A new threat purporting to be from Amazon Web Services (AWS) is targeting IT professionals, with a new phishing email designed to trick technical staff into handing over account and credit card details to cyber criminals.
The email appears to be from AWS with the subject line ‘Please confirm your amazon account.’ The email is branded with the Amazon logo instead of the AWS logo, and is not personally addressed to the email recipient.
To convince email recipients to take action, cyber criminals try to scare recipients into thinking their account has been suspended, asking for payment details to be updated in order to reactivate the account.
Here is a sample of the phishing email purporting to be from AWS:
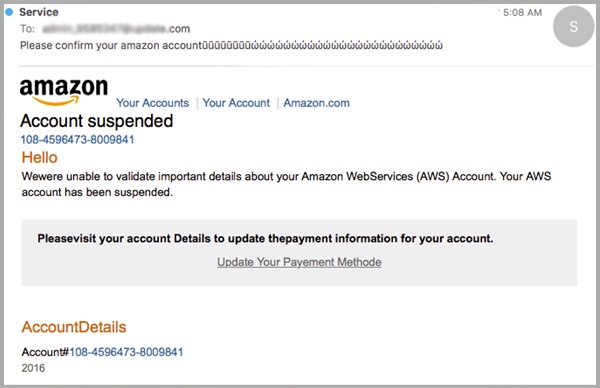
Hovering over the link where it says ‘Update Your Payement Methode’ [sic], you can see that the URL points to a compromised website (todieforclothing.com) and not that of the legitimate AWS website (https://aws.amazon.com/).
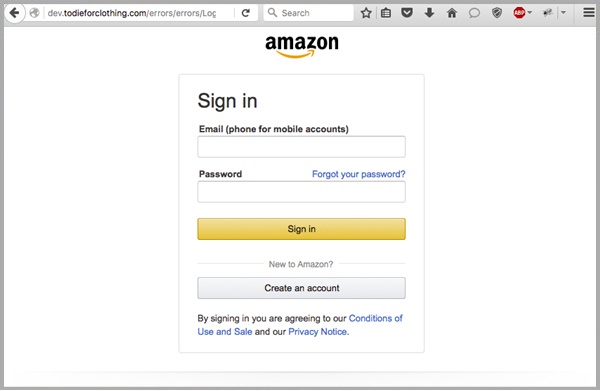
The compromised website landing page is a replica of the Amazon sign in page. By continuing to ‘Sign in’ to the Amazon account, the user is handing over their account access details to the cyber criminals.
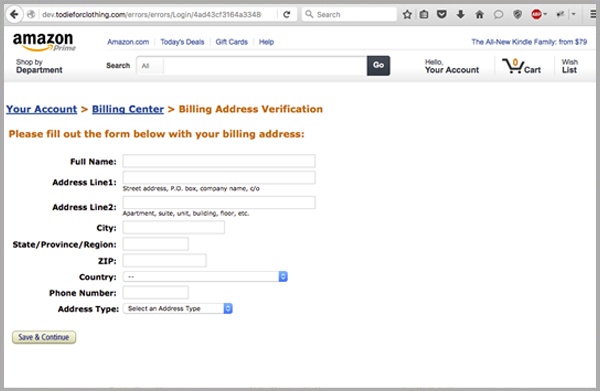
Upon clicking ‘Sign in’, users are directed to another fake landing page asking for billing details.
The last part of this scam asks the recipient to enter their credit card details, bank account number and date of birth.
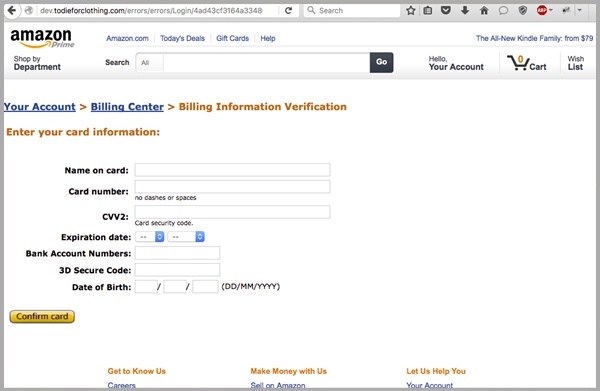
Hitting ‘Confirm Card’, recipients are redirected to an actual Amazon thank you page, making the user feel as if the process was legitimate and required by Amazon themselves.
To reduce the risk of being tricked by one of these scams, you should immediately report and delete any emails that:
- Appear to be from a well-known organisation, typically a bank or service provider and are not addressed to you by name and/or may include poor grammar.
- Ask you to click on a link within the email body in order to access their website. If unsure call the company directly and ask whether the email is legitimate
- Offer money, reward or gift to entice you to hand over your personal details
- Ask you to submit personal information that the sender should already have access to or should not be requesting from you in the first place
Amazon ask users to report phishing or spoofed emails via their website.
We recommend that you share these tips with your staff to make them aware of these campaigns.
By employing a cloud-based email and web filtering solution like MailGuard, you’ll also reduce the risk of these new variants of phishing from entering your network in the first place.
Our benchmarking shows that MailGuard is consistently between 2 hours and 48 hours ahead of the market in preventing new attacks.
At the time of writing, only 1 out of 67 vendors are currently flagging this content as malicious.
Keep up to date on the latest email scams by subscribing to MailGuard’s weekly update or follow us on social media.






