Australians are being hit by many variations of phishing email scams. Today MailGuard identified and blocked scams purporting to be from Australian Recoveries & Collections (ARC).
We have seen a number of similar scams fooling email recipients into believing they have received fines from the Australian Federal Police (AFP). This one impersonating the ARC is not so common, however.Any Australians receiving emails purporting to be from the ARC need to be wary.
First to stop NEW attacks, MailGuard is consistently between 2 hours and 48 hours ahead of the market in preventing fast breaking attacks.
Most on-premise or hybrid anti-virus vendors require software updates across multiple instances, which can take hours or even days, leaving clients vulnerable.
Here is a sample of one of the phishing emails from today that MailGuard has identified and blocked: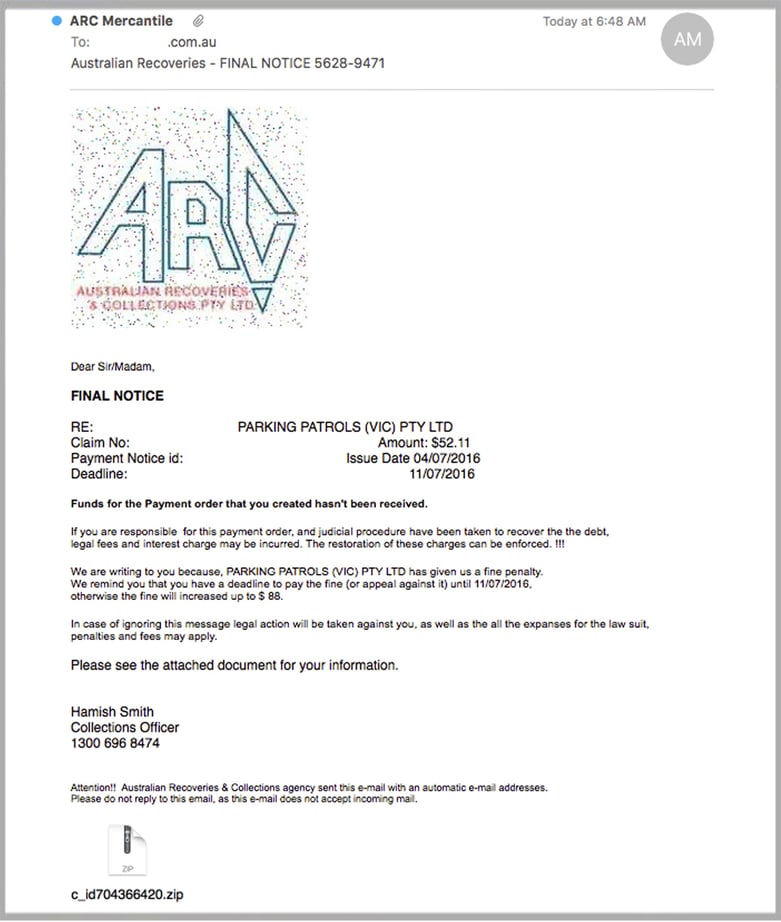
This email is not personally addressed to the email recipient and appears to be sent from several compromised mailboxes. The ‘from’ name in this instance has been obfuscated to show "ARC Mercantile" who are not the senders.
The email plays on fear and curiosity, making the email recipient believe they are being chased for outstanding payments. The email asks the recipient to open the attached .zip file in order to view information about the supposed ‘fine’. Enclosed within is a JScript file which when executed, downloads a Trojan.
Normally it would be straight forward for anti-virus engines to pick up this type of threat, however the attackers have messed up the header of the .zip file by adding in extra characters. This makes it difficult for virus engines to pick up the type of file as a .zip archive and they fail to extract and scan the malware successfully.
Though the attack vector is similar to phishing emails we've seen in the past, the content of this email is different and cyber criminals have played around with the headers of the .zip archive making it difficult to detect.
Why is this type of email scam dangerous?
By clicking and running the executable files, you are allowing malware to be installed in the form of a Trojan.
Trojans sit quietly in the background, and will take actions not authorised by the user, such as modifying, stealing, copying or even deleting data.
This type of malware is most dangerous because the user may not notice it running in the background until such time they are made aware – this can sometimes be weeks or even months after the event.
Please make email users in your company aware of this new phishing scam and advise them to look out for suspicious emails purporting to be from legitimate organisations.
Keep up to date on the latest email scams by subscribing to MailGuard’s weekly update or follow us on social media.






