A new spin on an old malware scam that we haven’t seen for a while has begun circulating. In what may be the precursor to a larger run, scammers are now revisiting the use of invoice attachments to engage their target.
In recent times, scams have moved away from attachments, instead preferring links as the threat delivery mechanism. This is the first we’ve seen of this scam for a while, with the main difference this time around being the file size which is larger than usual, enabling the email to by-pass many of the spam rules set by web and email filters.MailGuard identified the first malware run with a number of emails that purported to originate from a debtor that the target company has a relationship with.
The email below is an example of a typical attack with a Word document (.docx file) attached:
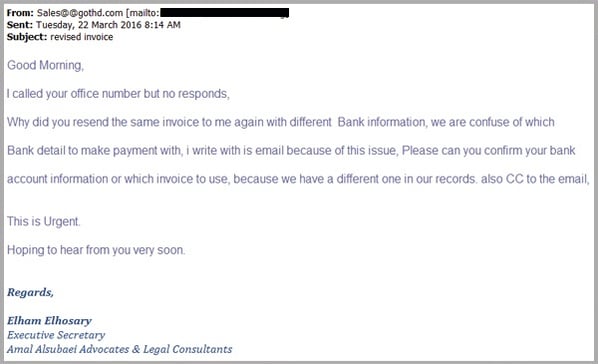
The email appears to be from legal consultancy firm, requesting confirmation as to which bank account details are correct, and which invoice is correct. The aim here is to trick the recipient into clicking and opening the Word documents.
These emails contain .docx as attachments.
The documents themselves contain embedded OLE (Object Linking and Embedding) files which in this case, contain malware. If you have a look at the second screenshot below, you can see the two .exe files attached.
When clicked, malware is installed on your computer in the form of a Trojan.
OLE is a technology that Microsoft invented allowing you to attach documents from other applications into your existing document. For example, you can attach a Word document to an Excel spreadsheet, or in this case, an executable(.exe) file into your Word document.
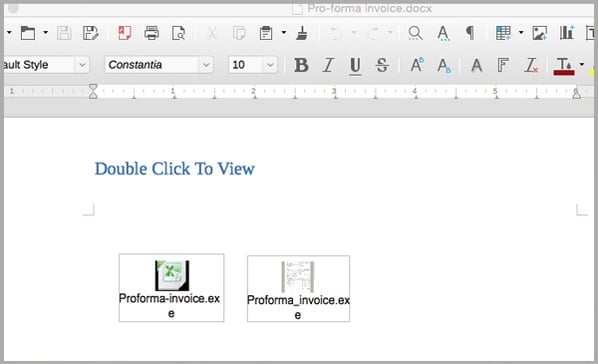
The size of the attachments are quite large – around 2MB each which is unusual for malware contained within emails.
What happens if I open the document and run the .exe files?
By clicking and running the executable files, you are allowing malware to be installed in the form of a Trojan.
Trojans sit quietly in the background, and will take actions not authorised by the user, such as modifying, stealing, copying or even deleting data.
This type of malware is most dangerous because the user may not notice it running in the background until such time they are made aware – this can sometimes be weeks or even months after the event.
How can I protect myself from these types of email scams?
To reduce the risk of being tricked by one of these scams, you should immediately delete any emails that:
- Seem suspicious and ask you to open or download files that you were not expecting
- Are purporting to be from businesses you may know and trust, yet use language that is not consistent with the way they usually write (including multiple grammatical errors)
- Ask you to click on a link within the email body in order to access their website. If unsure call the company/person directly and ask whether the email is legitimate
Help keep your colleagues safe by sharing these tips to make them aware of these campaigns. By employing a cloud-based email and web filtering solution like MailGuard, you’ll also reduce the risk of these new variants of phishing from entering your network in the first place.
Keep up to date on the latest email scams by subscribing to MailGuard’s weekly update or follow us on social media.






