MailGuard has detected a new phishing email scam masquerading as a voice message arrival notification.
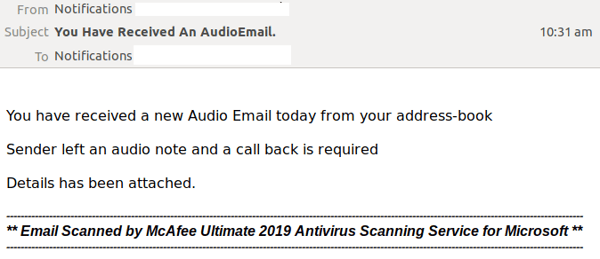
First detected on Tuesday (9th of July 2019), the malicious emails appear using a display name of "Notifications" along with the compromised email address of the sender. They are titled “You Have Received An AudioEmail”. The ‘To:’ field contains the same information as the ‘From:’ field.
The body of the message is in plain-text, and advises the recipient that they have received a new "Audio Email" from their address-book. A call back is required for this audio note, details of which have been attached.
Here is a screenshot of the email:
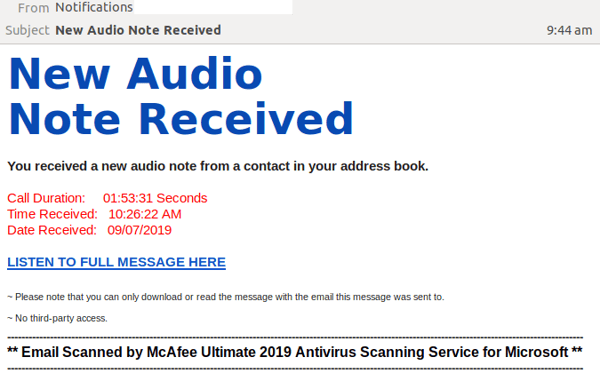
The attachment accompanying the email is another email, which includes some details on the supposed audio note, including its duration, date and the time it was received. A link is included to listen to the full message. The display name, and ‘To:’ and ‘From:’ fields in the attached email are the same as the original email.
Here’s a screenshot of the attachment:
Unsuspecting recipients who click on the link are led to a compromised Sharepoint account, which provides another link to listen to the full message, as per the below:
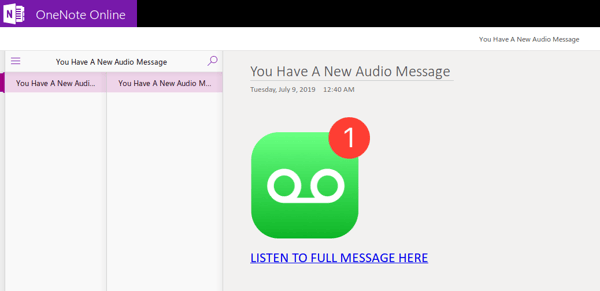
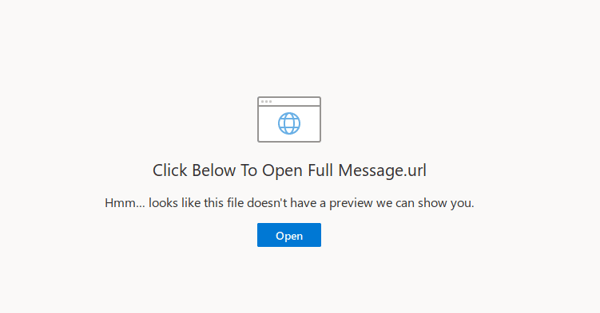
Clicking on the link to ‘listen to full message here’ leads recipients to a OneDrive for business page, stating that the file cannot be previewed and includes a link to open the full file, as per the below:
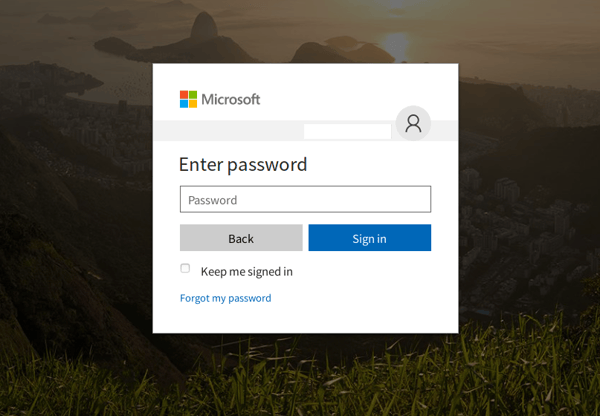
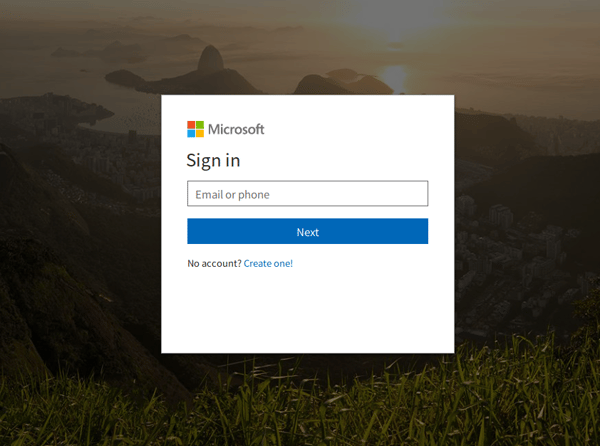
The user is then directed to a phishing page brandjacking Microsoft, which appears as the legitimate sign in page. This page asks for users’ username and password details. Here’s a screenshot of the page:
Once completed signing in, they are finally redirected to the Google voice home page.
An interesting thing to note about the scam is the usage of a footer in both the original email and at the attached email. The footer states that the message has been scanned by a McAfee scanning service for Microsoft. By including this message from a reputed security solution, cybercriminals attempt to raise the credibility of the email in order to convince recipients that it’s safe to click on the included links. In a similar vein, Microsoft’s logo and branding have also been utilised in the phishing pages of the scam using high quality graphical elements – again in order to enhance the authenticity of the email receive.
Despite these attempts, eagle-eyed recipients would be able to identify the inauthenticity of the email due to several red flags. These include the fact that the email body in itself isn’t well-formatted and contains grammatical & spacing errors, such as ‘Details has been attached”.
Whilst MailGuard is stopping this email scam from reaching Australian businesses, we encourage all users to be extra vigilant against this kind of email and whatever happens, do not open or click them.
Phishing continues to be one of the most prevalent forms of cyber-crime. The vast majority of online scams - more than 90% - are perpetrated using email, so it’s wise to always be skeptical of messages from unfamiliar senders asking you to log into your accounts.
What to look out for
As a precaution, avoid clicking links in emails that:
- Are not addressed to you by name, have poor English or omit personal details that a legitimate sender would include (e.g. – tracking ID).
- Are from businesses you’re not expecting to hear from.
- Ask you to download any files or messages, including audio notes.
- Take you to a landing page or website that does not have the legitimate URL of the company the email is purporting to be sent from.
One email
Cybercriminals use email scams to infiltrate organisations with malware and attack them from the inside.
All criminals need to break into your business is a cleverly worded message. If they can trick one person in your company into clicking on a malicious link they can gain access to your data.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive email security.
Talk to an expert at MailGuard today about making your company's network secure: click here.
Stay up-to-date with new posts on the MailGuard Blog by subscribing to free updates. Click on the button below: