The ATO and MYOB, regular victims of brand-jacking by cybercriminals, have again been targeted today in large-scale email campaigns. The first ATO-branded email was detected at 8.22am AEST, and the MYOB-branded email at 8.50am AEST. MailGuard has blocked 100% of these emails, and as both attacks are ongoing, we are monitoring for variants.
Details of the ATO phishing email:
The ATO-branded email about a tax refund from FY17 is well-timed, given the impending October 31 deadline for tax lodgments. It is in basic HTML format, and has two display and sending addresses: refund(at)ato.com and ato+zj4y9j69zss9-12O96F(at)ato.com. The sender is forging the domain ato.com, which is a legitimate domain owned by an industrial equipment vendor based in Chicago.
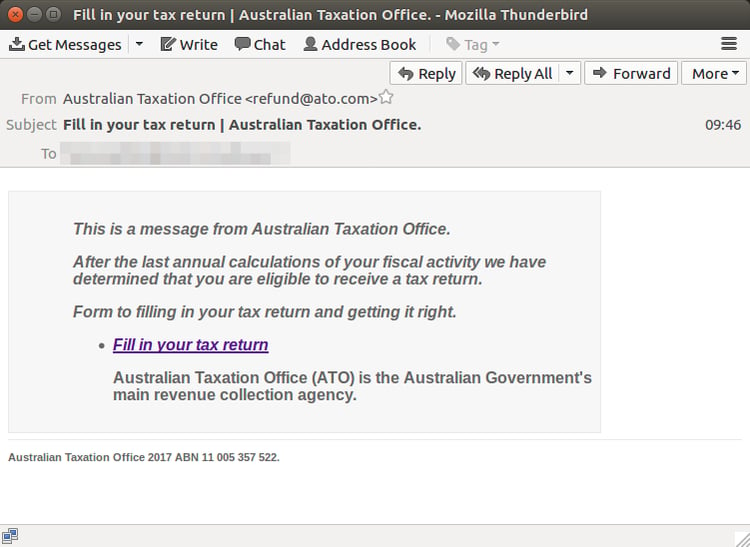
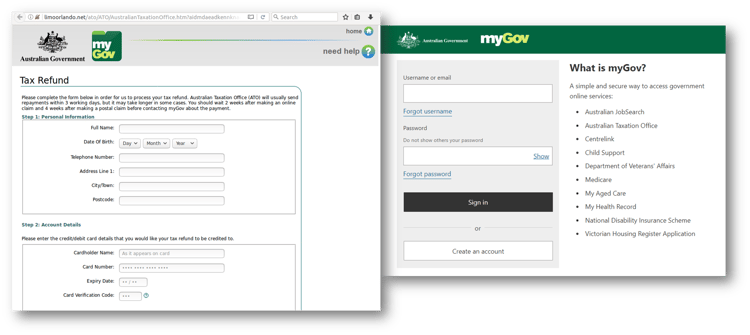
The link in the email is to a Google search result, linking to a website that redirects to a fake MyGov website on another host. The MyGov phishing site, which is a close imitation of the actual MyGov website branding, requests personal details including credit card details, driver's license, email and password. The phishing site is being hosted on a compromised host.
If the phishing form is submitted, it redirects to the legitimate ATO site, which is intended to assure users that they have just filled out a legitimate ATO form.
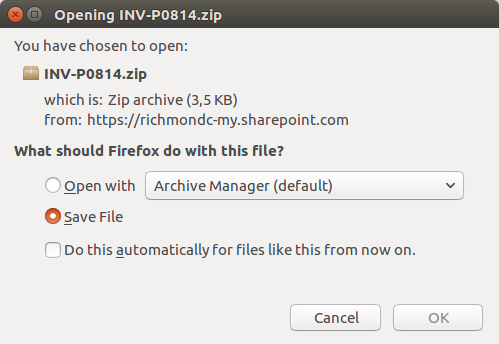
Details of the MYOB payload email:
The MYOB email directs to a compromised SharePoint site hosting a ZIP archive containing a malicious JavaScript file.
The well-formatted, HTML email informs recipients about a payable invoice, with the click-through to view the invoice. Cleverly, the issuing company name in both the subject line and the message body, and the amount due, varies between each email. Actual, ASX-listed company names are used.
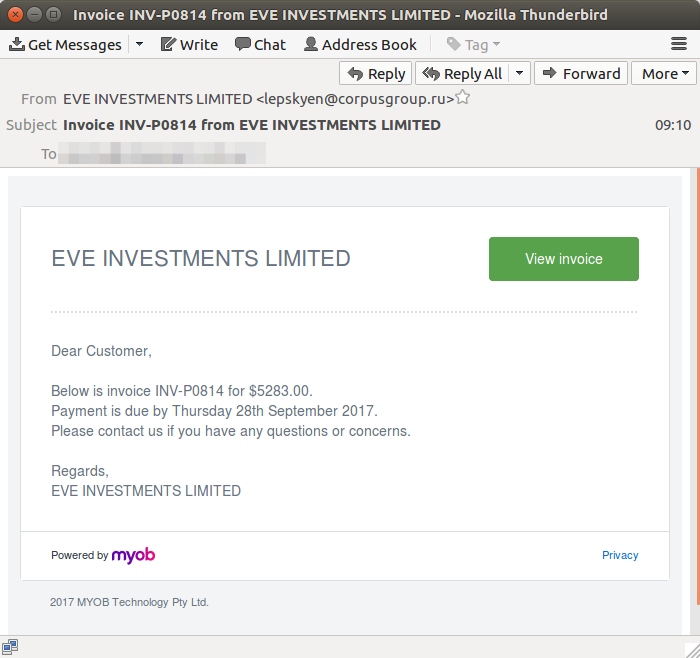
These are some of the subject line variances:
Subject: Invoice INV-P0814 from STREAM GROUP LIMITED
Subject: Invoice INV-P0814 from AFTERPAY TOUCH GROUP LIMITED
Subject: Invoice INV-P0814 from AIMS PROPERTY SECURITIES FUND
Subject: Invoice INV-P0814 from AUSTRALIA UNITED MINING LIMITED
Subject: Invoice INV-P0814 from LIFE CORPORATION LTD
Subject: Invoice INV-P0814 from REX MINERALS LIMITED
The display and sending address is a random address each time, with the email addresses presumably extracted from a previous data theft:
From: "PIONEER CREDIT LIMITED" <redacted@etfg.com.br>
From: "LIFESTYLE COMMUNITIES LIMITED" <redacted@jf-pontinhafamoes.pt>
From: "VELOCITY PROPERTY GROUP LIMITED" <redacted@rdd.lt>
From: "PRIMARY GOLD LIMITED" <redacted@lpcv.com.mx>
From: "ALTO METALS LIMITED" <redacted@tegiclogistique.com>
From: "AURIZON HOLDINGS LIMITED" <redacted@discoverymail.co.za>
Avoid being duped:
Be very suspicious of any emails that seem awry – either because of lack of customisations (e.g. a generic salutation), ill-timing (e.g. if you have not yet submitted your tax return) or if you are not expecting a correspondence from that particular organization.
The ATO has a response service for scams, and advises that the agency will never solicit personal details (such as Tax File Numbers, credit card details) and ask you to receive a refund, via email.
For a few dollars per staff member per month, add MailGuard's cloud-based email and web filtering to your business security. You’ll significantly reduce the risk of zero-day (previously unknown threats) and new variants of malicious email from entering your network.







