Emails are now circulating impersonating UK bank NatWest in an attempt to fool email recipients into handing over online banking credentials.
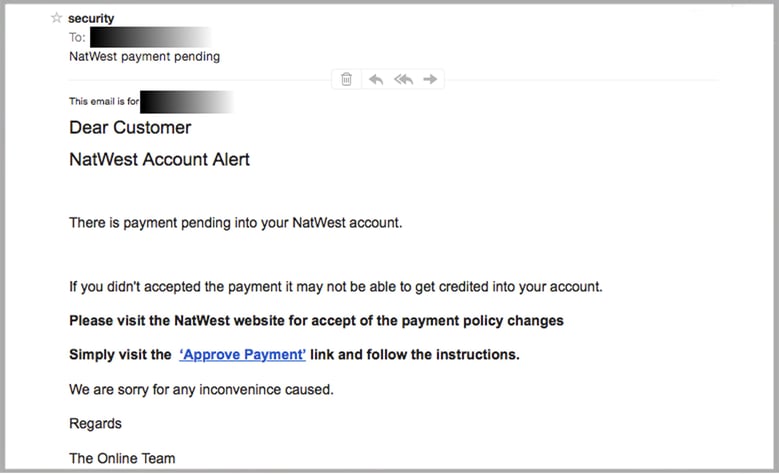
Here is a sample of one of the phishing emails MailGuard extracted from quarantine:
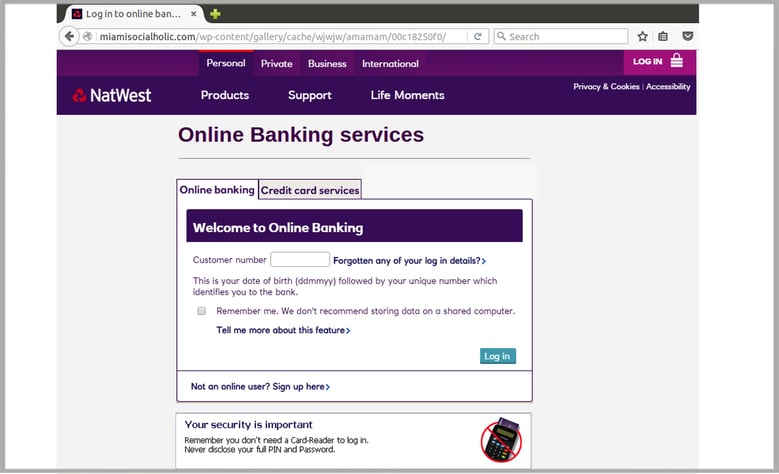
Clicking the link ‘Approve Payment’ takes the recipient to a fake NatWest login page.
Some obvious points to note:
- Banks don't typically require 'authorisation' to accept payments.
- The English used is full of grammatical errors and spelling mistakes which are rarely seen in communications from reputable banks.
- "Dear Customer" is not addressed to the recipient personally. That being said many cyber criminals these days obtain your full name and associated email address from compromised email accounts of people you have contacted. A fall back measure some spammers take is to address you by your email address (greyed out in the image below).
While not visible from the screen captures - this fake NatWest website is actually comprised of static images with the menu items up the top not functional. Sometimes spammers leave legitimate menu links active to increase the likelihood of someone who may be suspicious from leaving the site.
All current browsers will have an icon or status indicator informing the visitor that the website is using an encrypted, verified link. While connecting securely to a site does not guarantee authenticity, banks will always use a secure link at their login portal.
Good practice is to simply not click on a link in an email where you cannot see the entire URL.
Here is the fake login portal accessed over an unsecure link. Note the URL contains /wp-content/, which suggests the site is running a vulnerable WordPress plugin. If you run a blog using WordPress make sure you keep any third party plugins up to date, and frequently visit security sites that post WordPress vulnerability advisories such as https://cve.mitre.org/cgi-bin/cvekey.cgi?keyword=wordpress.
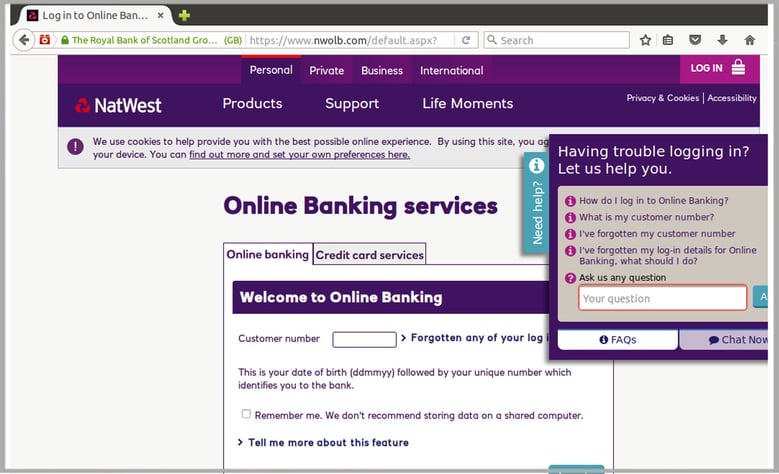
And here is the URL bar of Firefox displaying security information of the legitimate site using verified encryption:
After clicking 'Log in' on the fake site, email recipients are presented with a page asking for their PIN and banking password.
NatWest have employed a technique to prevent banking Trojans that may be lurking on your computer from obtaining your PIN, where you have to physically click on the boxes and enter the digits in a random order. While this is proven as an effective measure against Trojans logging your keystrokes - it won't stop you from putting your details in if you believe this site is authentic. MailGuard recommend a minimum of two factor authentication for sensitive sites.
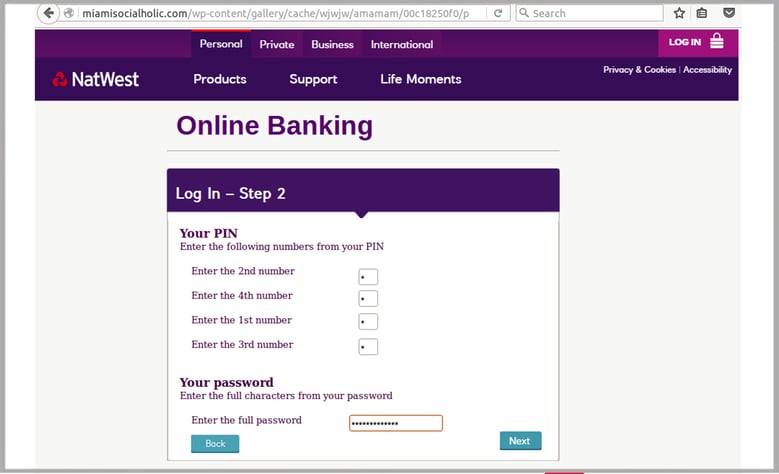
As a final measure the fake website redirects you to the real NatWest website. But notice that there was no option to approve the payment as the email suggests.
Where were the instructions to follow? If you get to this stage and your gut instinct tells you something is wrong - change your banking password immediately and contact the bank.
How can I protect myself from these types of email scams?
To reduce the risk of being tricked by one of these scams, you should immediately delete any emails that:
- Seem suspicious and ask you to download files or click any links within an email to access your account.
- Are purporting to be from businesses you may know and trust, yet use language that is not consistent with the way they usually write (including multiple grammatical errors)
Ask you to click on a link within the email body in order to access their website. If unsure call the company/person directly and ask whether the email is legitimate.
Share these tips with your staff to make them aware of these or other similar campaigns. By employing a cloud-based email and web filtering solution like MailGuard, you’ll also reduce the risk of these new variants of phishing from entering your network in the first place.
Keep up to date on the latest email scams by subscribing to MailGuard’s weekly update or follow us on social media.






