Another large scale run of fake ASIC emails was deployed yesterday. The first message was delivered at 08:46:21 AEST on the 23rd August, and purports to be an ABN registration renewal notification.
The email is seemingly legitimate, due to the professional formatting and grammatical accuracy.
The display and sending address are “ASIC Messaging Service” and asic.transaction.no-reply@australiangovernement.com respectively. The servers used to send the emails are located in France, and the domain was registered just a day before the phishing run.
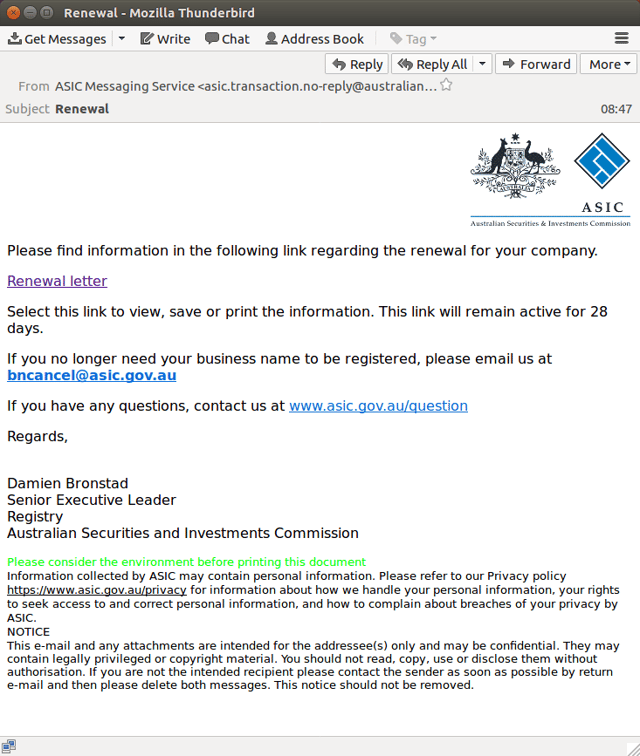
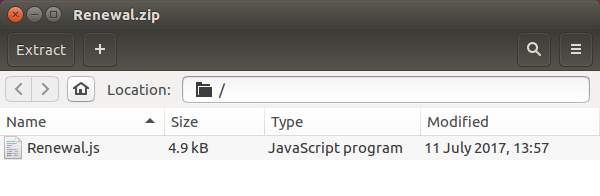
The notice does not ask for payment, but rather, a seemingly benign request to click a link to view, print or save the renewal letter. The link is to a ZIP file which contains malicious JavaScript payload.
As 94.7% of all websites use JavaScript, this scripting language presents a massive opportunity for cyber attackers. The insidious characteristic of a JavaScript payload, is that it doesn’t require user interaction to run.
The malicious payload is most likely a Javascript dropper, which downloads and deploys malware/trojans. To avoid detection, the Javascript code downloaded is usually obfuscated and not human readable. Some variants will also detect when executed in a sandbox environment and not action, thus making it harder to work out what it would do on a desktop environment. Often, they auto-delete after the malware installation.
Giveaways that this is a fraudulent email:
- The domain name – there is a misspelling of “government.” Australian government websites have the domain suffix / top level domain “.gov” (ASIC’s official domain is asic.gov.au).
- It is not personalised with the recipient’s details (business name, ABN, account number).
- The signatory, Damien Bronstad (based on a web search), is not an actual employee at ASIC.
ASIC, and other government departments such as the ATO and ACCC, and companies with large customer bases, are regular victims of brand jacking. This is the fifth ASIC branded email phishing scam detected by MailGuard this calendar year, off the back of a scam last month of unprecedented scale.
ASIC does send out email notifications 30 days prior to the renewal due date, however, their recommended payment method is via their online portal.
Our Operations team have determined that 100% of MailGuard's customers have been protected and are monitoring for variants.
For a few dollars per staff member per month, add MailGuard's cloud-based email and web security to your business security. You’ll significantly reduce the risk of new variants of malicious email from entering your network.







