As Easter approaches, you may be planning on enjoying a fun weekend with your family, but cybercriminals are likely hopping around trying to send new email scams your way.
Here at MailGuard, we’ve often seen a spike in online shopping related cyberattacks every time a public holiday approaches.
Just to put things in perspective - Aussie consumers reported over $2.7m in losses to online shopping scams in 2018 - and that’s just what’s been reported.
Here are a few examples of online scams that occur specifically during the Easter period, often exploiting cyber users’ holiday cheer and generosity:
-- Emails and Easter-themed ecards from unknown senders that may contain malicious links.
-- Fake advertisements or shipping email notifications with attachments infected with malware.
-- Spoofed email messages and phony posts on social networking sites requesting support for fraudulent Easter-related causes
(via Scamwatch)
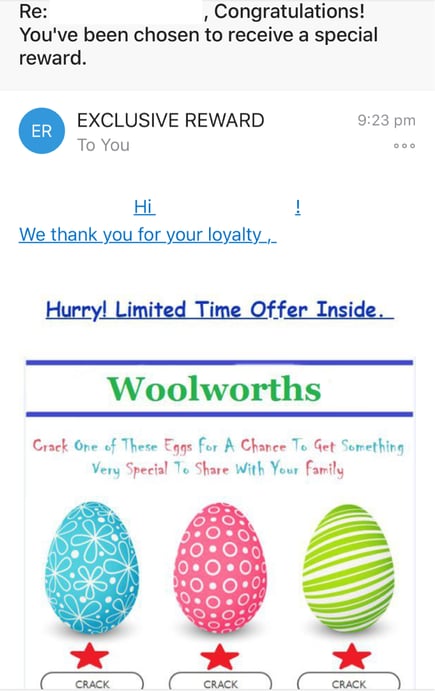
Here’s an example of an actual Easter-related scam email sent just last week:
And every year, we see these scams growing in frequency and complexity. To successfully confront this wave of cybercrime we often advocate a ‘defence-in-depth’ approach – which means using every resource available to us, because that’s exactly what cybercriminals are doing. A simple analogy for this would be what is often called ‘soccer goal security’. Imagine a soccer goalie actively defending one side of a goal, oblivious to the fact that his opponent was scoring on the other side of the goal. “The goalie is addressing the threat he expects,” says Richard Bejtlich, blogger at TaoSecurity, “The threat is smart and unpredictable, attacking a different part of the net.”
What this analogy means is that one type of defence simply isn’t enough – companies need a multi-layered strategy to boost their cybersecurity. All a malicious Easter promotion email requires is for one person to innocently click on it to bring a company to a standstill. Here’s a brief summary of what a multi-layered strategy entails:
Building physical, technical and administrative controls to combat cyberattacks when building a cybersecurity tech stack
Adopting this approach means developing a security tech stack that contains more than one layer of security, like some of these examples:
- Endpoint or Antivirus software
- Cloud Email Security and Advanced Threat Protection
- Archiving
- Biometrics
- Data-centric security
And so on.
The idea behind implementing multiple tools to defend your systems is the same as when you’re trying to defend your house from a break-in. You have locks on your doors, so why do you install deadlocks. In fact, a single deadlock is the absolute bare minimum layer of security home and business insurance providers often cite when providing insurance cover. A decent deadlock is only part of your security solution – many of us complement this with other alternatives like cameras, roller doors, grilles, motion detectors and padlocks, to avoid thieves making away with our valuables. So why not protect your company’s valuable data by implementing multi-layered security?
Let’s put this approach into the context of email security.
- For inbound email filtering
For many businesses, their main line of defence against spam is an on-premise antivirus solution. While this static, one-dimensional defence does offer significant protection, it also requires constant updates to remain effective against evolving cyber threats. Between updates, this single layer is vulnerable to brand-new threats, such as zero-day or fast-break malware.
To truly shut out these threats, best practice is to combine an on-premise antivirus solution and cloud-based email security solution from different security vendors. Using the same vendor for both would likely leave your business vulnerable to unknown viruses.
While most firms will have native security from their email hosting provider, like Google or Microsoft, since we know that 9 out of ten attacks start with an email, it’s also prudent to employ an additional layer of cloud email security with a solution like MailGuard that is a specialist at stopping advanced, zero-day threats.
Not even Google or Microsoft would claim that they can stop every threat, so just like with our home security, we should be adding another layer to protect against advanced email-borne threats.
That way, be it an Easter e-card with a malicious link, or an Easter gift invoice with a malicious attachment attacking your company’s inboxes – your systems are always secure.
- To ensure your password game is strong
Increasingly, hackers likely use a tactic known as password spraying, a technique that exploits weak passwords (the technique that led to the massive Citrix data breach last year). Ensuring your passwords are strong is one way to combat this, and the other is not re-using the same password for other accounts. This is dangerous because hackers who have obtained the password for your primary email account might be able to access other accounts linked to that email too (banking, shopping, secondary email accounts, etc).
An analogy explaining this involves a typical key bunch. Imagine if all your keys (to your car, your holiday home, your office) are all in a single bunch, and that bunch gets stolen. The thief will have access to all the keys, and the valuables protected by all of those keys. Therefore, to be safe, you could consider not bunching all your keys together and/or having a backup pair, so you still have access.
In the cyber world, this means not re-using the same passwords for different accounts. If passwords are even similar to used passwords, hackers may then be able to guess a new password from the leaked one. Take advantage of reputable services such as HaveIBeenPwned to see if emails and/or passwords have been compromised in any data breaches.
You can also use Multi-factor authentication (MFA) to protect your passwords making it harder for phishing scammers to hack into systems. When a user wants to login to an account they have to pass a second stage of authentication which commonly involves downloading an authenticator app on phones. It’s like having the front door key and then finding out that they don’t have the keypad code, or the key for the second deadlock. No doubt frustrating for the bad guys, and that’s what it’s all about. Again, having multiple layers of protection, this time for your passwords.
I’m sure there are other good analogies, like having airbags when you have perfectly good brakes in your car. Sure, the brakes will slow you down and bring you to a safe stop most of the time, but if they fail, or if the tyres fail to grip, you want the airbags ready to protect you when your car slams into a wall or heads down an embankment.
It’s age old wisdom, essentially embodied in the phrase we’ve all heard a thousand times, that it’s “better to be safe than sorry.” That same sentiment applies as much in the cyber realm as it does in the physical world.
So right before Easter hops around and email scams start multiplying like bunnies in your inbox, consider implementing a multi-layered defence to keep your data, people and other online valuables safely out of harm’s way.
Wishing you and your loved ones a cybersafe and happy Easter season.
Get the facts
Companies are spending more on cybersecurity now than ever before, but those funds aren't always targeting the most significant dangers. There seems to be a bit of a disconnect amongst many CEOs about the sources of cyber-threat.
Studies consistently show that more than 90% of cyber-attacks are perpetrated via email, yet email security is rarely the biggest item in cybersecurity budgets. If we’re going to win the battle against cybercrime we have to get real about the nature of the threat.
I’m on a mission to help business people understand cybercrime and protect their businesses from costly attacks. If you would like to learn more about the complex cybersecurity challenges facing business today, please download my e-book Surviving the Rise of Cybercrime. It’s a plain English, non-technical guide, explaining the most common threats and providing essential advice on managing risk.
You can download my e-book for free, here.
“Cybercrime is a serious and growing business risk. Building an effective cybersecurity culture within an organisation requires directors and executives to lead by example. Surviving the Rise of Cybercrime is a must-read for directors and executives across business and in government and provides strong foundations for leaders determined to address cyber risk.” - Rob Sloan, Cybersecurity Research Director, Wall Street Journal.
... ... ...
 Hi, I’m Craig McDonald; MailGuard CEO and cybersecurity author.
Hi, I’m Craig McDonald; MailGuard CEO and cybersecurity author.
Follow me on social media to keep up with the latest developments in cybersecurity; I'm active on LinkedIn and Twitter.
I’d really value your input and comments so please join the conversation.