With cybercrime evolving daily, cybercriminals are becoming more and more innovative when it comes to tricking unsuspecting users.
A good example of this is MailGuard’s detection of a new multi-staged phishing email scam spoofing Commonwealth Bank. The hallmark of this scam lies in not only how well-crafted it is, but how it ironically utilises multiple safety features to steal confidential data of users.
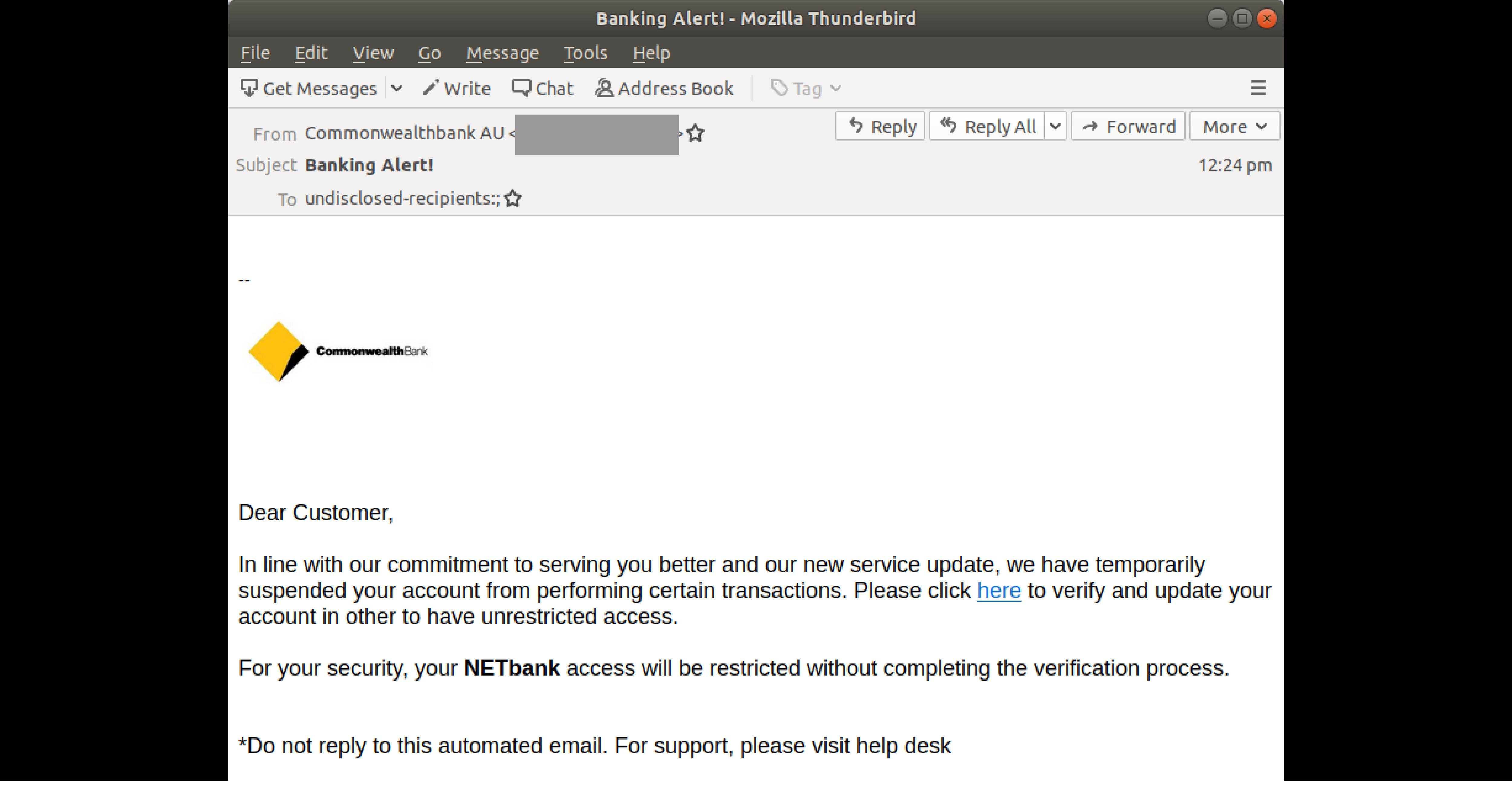
First detected on the afternoon of 12th of September (AEST), this scam uses two different display names: ‘Commonwealthbank AU’ and ‘ASB Bank New Zealand’. The email is, however, sent from the same sending and envelope address. The body of the email informs the recipient that his or her account has been ‘temporarily suspended’ due to a ‘new service update’. The user is advised to verify and update their account in order to ‘have unrestricted access’. A link is provided for the user to do so. MailGuard understands there are three different variants of this link.
Here is a screenshot of the email:
Unsuspecting recipients who click on the link are led to a fake Commonwealth Bank branded phishing page, asking them to log into their accounts, as per the below:
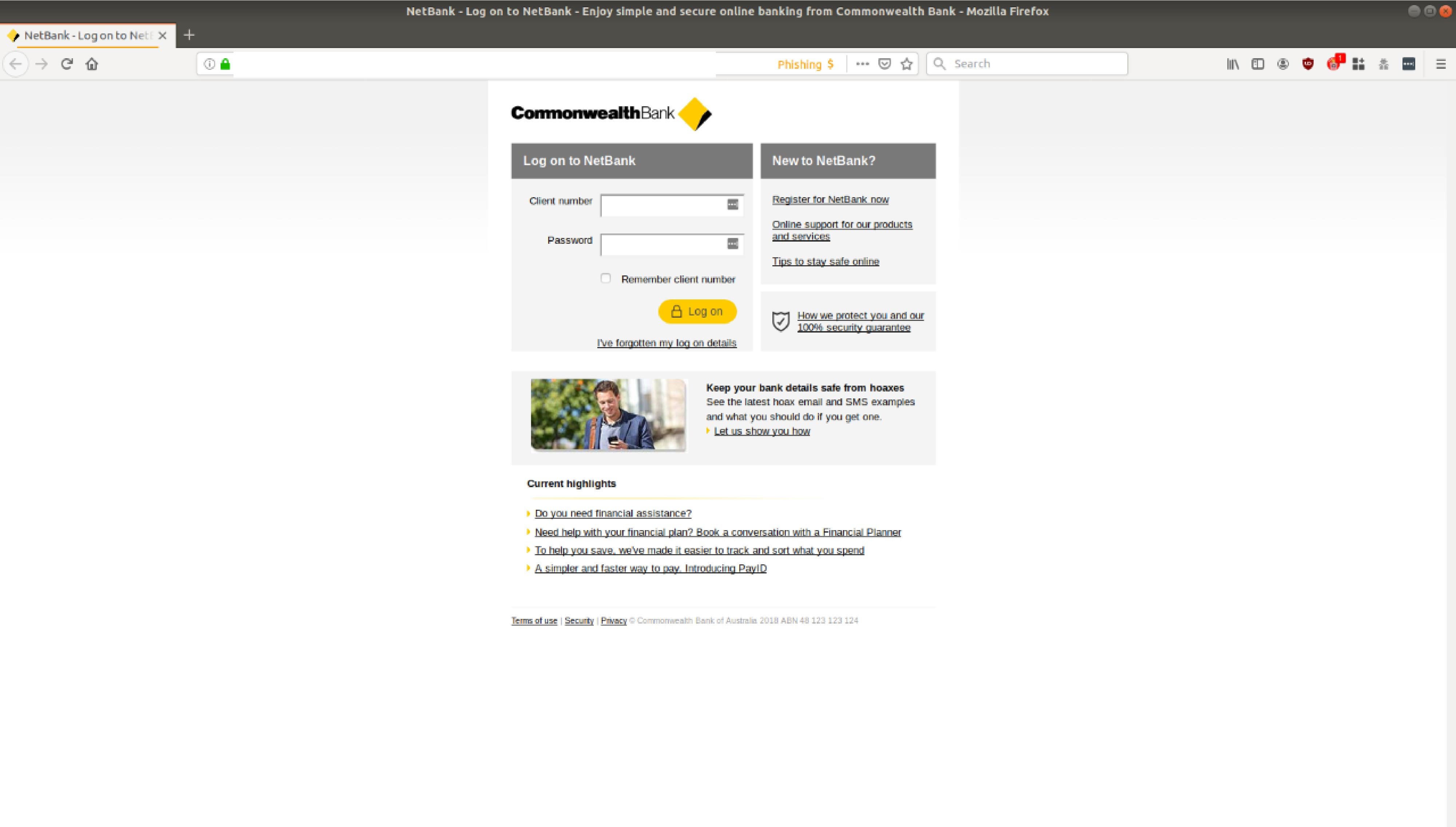
Upon ‘logging in’, users are directed to a page titled ‘NetCode Confirmation’. The page informs them that to ‘ensure security’, users need to enter a ‘Netcode’ that has been set to their mobile phone number. Here’s a screenshot of the page:
.png?width=1656&name=netcode%201%20(2).png)
Clicking the ‘Next’ button to continue the process leads users to a page titled ‘Email Confirmation’. This time, the page requests users to confirm the ‘email address’ that is currently on their ‘profile’.
.png?width=1680&name=netemail%20confirmation%20(2).png)
Following this page, users are asked to verify their identity one more time using a NetCode that has been sent to their mobile number, similar to the ‘Netcode’ titled page above.
This sole purpose of this elaborate phishing scam is to harvest the login credentials of Commonwealth Bank customers so the criminals behind this scam can break into their bank accounts.
As you can see from all the screenshots above, cybercriminals have attempted to replicate official landing pages from Commonwealth Bank – including incorporating the bank’s branding and logo. All this is done in an attempt to trick the users into thinking the scam is legitimate.
It is also interesting to note that the email and the phishing pages are, ironically, focused on securing the users’ banking accounts via ID verification. This only adds on to the sense of legitimacy evoked by the email as updates on account safety is a common notification expected of such a well-established bank. All this serves to elicit a more confident response from recipients who think they are, in fact, making their accounts more secure by clicking on the provided link and entering their confidential login details.
On top of this, this message contains several typical elements of a phishing email:
- use of a major brand name to inspire false trust; the usage of the supposed ‘Commonwealth’ display name boosts the credibility of the email,
- repeated usage of ‘safety features’ typically expected of a well-established bank such as links to avoid hoaxes and bank support numbers,
- false urgency; a subject line such as ‘Banking Alert’ creates a sense of anxiety
To reduce the risk of being tricked by one of these scams, you should immediately delete any emails that:
- Appear to be from a well-known organisation, typically a bank or service provider and are not addressed to you by name and may include poor grammar.
- Ask you to click on a link within the email body in order to access their website – your bank will always ask you to go to their website directly by typing their URL into your web browser address field, as a precautionary security measure.
- Ask you to submit personal information that the sender should already have access to.
Banks commonly hold a well-established and trusting relationship with customers, so when cybercriminals are looking for good trademarks to use in their email attacks they often brandjack banks.
This isn't the only email scam spoofing Commonwealth Bank recently. MailGuard intercepted a phishing attack supposedly from the bank just last week.
Commonwealth Bank offers a comprehensive online resource to help identify and report scams purporting to be from them. You can verify the authenticity of any contact you aren’t sure about, or report phishing, by calling 132 221 or emailing them at hoax@cba.com.au.
If your company’s email accounts aren’t protected, emails like the one above are almost certainly being received by your staff. Cybercriminals know people can be tricked; that’s why they send out millions of scam messages and put so much effort into making them look convincing.
People are not machines; we're all capable of making bad judgement calls. Without email filtering protecting your business, it’s just a matter of time before someone in your organisation has a momentary lapse of judgement and clicks on the wrong thing.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive email security.
Talk to an expert at MailGuard today about making your company's network secure: click here.
Stay up-to-date with new posts on the MailGuard Blog by subscribing to free updates. Click on the button below:







