We all use passwords. In fact, we need them to access almost any online device. They are the key to retrieving sensitive data, whether it be online banking, classified company documents or social profiles, such as LinkedIn. They’re the first line of defense to protect crucial information, and often the most vulnerable. It’s not surprising then, that cybercriminals often create phishing scams to steal password credentials in order to procure data for use in criminal activity.
As we go about our daily routines, technology is a fundamental and necessary part of our everyday existence. Most of us are not industry experts though, with in-depth knowledge about the inner workings of the tech we rely upon, nor do we consider the risks if it were to fall into the wrong hands, and more specifically the data. So, security concerns and the level of password security may not occur to us. Often, it’s not until after we have fallen victim to a cybersecurity attack that we think about what we need to implement in order to strengthen our defenses.
The same applies to business. When it comes to protecting your business data and user passwords, there are practical measures that can be implemented as part of your security practises in order to try and keep your data safe from unauthorised access. Although these measures aren’t a be all and end all, they will at the very least encourage proactivity with regards to password security within your business. Criminal third-party access to business assets, can not only cause severe financial loss, but also reputational and operational damage to your business, and to the individuals within it. It can take months, or even years to recover from an incident, indeed for some businesses, it can sadly mean the end.
5 ways to improve your password security:
Although the war against cybercrime is complex and forever evolving, there are some simple steps we can take as individuals and businesses to strengthen our passwords, and overall, our security culture. Where we can’t, technology can.
1. Frequently update passwords (and don’t re-use them).
To put it simply, the less often you update a password, the more vulnerable it is. Worse still, re-using passwords is a hacker’s play pen. Whether it’s easier or just more convenient, it’s not uncommon to keep a favourite password for a prolonged period of time. After all, they’re easier to remember. The same goes for re-using the same password for multiple accounts, and cybercriminals know this. So, by changing passwords frequently we give hackers less chance of figuring out our password and stealing our data. It’s merely a process of trial and error for them, and if they hit a pot of gold, they have access to multiple accounts and your sensitive data that can be used for follow on attacks, identify fraud or sold to other criminal enterprises on the dark web.
2. Employ a Password Manager.
Password managers are arguably the most secure way to protect your passwords. To begin with, (most) password managers use AES 256-bit encryption as an industry standard to protect your passwords. That’s military grade encryption. In addition to this, password managers are built using zero-knowledge technology, which means that your passwords are encrypted before they leave your device.
Most password managers, like Last Pass, ask you to use a master password as entry to your vault. Considering that you have created a password that is secure enough, you can rest assured that the passwords contained in your vault are safe. Last Pass also uses multi-factor authentication (MFA) to further protect your passwords. Remember, password managers are in the business of protecting your passwords, therefore the technology incorporates features designed to do just this, including anything from evaluating your password strength, scanning the dark web on your behalf for logins using your credentials and reminders to change your password. They also boost password strength in other ways, for instance, when they’re used for password generation, and in organisations where access needs to be shared across different team members, but where you don’t necessarily want the credentials revealed.
3. Passphrases.
The FBI has recommended that “instead of using a short, complex password, that is hard to remember, consider using a longer passphrase” (ZDnet). A passphrase involves the combination of several words into a long string of at least 15 characters and can often prove to be a strong wall between threat actors and your sensitive information and accounts. Passphrases are helpful when complex, long, unpredictable, and unique.
According to the ACSC (Australian Cyber Security Centre):
“Passwords are passé. It’s time to use passphrases instead. As we have increased our reliance on passwords, adversaries have developed increasingly sophisticated ways to crack them. In attempting to make passwords stronger, we have made them harder for humans to remember, and easier for machines to crack. Hence, the need for passphrases that are easy for humans to remember, and harder for machines to crack”.
Find out more about how to create a passphrase here: https://www.cyber.gov.au/acsc/view-all-content/publications/creating-strong-passphrases
4. Using Single Sign-On.
According to The 2020 State of Password and Authentication Security Behaviors Report, “individuals re-use passwords across an average of 16 workplace accounts and IT security respondents say they re-use passwords across an average of 12 workplace accounts.” It goes on to note that “over half of individuals share passwords with colleagues to access business accounts”. Preventing password re-use can be difficult, which is why one password that goes across many apps can help decrease the risk of this occurring. Single Sign-On (SSO) is helpful because it reduces the number of attack surfaces because users only log in once daily with one set of credentials. Reducing login to one set of credentials improves enterprise security. When employees must use separate passwords for each app, they usually don't.
5. Mandate Multi-Factor Authentication (MFA).
MFA is an added layer of security for each online platform or account that you may access (that requires a username and login). The first layer is a combination of a username and password (this is where password hygiene is very important), and then MFA (or sometimes referred to as Two Factor Authentication (2FA)), is an extra security blanket that further validates your identity and makes it very difficult for a third party to access your data.
While they may access some or all of your data via a compromised service, criminals ability to make changes or to get access to services and data are severely reduced if they don’t have your paired device. Furthermore, you will generally receive notifications of activity on the account, alerting you to the fact that someone unauthorized may be attempting access.
Using MFA can help to reduce the impact of fraud, data loss and identity theft. In 2020, Marriot suffered a data breach of 5.2 million guests which could’ve been prevented by MFA. Don’t let it happen to you.
Multi-Factor Authentication is a must. If a password is stolen, MFA may be the best defense against fraudulent logins. MFA types include the following (by increasing levels of security):
- One Time Passwords (e.g. SMS/phone)
- App Generated Codes (that pop up on a given app)
- Authentication Apps (e.g. Google Authenticator)
- Physical Keys (e.g. swipe cards), and
- Biometrics (e.g. fingerprints)
For best practice, mandate MFA across all access points - devices, apps, networks, cloud. You may also consider Adaptive MFA, where contextual info like device or IP information are used to determine whether to ask for secondary credentials.
More recently, the ASCS has endorsed using MFA for added protection for individuals and businesses alike, advising that “businesses should implement Multi-Factor Authentication as soon as possible to ensure that their data is protected”.
“MFA offers significantly more powerful security and protection against criminals”. They might manage to steal one proof of identity such as your PIN, but they still need to obtain and use the other proofs of identity to access your account. https://www.cyber.gov.au/mfa
Is your organisation prepared to mitigate the threat of Business Email Compromise (BEC)?
These 5 password best practices are important to keep your business data and users safe, but there are other ways that cybercriminals attempt to secure credentials. The news cycle is full of stories about ransomware attacks, such as the Colonial Pipeline attack, and data breaches impacting businesses and lives. But do you know how attackers are getting into systems in the first place? A lot of the time, it’s through stolen credentials. And attackers can steal those credentials, including passwords through an unassuming email.
Head of the Australian Cyber Security Centre, Ms Abigail Bradshaw CSC, reports that “In 2019-20 financial year there were 4,255 reports of BEC scams reported through the ACSC’s ReportCyber tool, representing losses of over $142 million.” Just like other industries, cybercrime is evolving too. Email scams are all pervasive and becoming harder to spot with the naked eye. One of the most common forms, is where an email lands in your inbox impersonating a well-known business. It looks legitimate, so you click a link, which takes you to a website asking you to fill in (or update) your credentials.
We see it every day, caught in our filters at MailGuard:
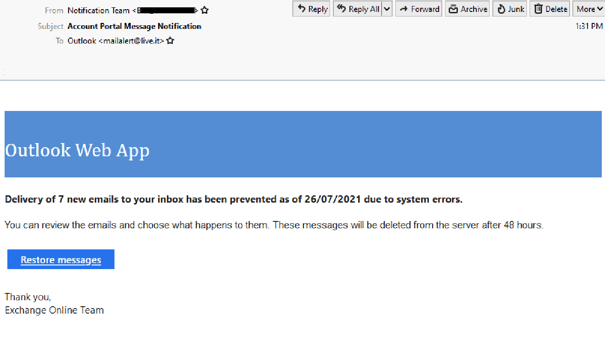
This above example is purportedly from Microsoft Outlook. It’s clever in that the sender’s email domain - live.it - looks a lot like a Microsoft live.com email domain. However, clicking on the link takes you to a weebly.com address, which is not a legitimate Microsoft address. If you enter your Outlook credentials on the site, then they have just been stolen. For businesses without the right password protocols in place, this set of login details can then be used to access their systems.
The cybercriminals will either use these details themselves or now, more commonly, on-sell them from the cost of just a few dollars on the dark web. For instance, researchers found a listing for “VPN/RDP access for three computers at a U.S. company with annual revenue of $300,000 at a starting price of $1,000.”
While MailGuard can help catch these emails before they get to inboxes, good email security is important as an added layer of secure alongside best practice password procedures, to ensure passwords are highly secure for an extra layer of security. For instance, with SSO and MFA in play, if your employees’ credentials are stolen and used in an attack, they will be of limited use against your organization.
HaveIBeenPwned?
Another tip, to see if an email address or phone number has been involved in any known data breaches, is to visit the free tool HaveIBeenPwned. If a data breach has occurred that includes a leaked password, and that password has been re-used (or a similar configuration used) anywhere, it must be changed across all the accounts. Encourage all employees to check all business and personal emails for compromised accounts.
MailGuard helps keep BEC and other email scams out - before they have a chance to steal passwords.
Cybercriminals are always looking for vulnerabilities. Keeping your inboxes safe with MailGuard is just one of the ways that you can keep your team safe. Good password hygiene is another - email lures are the most popular avenue for attackers to steal credentials, but they are not the only one. MailGuard catches emails that are designed to elicit passwords for criminal intent.
Stop phishing emails before cybercriminals even have a chance to steal your employee’s credentials.
Nine out of 10 cyber-attacks start with an email, even when most businesses have an email security solution in place. Precisely because email is a critical tool and arguably the most important means of communication among many businesses, it is imperative for businesses to consistently review their email security strategies to ensure they’re doing all that they can to stay safe. No one vendor can stop all threats, so don’t leave your business exposed. If you are using Microsoft 365 or G Suite, you should also have third-party solutions in place to mitigate your risk. For example, using a specialist cloud email security solution like MailGuard to complement Microsoft 365. For more information about how MailGuard can help defend your inboxes, reach out to my team at expert@mailguard.com.au.
What other password best practises are you employing in your business to defend your systems and your people against cyber-attacks? Share your thoughts below.







