Cybercrime for good – it seems like an oxymoron, yet it’s surprisingly common. Sometimes referred to as hacktivism, socially or politically motivated cyberattacks are not a novel concept.
The first explicitly politically motivated case of hacking occurred in 1989 when computers at the U.S. Energy Department and NASA were attacked by anti-nuclear protesters titled WANK (Worms Against Nuclear Killers). Generally targeting government agencies or multinational corporations, the hacktivism movement has grown tremendously since the 80’s, reaching its peak around a decade ago.
For many, the term hacktivism is synonymous with the group Anonymous, which is comprised of “working class people seeking a better future for humanity”. It has carried out attacks for close to two decades. Some of their most infamous attacks have been against the Church of Scientology, Sony, and governments around the globe, with the Russian Federation being their current target following their invasion of Ukraine.
However, it’s recently become apparent that hacktivism is progressing beyond attacks on corporate or governing bodies, with one group in particular targeting everyday people.
GoodWill Ransomware
In March 2022, a new ransomware strain was found in India which was titled “GoodWill”. While this particular strain works the same as others, by encrypting files until a ransom is paid for a decryption key, there is one major difference – the hackers weren’t asking for financial payment from their victims. Instead, as the name suggests, they request that the victim complete three pre-specified charitable acts.
When the victim’s device is infected with the ransomware, they’re shown a message that states:
“We want to make every person on the planet to be kind and wants to give them a hard lesson to always help poor and needy people…
Take Deep breath and look all around for those who need help? You! No way, the only way to help yourself is to help others.”
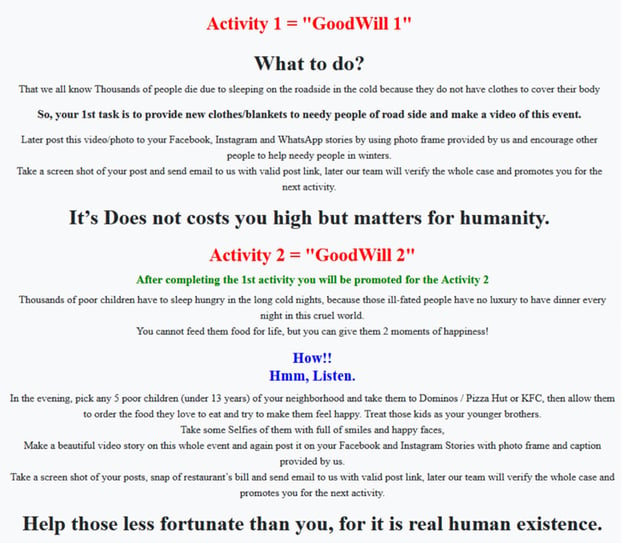
The victim is then instructed to carry out each of the below good will acts, making sure to record each one as evidence, share to social media with a frame and caption provided by the hackers, and send it through to the attackers.
- Provide new clothes/blankets to people in need
The task specifies that these items should be provided to “needy people of roadside”, to help them through the winter.
- Take 5 underprivileged children out for dinner
These children are required to be from the victim’s neighbourhood, under 13, and taken to either Dominos, Pizza Hut or KFC. The attack encourages the victim to “treat those kids as your younger brothers”. - Pay for someone’s medical treatment
The victim is instructed to go to a hospital, find someone who urgently needs money, and offer to pay on their behalf.
While the act may be well intended, it still leaves a sour taste in my mouth. Turning to my LinkedIn network, I posed the question, “Does committing cybercrime for good outweigh the criminal aspect?”.
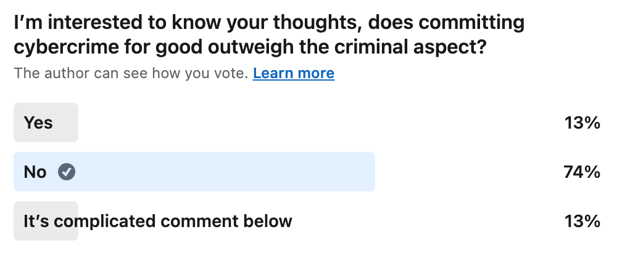
- 13% of respondents voted for ‘Yes’,
- A large majority of replies (74%) voted for ‘No’,
- And 13% agree with the statement ‘It’s complicated’
The results were somewhat more divided than I had initially expected, although it is a complicated issue with no clearcut answer.
On the surface, I can understand why some feel that hacktivism in general is more beneficial for society than damaging. However, the end does not always justify the means. Infecting devices with ransomware is still a criminal act. Forcing good will does not negate the bad act.
Who determines what is right and wrong, and therefore which acts and/or people are most worthy? It is a very slippery slope.
Moreover, can we be certain that there are no unforeseen consequences? In this particular instance, unless each attack is carefully targeted, there’s no telling if the victim themselves can afford new clothes, a warm dinner, or hospital bills. And beyond the immediate target, if others were not unwittingly impacted, like employees or others in their supply chain if a small organisation’s systems are impacted. Is an individual’s hospital visit affordable for the victim? Were those funds necessary for schooling or healthcare for the victim or their family? What other costs, either time or money, are there for the business while the victim is left carrying out these acts to receive a decryption key?
As one commenter on Reddit put it, the group behind GoodWill are essentially asking the victim to "steal from those barely above water and give to the drowning".
Put simply, this is no more than extortion, and no individual or group has the right, however well intended, to arbitrarily target others and to force them to commit acts against their will.
Fortunately, there are presently no known victims of the ransomware. The concern is that others may soon follow in the GoodWill group’s footsteps, and who is to say which groups they may target, what their demands may be, and who the victims will be.
I’m keen to open up the conversation on this topic and would love to know your thoughts, please don't hesitate to reach out to us to discuss further.
Talk to us
Talk to a MailGuard solution consultant today about securing your company's inboxes. You can get in touch with us by calling +61 3 9694 4444, or by emailing us at info@mailguard.com.au.
Existing MailGuard partners and clients can reach out to us here:
Australia - please call us on 1300 30 65 10
US - call 1888 848 2822
UK - call 0 800 404 8993






