Scammers have set up a near-perfect clone of the myGov website in order to dupe victims into sharing their password and credit card details.
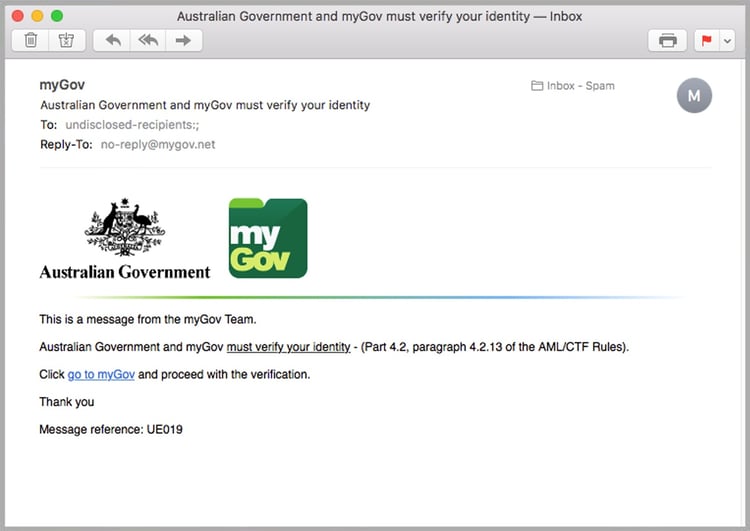
The sophisticated rouse starts with a credible-looking phishing email from the Australian Government portal my.Gov.au, which tells recipients they must go to the website to verify their identity.
 Those who click the link directing them to the website are taken to a replica of the real site. Note the strange URL which is an indication the website is not a legitimate Australian Government domain.
Those who click the link directing them to the website are taken to a replica of the real site. Note the strange URL which is an indication the website is not a legitimate Australian Government domain.

There, the cybercriminals behind the scam attempt to harvest their account details.
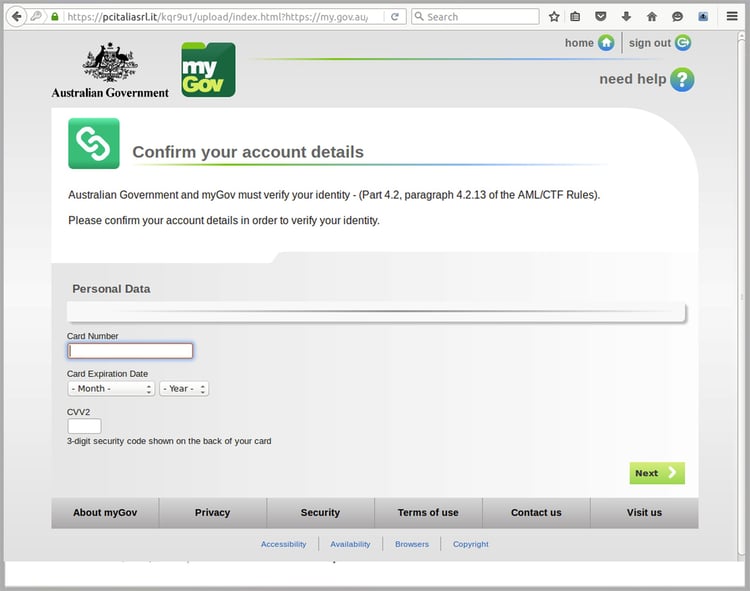
Experts from the MailGuard email security team compared the source code of the fake site and discovered it’s cloned directly from the real government website.
After victims input their credit card details and click ‘Next’, they are directed to the real myGov website. This is an attempt to hide the deception from victims.

The phishing email was distributed on a surprisingly small scale given the complexity of the scam.
But it poses a large risk. With more than 11 million accounts, and visitors accessing information from agencies including the Australian Taxation Office, Medicare and Centrelink, there’s a high chance the recipients of the phishing email have a myGov account.
The email originates from servers hosted in the Czech Republic, which are likely to have been compromised. The sending address used is noreply@mygov.net, which has no relationship with the legitimate portal.
The fake domain, mygov.net, has no SPF (Sender Policy Framework) records, meaning it can be easily forged. An SPF record is a method of protection against spammers as it identifies which mail servers are permitted to send on behalf of a domain.
It’s not the first time myGov has been targeted by cybercriminals.
In February Stay Smart Online advised Australians to delete fake emails purporting to be from the government.
“You are advised not to click any links in the scam email as these direct you to forms designed to capture personally identifying information such as photocopies of passports and drivers' licences, as well as your bank account details.
“These fake forms and pages feature myGov design and branding, making them appear legitimate. They may even provide you with a one-time PIN as part of the process of capturing your account details.”
The email and web security experts at MailGuard recommend these steps for avoiding being tricked by a fraud email:
- Check who it was sent by. Examine the sender or reply-to address and check that it hasn’t been sent from a similar, but recently-registered domain such as mailguard.com instead of mailguard.com.au
- Beware of links in emails. Before you click anything, take a closer look by hovering your mouse over and checking the destination in your browser. If it doesn’t match, it is not legitimate.
- Be aware that a reputable company or organisation will never use an email to request personal information. If you think there is a possibility it may be legitimate, type the real URL into your browser or contact the company directly.
- Be alert for strange sentence structure, or phrasing uncommon to the apparent sender
- Ensure your email security is up to scratch. A cloud-based, AI-based threat detection service such as MailGuard will protect your staff in real-time from targeted attacks, without the dangerous time-lag common with signature-based antivirus vendors.
Click here to download your free executive guide, Surviving the Rise of Cybercrime, by MailGuard CEO and founder Craig McDonald.
Keep up to date on the latest email scams by subscribing to MailGuard’s weekly update, or follow us on Twitter @MailGuard.







