Australians are being inundated by a huge spike in malicious email attacks coinciding with the end of financial year, led by a fresh batch of Origin Energy emails harbouring malware.
Hitting inboxes at a rate of nearly 10,000 an hour at its peak this morning, the fraud Origin email is highly realistic and installs malware at the click of a button. It perfectly mimics the branding and billing format of the popular energy provider.
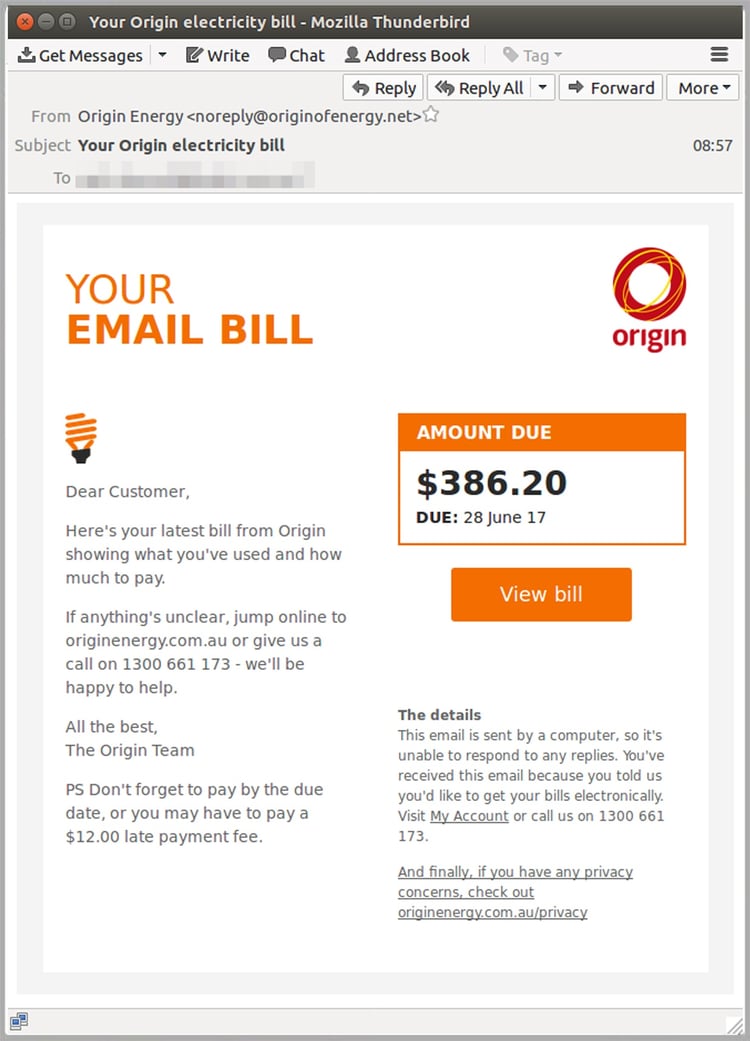
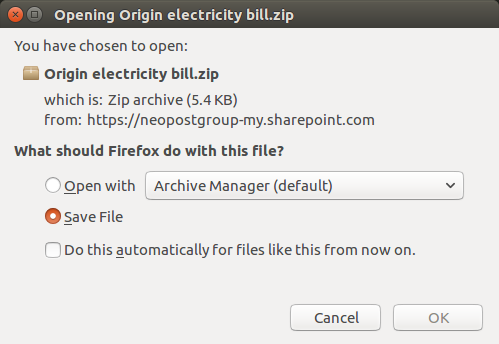
Those who click the ‘View bill’ link are at risk of malware infection. The link allows a JavaScript payload file to install itself to autorun, and attempts to steal private information from internet browsers.
These types of attacks tend to spike at traditionally busy times of year, such as Christmas, Easter and end of financial year as people are more likely to be time-poor and less likely to apply their usual scrutiny.
Details about the malicious Origin email
Subject line: Your Origin electricity bill
From address: noreply@originofenergy.net
Amount due: $386.20 in this example, but the amount varies from one email to the next
Due date: 28 June 2017
The well-formatted email has a generic ‘Dear customer’ greeting (this is a warning sign that it shouldn’t be trusted) and warns people not to forget to pay on time, or they’ll risk a $12 late payment fee.
The sending domain was set up yesterday with a registrar based in China.
Why MailGuard is first to alert the public about new targeted scams
Antivirus aggregator VirusTotal, owned by Google, indicates none of 65 commonly-used antivirus vendors are detecting the link as malicious.
Yet MailGuard blocked thousands of versions of the email before it hit any inboxes.
“Traditional antivirus providers are slow because they’re reliant on receiving copies of new threats, then writing and deploying fixes known as signatures. For these to work, customers’ antivirus software needs to install updates automatically or manually,” MailGuard CEO Craig McDonald explains.
“The time this takes creates a window of vulnerability, and exposes end-users to malicious content including malware and ransomware.
“To succeed against this new frontier of cybercrime you need to think differently. Our predictive, AI-led approach stops threats as they emerge – meaning we’re once again first to alert the market about new malicious emails flooding inboxes.
“This gives businesses extra protection from malicious content that can very easily be introduced to the work environment – for example by a curious staff member using a work computer to click a malicious link from a personal email account.
Inbox roulette
Contrary to popular belief, cybercrime doesn’t always mean complicated hacks and months of careful planning.
“Email is the new frontier for criminals capable of making money without leaving their house. They can fleece a person they’ve never met – from the other side of the globe.
“In fact, more than 90% of all cyber attacks begin with a single email. Usually it takes the form of phishing, where a scam-artists tricks their victim into handing over private information such as their log-in and password for online banking – as evidenced in this new iteration of the Origin scam.
Last month Origin was impersonated in a similar malware attack: That ‘Origin Energy’ bill is a scam. Whatever you do, don’t open the attachment. Further details here.
Tips from Origin Energy on detecting scams
Origin Energy says scammers often mimic legitimate companies to trick people into opening an email, clicking on a link or even making a payment.
“Some scam emails try to get you to click on links that launch nasty viruses, ready to invade your computer, and the computer of everyone you email, to delete or lock your files.”
The company recommends seeking advice from www.scamwatch.gov.au or www.staysmartonline.gov.au if you think you’ve been scammed.
Every minute counts. Talk to an expert at MailGuard about protecting your business today







