Confidential business documents such as contracts, legal documents and finance records are commonly passed on from one recipient to another via email. But how can you tell if links to such important documents are safe to click when they appear in your inbox?
That question became all the more pertinent when MailGuard detected a new phishing email scam infiltrating inboxes on 10th of December 2019 afternoon (AEST). Using a display name of "WeTransfer", the email actually came from one of several malicious senders.
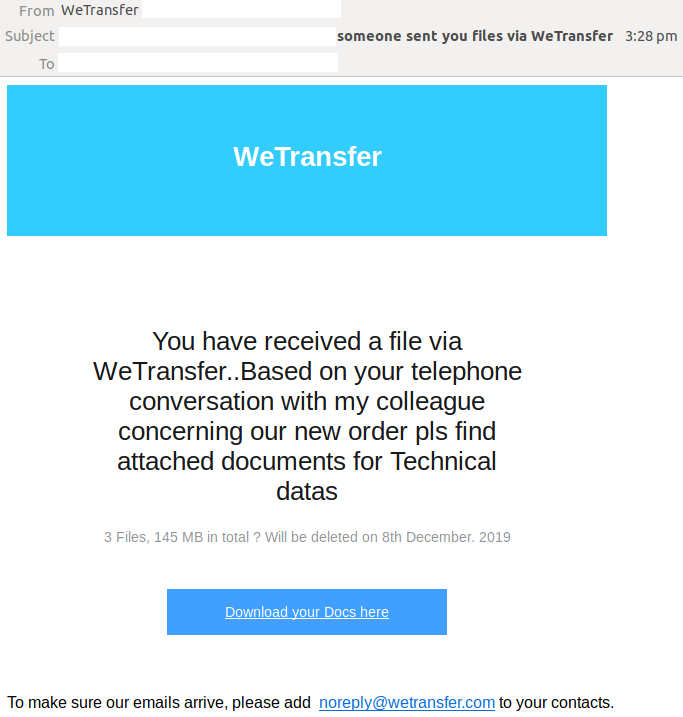
The email body is poorly formatted, with a blue banner containing "WeTransfer." The message body advises the recipient that they have received a file via WeTransfer. A message about the file then follows. A link is provided to "Download your docs here"
Here is a screenshot of the email:
Unsuspecting recipients who click on the link are led to a fake WeTransfer-branded login page. This is actually a phishing page.
Here’s a screenshot of the page:
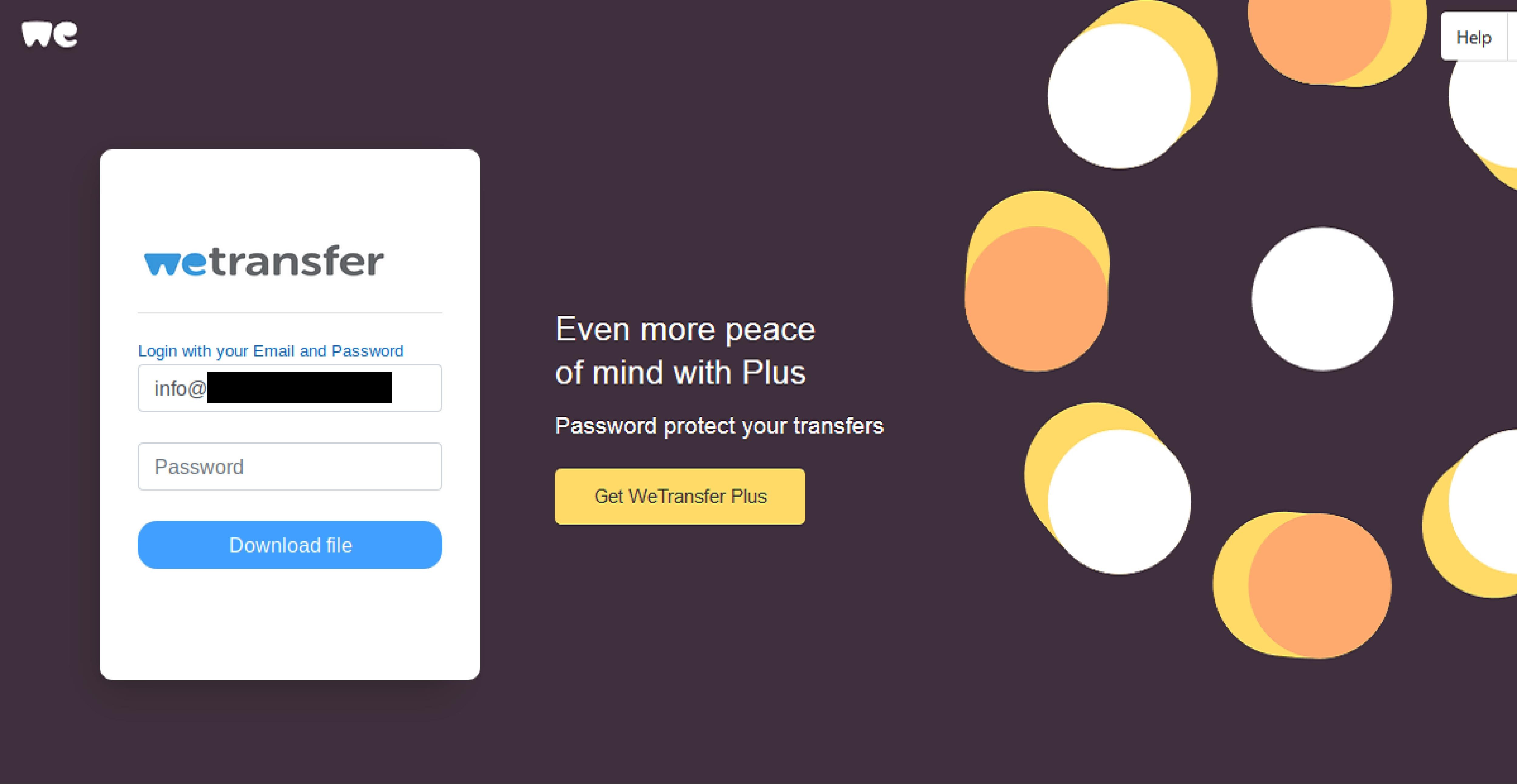
Upon ‘logging in’ and clicking on the link to ‘download file’, users are shown a response stating the password entered is incorrect. The phishing site never moves from this page.
MailGuard urges all recipients of this email to delete it immediately without clicking on any links.
Several techniques have been employed in this particular email to look like a genuine notification, including the usage of high-quality graphical elements in the phishing page, such as WeTransfer’s branding & logo. All this serves to elicit a more confident response from recipients who think they are, in fact, viewing a document from the popular file-sharing cloud platform.
This email also attempts to intrigue; telling the recipient that a new file has arrived ‘based on your telephone conversation’ creates a sense of curiosity. This motivates the recipient to click on the provided link right away, distracting them from checking the sending address of the email and looking out for any other errors.
However, eagle-eyed recipients would notice several red flag that point to the email’s illegitimacy. For example, the recipient’s email address is used within the email body and subject. However, no user-specific information is used, such as the recipient’s name. Legitimate WeTransfer emails also typically contain information on the sender of the file, unlike this phishing email. Instead, this email simply states that "someone sent you files via WeTransfer".
What to look out for
As a precaution, avoid clicking links in emails that:
- Are not addressed to you by name, have poor English or omit personal details that a legitimate sender would include (e.g. – tracking ID).
- Are from businesses you’re not expecting to hear from.
- Ask you to click on any suspicious links.
- Take you to a landing page or website that does not have the legitimate URL of the company the email is purporting to be sent from.
Defend your inbox
Even the most experienced and savvy email users can have a moment of haste, carelessness or fatigue when their guard is down. Just practising good common sense isn’t enough anymore, because for scammers it’s a numbers game; they know that if they keep sending their scams, sooner or later we will slip up and do something we shouldn’t.
Speak to the MailGuard team today to learn more how MailGuard's predictive and advanced email security can help protect your business for a few dollars per staff member per month.
Talk to a solution consultant at MailGuard today about securing your company's network.
Why not stay up-to-date with MailGuard's latest blog posts by subscribing to free updates? Subscribe to weekly updates by clicking on the button below.







