A large-scale fake email attack is targeting inboxes across Australia today.
This criminal-intent email is trying to trick people into believing that it is from Telstra. This is well executed fake, using a sophisticated HTML design utilising authentic looking graphical elements and layout.
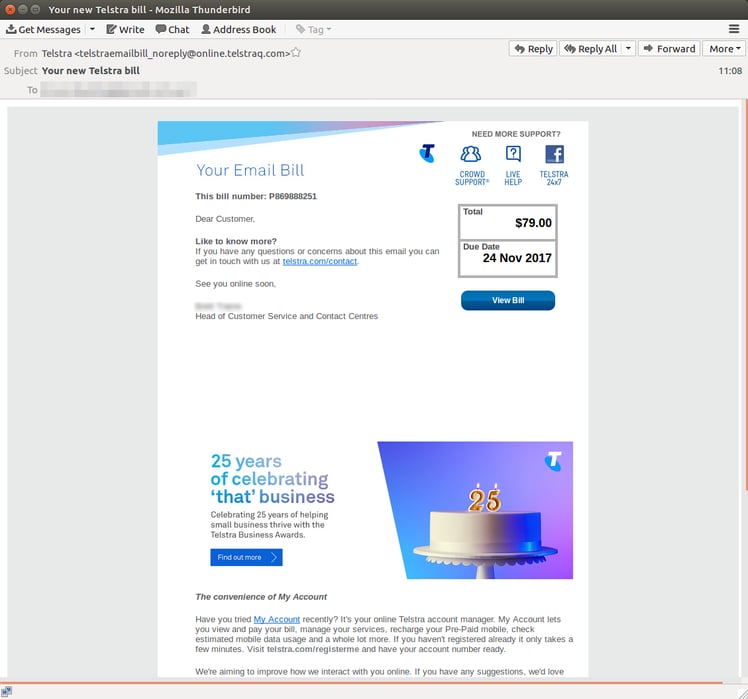 The criminals behind this scam have even obtained a URL to make their email look more convincing. The new domain - telstraq[dot]com - was registered on Sunday 19th Nov in China.
The criminals behind this scam have even obtained a URL to make their email look more convincing. The new domain - telstraq[dot]com - was registered on Sunday 19th Nov in China.
The sender display name ‘Telstra’ on the email header, and the authentic looking sender address; ‘telstraemailbill_noreply[at]online[dot]telstraq[dot]com, give this message a very convincing appearance.
Although this email is completely bogus, the average recipient could easily be deceived into thinking that it is a genuine Telstra communication.
How Does This Attack Work?
 This scam uses a mechanism similar to the fake Energy Australia emails we saw yesterday to ensnare victims.
This scam uses a mechanism similar to the fake Energy Australia emails we saw yesterday to ensnare victims.
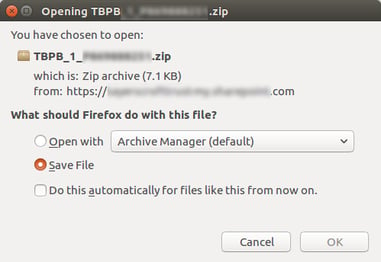
If a recipient clicks on the link in the ‘bill’ email they will be directed to compromised SharePoint site where they will be invited to download a .zip folder. The zip folder contains a malicious JavaScript file that acts as an agent to automatically download malware to the victim’s computer.
JavaScript has Powerful Capabilities
Javascript files (appended with the suffix ‘.js’) usually, contain code elements and these can have significant effects on a computer system. Like files with the suffix .exe, they are a red-flag to us at MailGuard, because they signal that a file which is supposed to be a text document - like a utility bill - actually contains executable code.
It’s a good rule of thumb to never click on email attachments that are hidden in .zip files or have .exe or .js file names.
MailGuard Clients Protected
MailGuard first detected these emails this morning and prevented them from reaching our customer’s inboxes.
At the time we intercepted this email attack, no other security vendors were acting against it.
There are thousands of these emails landing in unprotected inboxes today, so be extremely cautious when checking your email.
Telstra Takes Security Seriously
Telstra has been targetted by brandjacking before, and they caution their customers to verify Telstra emails are authentic. On their support page they advise:
Hoax emails may:
- Be unaddressed, or addressed generically to Dear Customer
- Be badly written with broken sentences, spelling mistakes and grammatical errors
- Show a sender address that is very close to the real company's address
- Display a suspicious looking URL when you hover over links or buttons you're asked to click
- Contain an unexpected zip file or other attachment
Remember: Think Before You Click
All criminals need to steal from you is a cleverly worded email; if they can trick you into clicking on a malicious link they can gain access to your data.
For a few dollars per staff member per month, you can protect your business inboxes with MailGuard's cloud-based email and web filtering security.
Talk to an expert at MailGuard today about making your company's network secure: click here.
Stay up-to-date on breaking scam news. Subscribe to MailGuard's free weekly updates by clicking on the button below:







