Cybercrime networks are once again sending email scams purporting to come from popular telecommunications company, Optus. MailGuard detected several such malicious emails throughout the day on Tuesday.
The scam appears in several different variations, all using the domain ‘optusnet.com.au’. All variations are designed to result in the same goal, tricking the recipient into running a malicious .vbs file. Below are 2 examples of this payload email scam.
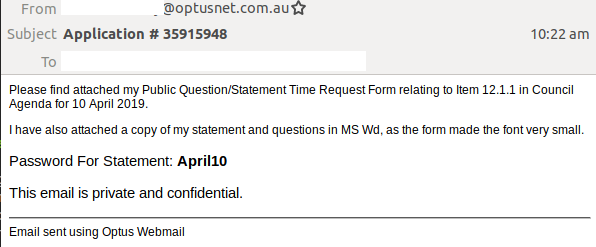
The first example of the scam advises the recipient that their 'Public Question/Statement Time Request Form' is attached. Appearing in plain-text format, the email body claims the copy is attached as a 'MS Wd' as the form made the font very small. The attachment is a ZIP archive, which is password protected. The message body includes the password to access the archive. Inside this ZIP archive is a malicious VBS file.
Here is the screenshot of this example:
The subject of the second example states that the email is for a Federal Police check and asks the recipient to review it. Within the body, the recipient is advised that their application is attached. However, no attachments accompany the email. Instead, the words 'attached application' and 'your application' are linked to a .zip file download, which contains a malicious .vbs file. Below is a screenshot of the email:
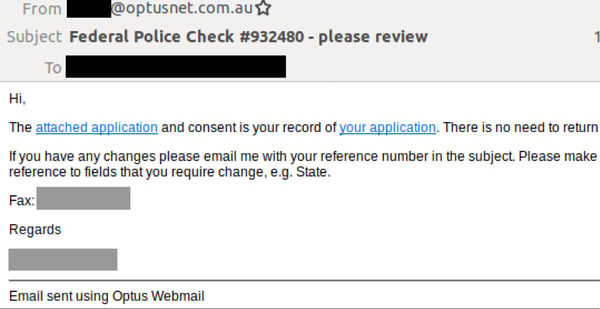
MailGuard found both the above malicious emails come from what appear to be compromised ‘optusnet.com.au’ accounts.
While the plain-text nature of both emails and the fact that the recipient isn’t addressed directly are strong indicators that these emails are malicious, the email scam does employ several elements to convey legitimacy and a false sense of security.
This includes the use of a password in the first example to access the archive. This not only boosts the legitimacy of the email, but also makes it harder for email filtering services to access the payload directly. Hence, it is less likely that the email will be classified as a scam.
MailGuard urges all cyber users to be vigilant when accessing their emails, and look out for tell-tale signs of malicious emails.
Tell-tale signs of email scams
- Do not address recipients directly (e.g. “Dear customer”)
- Bad grammar or misuse of punctuation and poor-quality or distorted graphics
- An instruction to click a link to perform an action (hover over them to see where you’re really being directed)
- Obscure sending addresses (for example, Hotmail, gmail, Yahoo addresses should set alarms bells ringing)
Don't get scammed
If your company’s email accounts aren’t protected, emails like the one above are almost certainly being received by your staff. Cybercriminals know people can be tricked; that’s why they send out millions of scam messages and put so much effort into making them look convincing.
People are not machines; we're all capable of making bad judgement calls. Without email filtering protecting your business, it’s just a matter of time before someone in your organisation has a momentary lapse of judgement and clicks on the wrong thing.
For a few dollars per staff member per month, add MailGuard's cloud-based email and web filtering solution to your business security. You’ll significantly reduce the risk of new variants of malicious email from entering your network. Talk to an expert at MailGuard today about your company's cybersecurity needs: expert@mailguard.com.au
Keep up to date on the latest email scams by subscribing to MailGuard’s weekly update, or follow us on Twitter @MailGuard.







