The attacks can take many names, from CEO Fraud, to Whaling and Business Email Compromise. Whichever name you choose, spear phishing attacks impersonating influential executives continue to be a big problem for businesses of all sizes.
MailGuard intercepts spear phishing attacks every day, however these attacks rarely go reported due to their highly targeted and personal nature. Typically, they will only represent a handful of interactions within an individual organisation, with the cybercriminals attempting to execute their crime at speed. The emails are simple and plain text, with no payloads or links, so they can by-pass most antivirus solutions.
Before the first email is sent, the cybercrime network behind the attack will conduct thorough reconnaissance to research the targeted organisation and the individual executives involved. With carefully socially engineered attacks, often much of the information that the attackers require is easily available from company websites and social networks like LinkedIn. The scammers are able to understand the contact details, location and role titles of executives and employees, as well as researching the victims network within the target organisation. Depending on the profile of the executives involved, it may be possible to determine if they will be offsite at business roundtables, conferences or other speaking engagements, creating a window for opportunistic scammers.
This means with the benefit of a small amount of research, and minimal investment of time and money, the attackers can develop a tailored campaign with a high degree of confidence.
The emails below are real, however we have screened the names to protect the identities involved. The target in this example is an ASX listed Mining & Resources company, and the email is coming from the Managing Director.
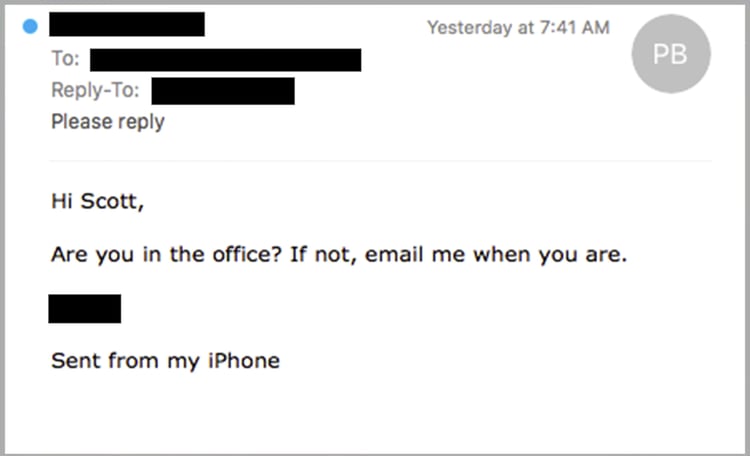
It’s a very casual, simple first approach, attempting to determine if the individual required to make the transfer is at his desk. It’s from the mobile phone (iPhone) of the Managing Director, so it is likely to capture his attention. It is also early in the morning, 7:40am, so there’s a good chance there aren’t many people around to verify that the request is legitimate.
Here’s another example. This time it purports to be from the CEO of a large financial services business. It’s shortly before lunch, and makes it quite clear that he is seeking to converse over email only. Nonetheless, it is quite casual and personal in nature.
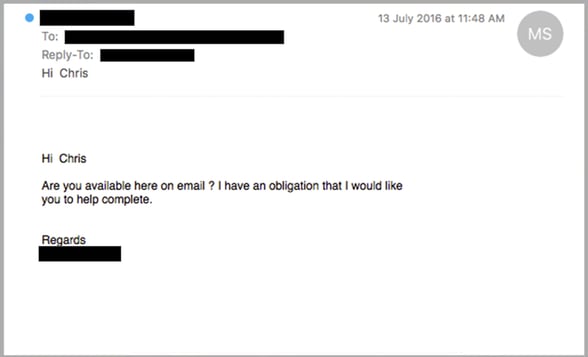
In each of these examples, there is no mention of a funds transfer. The initial contact is simply trying to establish a dialogue and determine if the target is at his or her desk. These are the more patient attacks.
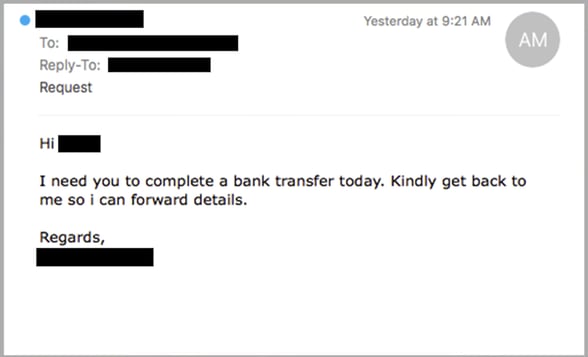
In some cases, as in the email below, the first contact will in fact also establish that a funds transfer is needed. Still a simple and personable email, the attacker is trying to establish a connection and without causing alarm, to ensure that the target knows that this is a time critical task that must be completed today.
How would your team respond to a personal request from the Managing Director, CEO or other senior executives in the business?
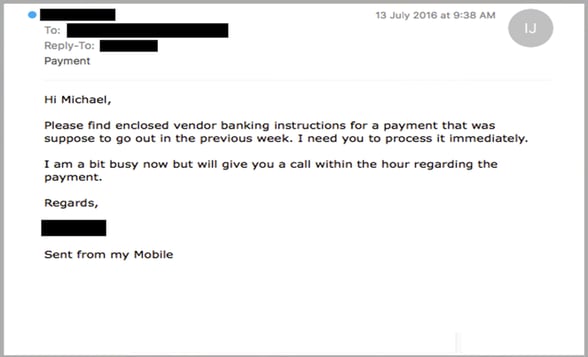
Having established connection, the following example purported to be from another Managing Director in yet another ASX listed business, provides details for the payment and makes clear that the payment is overdue so there is some urgency.
Please complete this task immediately and I will be available to speak with you about it in an hour. Again the request is coming from the mobile phone of the MD, making clear that he is not in the office so there is no point trying to speak with him in person.
You can see how simple these scams are, yet they are extremely effective. With little time and cost invested, a cybercrime network can easily assume the identity of a high profile executive and pressure employees within the business to make a payment.
As simple as they may seem, these attacks are happening all too regularly, and with devastating effect. Not only can they inflict significant financial damage on an organisation, but they can also take an enormous emotional toll on the individuals concerned, and they are likely to have serious career consequences as well.
A leading email and web filtering solution like MailGuard is an excellent first step. In addition, this is a timely reminder to ensure that appropriate training and education is in place to ensure that all of your employees know how to respond to such requests. In addition, have effective processes agreed to prevent individuals from making erroneous funds transfers without the necessary checks and balances.
Keep up to date on the latest email scams by subscribing to MailGuard’s weekly update or follow us on social media.
If you’re experiencing problems, you can speak to a cloud security specialist on 1300 30 44 30 or email expert@mailguard.com.au.







