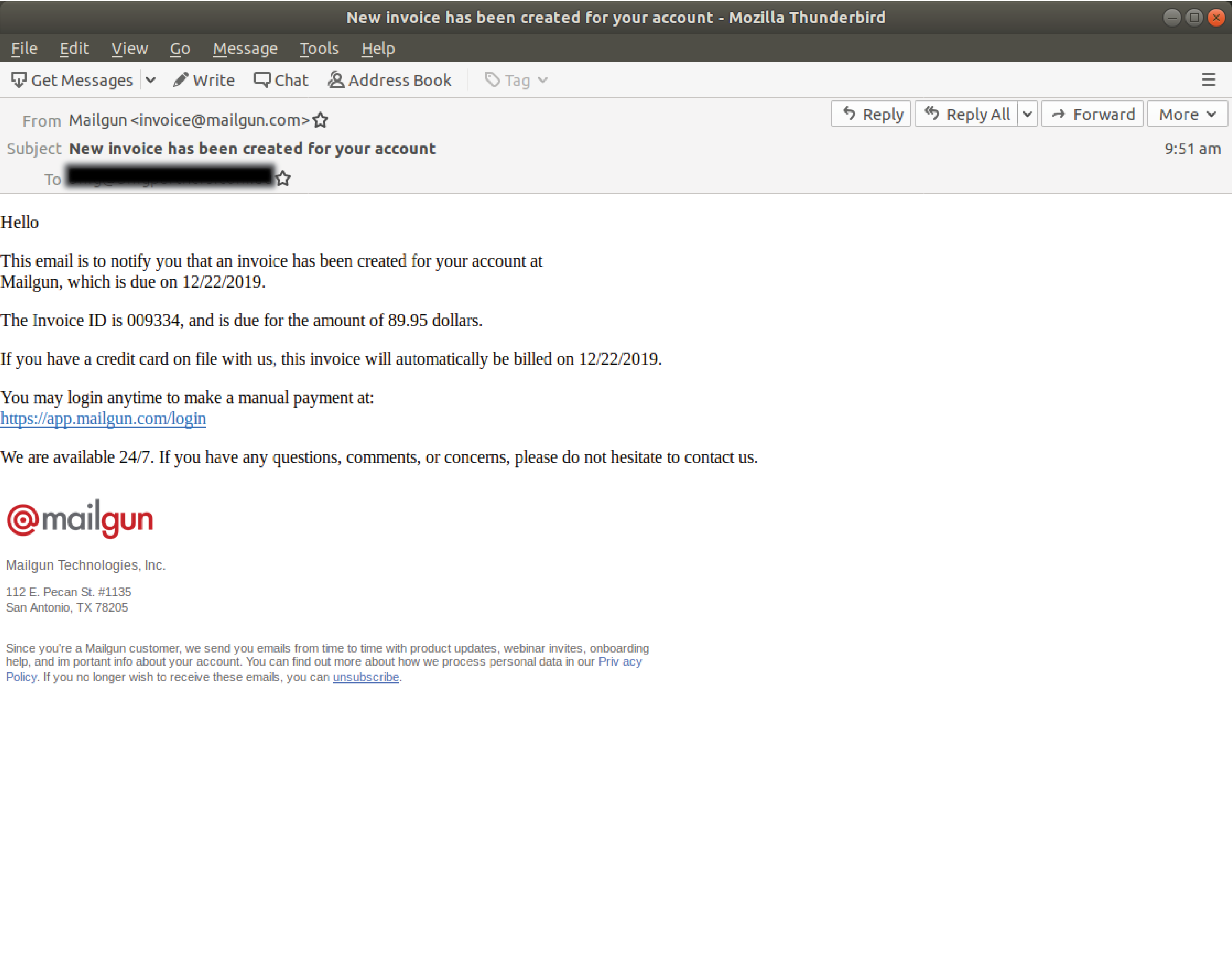 A relatively simple attack, none of the message contents vary with every one of the HTML emails carrying the same invoice numbered ‘009334’ with a due amount of ‘$89.95.’ The phishing link in the email directs recipients to a login page designed to steal user login credentials like their username, and on a following page their password. The fraudulent password page displays an error once completed and re-directs users to the legitimate MailGun login page.
A relatively simple attack, none of the message contents vary with every one of the HTML emails carrying the same invoice numbered ‘009334’ with a due amount of ‘$89.95.’ The phishing link in the email directs recipients to a login page designed to steal user login credentials like their username, and on a following page their password. The fraudulent password page displays an error once completed and re-directs users to the legitimate MailGun login page.
In the final Amazon Web Services scam, the email is titled ‘Amazon Web Services Billing Statement Available’ with a display name of ‘no-reply-aws[@]amazon.com’ however the actual sending email address is ‘no-reply[@]nger.xyz.’
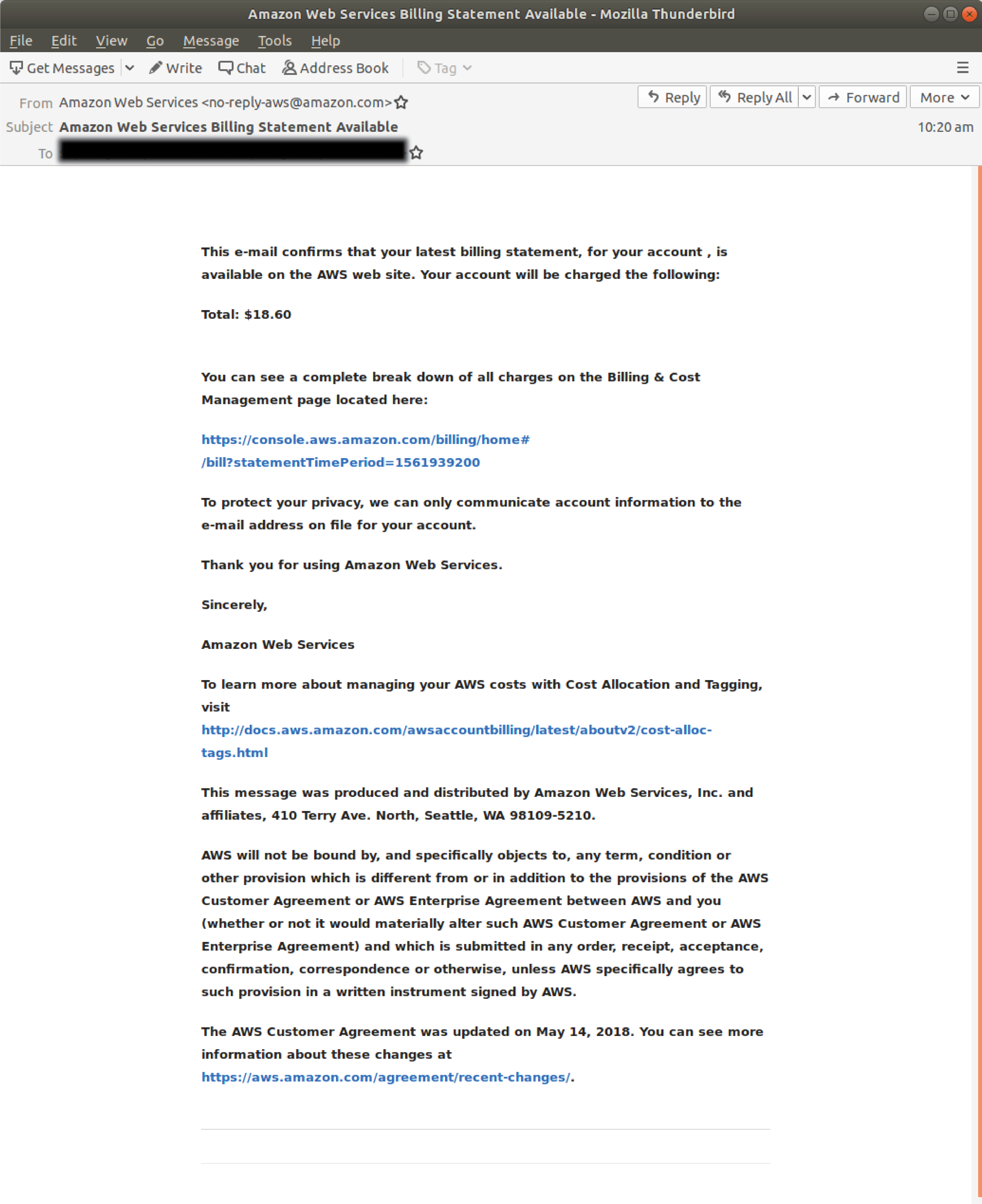
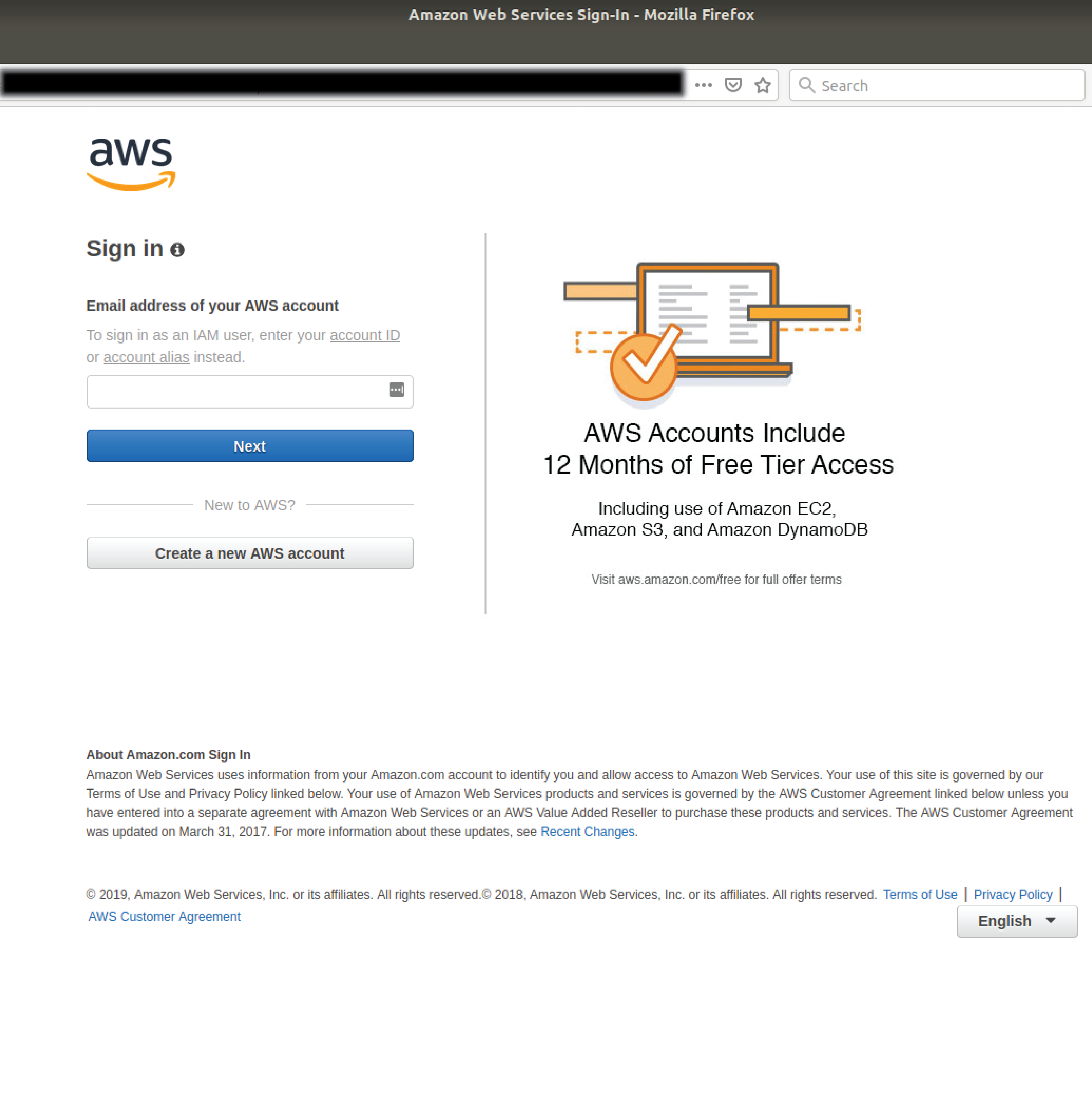
The email informs recipients that their latest billing statement is available on the AWS website with an amount that will be charged to their account. Unsuspecting recipients who click through on the phishing link are directed to a convincing AWS login page where they are prompted for account credentials including their username and password.
Cyber-criminals frequently exploit the branding of reputable companies because their good reputations lull victims into a false sense of security. Because of the large number of customers that these firms have, along with the sensitive account credentials of victims and the potential to yield large volumes of customer data, they are attractive targets.
Phishing continues to be one of the most prevalent forms of cyber-crime. The vast majority of online scams - more than 90% - are perpetrated using email, so it’s wise to always be skeptical of messages from unfamiliar senders asking you to log into your accounts.
Phishing attacks can be enormously costly and destructive, and new scams are appearing every week. Don’t wait until it happens to your business; protect your business and your staff from financial and reputational damage, now.
What to do if you receive a suspicious email
As a precaution, avoid clicking links in emails that:
- Are not addressed to you by name, have poor English or omit personal details that a legitimate sender would include
- Are from businesses you’re not expecting to hear from.
- Ask you to download any files
- Take you to a landing page or website that does not have the legitimate URL of the company the email is purporting to be sent from.
Don't get scammed
If your company’s email accounts aren’t protected, emails like the one above are almost certainly being received by your staff. Cybercriminals know people can be tricked; that’s why they send out millions of scam messages and put so much effort into making them look convincing.
People are not machines; we're all capable of making bad judgement calls. Without email filtering protecting your business, it’s just a matter of time before someone in your organisation has a momentary lapse of judgement and clicks on the wrong thing.
One email is all that it takes
Cybercriminals use email scams to infiltrate organisations. All that it takes to break into your business is a cleverly-worded email message. If scammers can trick one person in your company into clicking on a malicious link they can gain access to your data.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive and advanced email security.
Talk to a solution consultant at MailGuard today about securing your company's network.
Why not stay up-to-date with MailGuard's latest blog posts by subscribing to free updates? Subscribe to weekly updates by clicking on the button below.







