A malicious email spam campaign has held businesses for ransom after downloading an email attachment purporting to be from Microsoft.
MailGuard has successfully identified and quarantined all instances of the recent ransomware email scam, protecting our clients from loss of critical business data.
Windows users considering upgrading to Windows 10 are the new target for cyber criminals, leveraging the brand to trick email recipients with a zero-day malware exploit. The hackers, claiming to be from Microsoft, are pretending to offer quicker access to the new Windows 10 operating system.
Here is a screenshot of the type of email to watch out for.
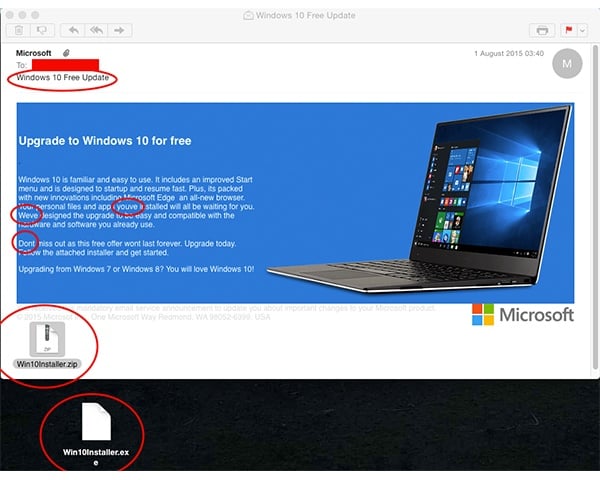
As you can see, the email appears to originate from Microsoft, exciting the victim about the prospect of immediate access of the new operating system. The email maliciously holds the recipient’s hand as they are guided down a simple installation path to encrypting their device.
An immediate warning sign is the manner in which the update is distributed; via an unsolicited email. Microsoft are adamant that its update mechanism prompts users with a notice on their screens when a download is available. This scam takes advantage of the trusting nature of excited users that would otherwise need to wait in line prior to receiving a Windows 10 update from Microsoft.
The email is addressed to the recipient personally, and as a result, doesn’t appear to be mass email spam.
The content of the email is competently written, and despite a number of grammatical errors doesn’t arouse any further suspicion from the user.
The wave of bogus spam emails are sent containing a malicious .zip attachment concealing an executable ‘ransomware’ file. The encryption used in the ransomware is known as Elliptic Curve Encryption (EEC), a lightweight encryption method intended to block access to your data as quickly as possible.
Once unzipped, if the .exe file is executed, the program encrypts and locks data on all local and mapped drives, finally demanding payment to release access. This particular scam contains a CTB Locker, a CryptoLocker variant.
What’s worse is that it is difficult for antivirus software to detect, often delivered as a .zip file hiding within another .zip file. Once infected, a notice appears demanding ransom within 96 hours to decrypt business files.
As reported by the ABC, the ransom is demanded in a payment made via Bitcoin using the anonymity network, Tor. This makes the transaction “virtually untraceable” and allows the malware distributor to quickly profit. Cyber criminals are targeting businesses that cannot afford the loss of productivity in the “weeks [it takes] for them to work out how to decrypt the files”.
This scam has arrived in a number of variations, ensure you are wary of any unsolicited emails purporting to be from Microsoft boasting faster access to Windows 10 or offering free updates.
Our Advice:
- Don’t open files or click links from unsolicited senders. Whilst this particular email did not come in the form of a phishing scam prompting users via an outbound link, it’s important to remain vigilant in what you click on and download onto your computer and in turn your corporate network.
- Ensure you keep frequent backups of your data. If your hard drive becomes encrypted, it’s a much easier rectification process if you are able to revert back to a recent backup.
Educating staff and employing multilayered defences including desktop antivirus, anti-malware, anti-spyware, and using cloud-based email filtering and web filtering will go a long way to mitigating the risk from a wide range of email scams.
Here's what a legitimate Windows 10 upgrade looks like.
A notification in your taskbar from Microsoft.

Once clicked, the following application launches prompting you with a free upgrade to Windows 10.

Keep up to date on the latest email scams by subscribing to MailGuard’s weekly update or follow us on social media.







