A sophisticated new QuickBooks scam is circulating targeting businesses that appear to be largely in the mining and resources sector.
The scam is carefully socially engineered, matching the email recipient with companies in their sector, and attaching a fake QuickBooks invoice with a request for payment. QuickBooks is a well known online accounting software, so the scammers are leveraging awareness of the QuickBooks brand to deliver the malware.
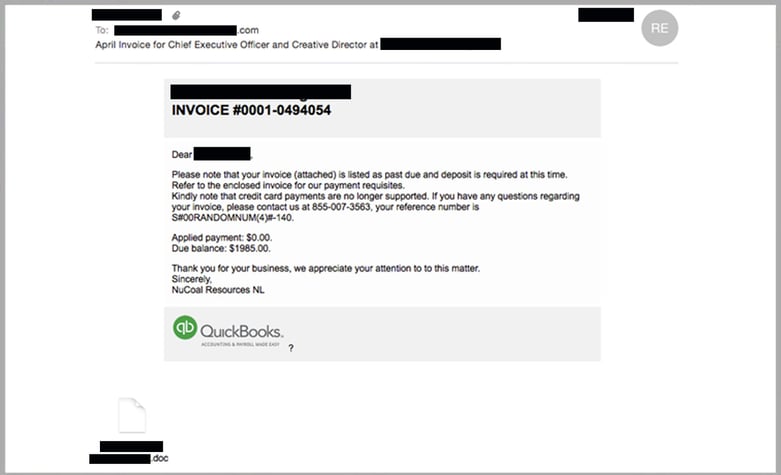
The email appears to be from a generic person, who in the sample below, works at a well-known Australian company in the mining & resources sector. Thousands of legitimate companies are being leveraged in the scam, and while the majority appear to be in Mining & Resources, or related sectors like Construction and Engineering, there are other companies being used that are in unrelated fields like Education.
What is interesting is that we are seeing the cyber criminals addressing the emails personally to the intended recipient, and naming the file/attachment with a legitimate local company name. Typically when spammers have details such as individual names and the companies they work for, it means that trojans installed on other peoples machines have stolen information out of their address books, and used that data to send the emails. This also means that potentially those trojans have also stolen the content of the emails themselves.
MailGuard identified and blocked the scam email which is delivering malware to its recipients. MailGuard are consistently between 2 hours and 48 hours ahead of the market in preventing these never seen before or zero-day attacks. Most on-premise or hybrid anti-virus vendors require software updates across multiple instances, which can take hours or even days, leaving clients vulnerable.
Here is a sample of one out of the thousands of emails delivered yesterday:
By opening the attachment within the email and enabling the macros, the recipient is allowing the delivery and installation of Trojan malware. The malware also installs a server on your machine so that the attackers have direct control over your computer.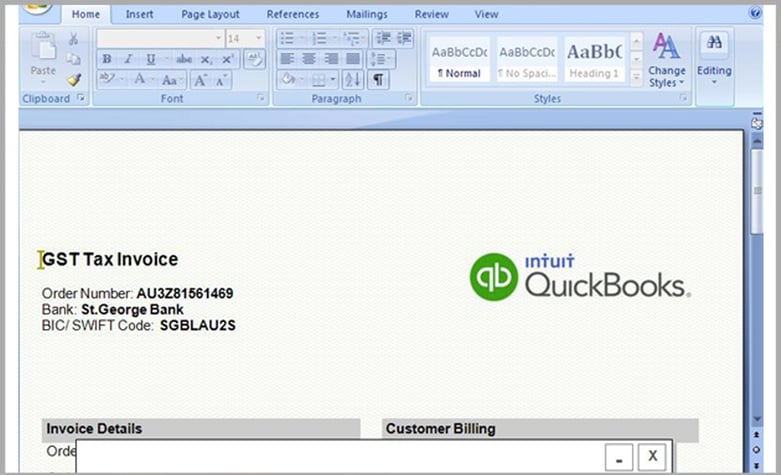
Why is Trojan malware dangerous?
Trojans sit quietly in the background, and will take actions not authorised by the user, such as modifying, stealing, copying or even deleting data.
This type of malware is most dangerous because the user may not notice it running in the background until such time they are made aware – this can sometimes be weeks or even months after the event.
The fact that a server is also installed on the machine means other criminal activities can be initiated from the machine on behalf of the criminals.
How can I protect myself from these types of email scams?
To reduce the risk of being tricked by one of these scams, you should immediately delete any emails that:
- Seem suspicious and ask you to download files or click any links within an email to access your account.
- Are purporting to be from businesses you may know and trust, yet use language that is not consistent with the way they usually write (including multiple grammatical errors)
- Ask you to click on a link within the email body in order to access their website. If unsure call the company/person directly and ask whether the email is legitimate
We recommend that you share these tips with your staff to make them aware of these campaigns. By employing a cloud-based email and web filtering solution like MailGuard, you’ll also reduce the risk of these new variants of malicious email from entering your network in the first place.
Keep up to date on the latest email scams by subscribing to MailGuard’s weekly update or follow us on social media.







